SIMPLY CYBER CON 2025
Agenda
9:00: Welcome!
What today is all about
Today’s training is about taking the value you can deliver to a cybersecurity program, to the next level.
From junior to senior levels, if you sharpen and dial in your ability to apply these concepts, it’s going to remove barriers, for your organizations cybersecurity program, and your carrer
I’m a case study that has lived and experienced this
Here’s what Dr. Gerald Auger has to say:
Here’s more on how Risk Management skills and NIST Cybersecurity Framework remove barriers for your career path and your ability to communicate effectively about risk:
Risk Professional Skills: Mastering Cyber Resilience
Students develop a comprehensive foundation in the NIST Cybersecurity Framework (CSF) and learn to implement and optimize it across organizations of any size. Working from that strong foundation, they develop practitioner competencies, getting ready to lead cybersecurity teams or work as independent consultants.
Target Audience: No prerequisites required. Ideal for professionals making entry-level or mid-career transitions into cybersecurity GRC, as well as current IT professionals, security analysts, and managers seeking to advance their cybersecurity leadership capabilities.
Gain the necessary skills, methods and mindset to help an organization achieve cyber resilience and safeguard critical digital assets confidently.
What You'll Be Able to Do
Lead comprehensive cybersecurity risk assessments
Present risk findings and recommendations to executive leadership
Develop organizational cybersecurity implementation roadmaps
Create and manage cybersecurity action plans aligned with business objectives
Guide organizations through cybersecurity maturity improvements
CYBER RESILIENCE FUNDAMENTALS
DOMAIN 1 - Cybersecurity Framework Concepts: Understanding the basics
DOMAIN 2 - Framework Core: Six functions (Govern, Identify, Protect, Detect, Respond, Recover) drilling down into 22 categories and 106 subcategories. These enable effective communication about cyber risk between executives, managers, and practitioners
DOMAIN 3 - CSF Tiers: Determining the level of security based on your organization's unique mission, risk tolerance, and resources. CSF is not prescriptive and not one-size-fits-all. It is flexible and scalable
DOMAIN 4 - CSF Profiles: Strategic planning between current and desired states to align cybersecurity efforts with organizational goals
DOMAIN 5 - Risk Management: To reliably achieve objectives
CYBER RESILIENCE PRACTITIONER
DOMAIN 1 - Management Action Plan Fundamentals: Prepare for assessments, comprehend a management action plan process, achieve management buy-in, and understand the relationship between NIST Cybersecurity Framework and a management action plan process
DOMAIN 2 - Determine Top Cyber Risks: Identify, understand, assess, and present cyber risks using interviews, network diagrams, and custom questionnaires while setting NIST CSF alignment targets
DOMAIN 3 - Creating a Management Action Plan: Evaluate and rate risk mitigation, create custom strategies, estimate costs, and develop an implementation roadmap for an organization
DOMAIN 4 - Maintenance and Updates: Guide organizational leadership in allocating risk mitigation strategies, updating risk presentations, clarifying proposed measures, and conducting ongoing cybersecurity resilience review
CERTIFICATION PREP
This course is based on the Mastering Cyber Resilience textbook by AKYLADE. In addition to developing valuable competencies you can apply in the field, it prepares you for the AKYLADE Certified Cyber Resilience Fundamentals (A/CCRF) and AKYLADE Certified Cyber Resilience Practitioner (A/CCRP) certification exams. These industry-recognized certifications validate your expertise in cybersecurity framework implementation and risk management, enhancing your career advancement opportunities.
COMES WITH
Mastering Cyber Resilience Textbook
Authorized Training Provider 20% discount on AKYLADE certification exams
Access to recordings and resources for the online versions of these courses in Simply Cyber Academy
SYSTEM REQUIREMENTS
There are no system prerequisites for the course. Lab demonstrations will include the following applications: Microsoft Excel, Visual Studio Code, Claude and ChatGPT.
About your instructor, Steve McMichael

Steve is passionate about guiding professionals from technical and non-technical backgrounds into cybersecurity GRC. He successfully made this shift himself and shares his transition insights in the popular blog, CPA to Cybersecurity.
Steve holds advanced degrees in business (BBA, MBA), along with top cybersecurity certifications (CCRP, CRMP, CISSP, CISA), and is a Chartered Professional Accountant (CPA). With nearly 20 years of experience spanning business continuity, financial auditing and cybersecurity leadership, he currently serves as the Director of Governance, Risk, and Compliance at BlackBerry.
Introductions
Round table:
Your thumbnail sketch introduction
What are you hoping to get out of this course?
Are there any specific challenges on the job that you want to apply skills or methods from this training to?
If you’ve seen the on-line course lesson outlines, are any any lectures or topics of particular interest (I’ll ask again later if you haven’t seen them yet)
9:15 Course Materials
Online Lectures
Your 100% discount code to unlock: SIMPLYCYBERCON2025
Your Mastering Cyber Resilience Textbook
Email sent last night (check junk folder):
Subject: Invitation to Join Simply Cyber Academy from AKYLADE®
From: [email protected]
Dear [Your Name Here],
We’re excited to invite you to join Simply Cyber Academy, an AKYLADE Authorized Training Partner group, through the AKYLADE Member Portal.
Here are the details you’ll need to get started:
Status: PENDING
Invitation Code: [Your Code Here]
Expires At: 2025-11-16T10:20:27.355Z
To accept this invitation, visit https://members.akylade.com/atp-invites , click “Accept ATP Invite Code” and enter the invitation code provided above.
If you have any questions or need assistance with the AKYLADE member portal, feel free to reach out to us at [email protected]. If you have any questions about your training, please do not hesitate to contact your Authorized Training Partner directly at [email protected]. We’re here to help!
We look forward to welcoming you to the Simply Cyber Academy group and supporting you on your educational journey with AKYLADE where we bridge the gap between learning and doing.
Best regards,
Alyson Laderman
Chief Executive Officer AKYLADE®
Your invitation code:
I emailed it to you this morning from [email protected] (here’s a private link for my reference).
Quick Reference and BCP if Internet Issues Today
— AKYLADE Certified Cyber Resilience Fundamentals (A/CCRF) —
FOUNDATIONS & FRAMEWORK BASICS (9:30-10:25 AM)
9:30-9:40 | Ch 2: Cybersecurity Fundamentals
FOCUS: CIANA Pentagon, Risk = Threat × Vulnerability formula
QUICK COVERAGE: Terms definitions
9:40-9:55 | Ch 3: Risk Management Fundamentals
FOCUS:
Risk Management Lifecycle phases
Quantitative vs Qualitative analysis
4 Risk Responses: Accept/Avoid/Transfer/Mitigate
QUICK COVERAGE: BIA terms, Financial metrics
9:40-9:55 | Ch 3: Risk Management Fundamentals
FOCUS:
Risk Management Lifecycle phases
Quantitative vs Qualitative analysis
4 Risk Responses: Accept/Avoid/Transfer/Mitigate
QUICK COVERAGE: BIA terms, Financial metrics
9:55-10:10 | Ch 4: NIST CSF Overview
FOCUS:
Executive Orders & development history
Voluntary, flexible, risk-focused nature
Applicability across sectors
QUICK COVERAGE: Regulations, cyber resilience definition
10:10-10:25 | Ch 5: Framework Components
FOCUS:
Three pillars: Core, Tiers, Profiles
4 Implementation Tiers overview
QUICK COVERAGE: Current vs Target profiles
10:25-10:30 | Quick Break
THE FRAMEWORK CORE (10:30-11:15 AM)
10:30-11:00 | Ch 6: Six Functions Deep Dive
11:00-11:07 | Ch 7: Controls vs Outcomes
FOCUS:
Outcomes-based approach vs prescriptive controls
Informative References overview
11:07-11:15 | Ch 8: Implementation Tiers
FOCUS:
Tier 1-4 characteristics
NOT maturity levels - emphasize this distinction
Moving between tiers: 5-step process
PROFILES, RISK & WRAP-UP (11:15 AM-12:00 PM)
11:15-11:25 | Ch 9: Profiles
FOCUS:
Creating profiles: 6-step process
Current vs Target profiles
Sector-specific examples
11:25-11:35 | Ch 10: Assessing Cybersecurity Risk
FOCUS:
Case study: AKYLADE Learning Company
Risk assessment process: Threats → Vulnerabilities → Risks → Mitigations
Risk management plan & cybersecurity strategy
11:35-12:00 Practice Exam Questions
Domain weightings review:
Domain 1: 25% (Framework Concepts)
Domain 2: 30% (Framework Core) - MOST IMPORTANT
Domain 3: 10% (Implementation Tiers)
Domain 4: 15% (Framework Profiles)
Domain 5: 20% (Risk Management)
Key relationships between components
Test-taking strategies
12:00 LUNCH
— AKYLADE Certified Cyber Resilience Practitioner (A/CCRP) —
Domain 1: 20% (CR-MAP Fundamentals)
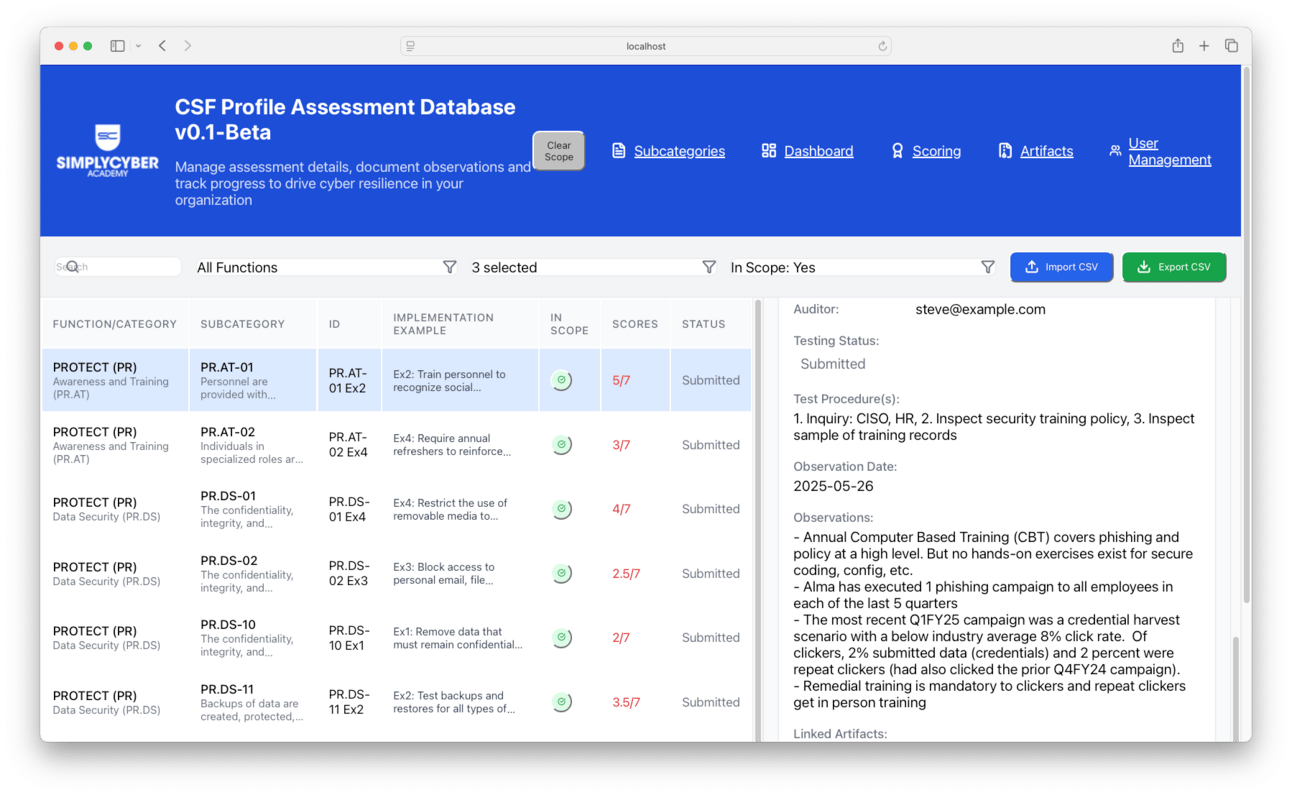
1:00-1:45 CSF Profile Assessment Lab
FOCUS:
Hands-on profile creation exercise
Current vs Target state assessment
1:45-2:00 PM | Ch 11: CR-MAP Fundamentals
FOCUS:
CR-MAP 3-phase process
The Five Essential Questions
NIST CSF to CR-MAP relationship
QUICK COVERAGE:
Expeditors case
Domain 2: 36% (CR-MAP Phase One: Determining Top Cyber Risks)
2:00-2:10 PM | Ch 12A: Preparation & Stakeholders
FOCUS:
Widen Your Scope beyond IT
Get Buy-In strategies
Interviewee selection ratios
QUICK COVERAGE:
C-suite email template
2:10-2:20 PM | Ch 12B: Creating Questionnaires
FOCUS:
Aligning questions with NIST CSF
Target score setting (5 approaches)
Risk-to-Cost-of-Controls curve
QUICK COVERAGE:
FTC Safeguards Rule
2:20-2:25 PM | Ch 12C: Spreadsheet Lab
FOCUS:
XLOOKUP demonstration
Pivot Tables for analysis
2:25-2:40 PM | Ch 12D-E: Conducting Assessments
FOCUS:
Interview best practices
Compiling and averaging scores
Identifying Top 5 Cyber Risks
Managing "junk data"
QUICK COVERAGE:
Communication methods ranking
2:40-2:50 PM | BREAK
Domain 3: 27% (CR-MAP Phase Two: Create a CR-MAP)
2:50-3:05 PM | Ch 13A: Phase 2 Introduction
FOCUS:
Responsible disclosure importance
ASUS vs Home Depot case comparisons
Keys to success in Phase 2
KISS Principle
QUICK COVERAGE:
Detailed case studies
3:05-3:20 PM | Ch 13B: Supply Chain Risk
FOCUS:
Shared responsibility model
Information Security Addendum template
SC-01, SC-05, SC-07 implementation DELIVERABLE: Template for vendor contracts
3:20-3:35 PM | Ch 13C: Core Security Controls
FOCUS:
PR.DS (Data protection in transit/at rest)
PR.AA (Identity & Access Management)
PR.AT (Awareness & Training)
RS.CO (Incident communication)
QUICK COVERAGE:
Encryption
3:35-3:50 PM | Ch 13D: Business Value & 3TCO
FOCUS:
3TCO formula and calculation
Four dimensions of business value
In-house vs outsource framework
Six example cost scenarios DELIVERABLE: Pre-calculated TCO examples
3:50-4:05 PM | Ch 13E: Communication Strategy
FOCUS:
Internal marketing (Force Field Analysis)
External marketing (Summary Scorecard)
Dashboard and roadmap creation
Stakeholder analysis matrix
QUICK COVERAGE:
NDA requirements
Domain 4: 17% (CR-MAP Phase Three: Maintenance and Updates)
4:05-4:25 PM | Ch 14: Maintenance & Updates
FOCUS:
Equifax breach lessons
Four maintenance steps structure
Monthly check-ins (60 min format)
Quarterly reviews (90 min format)
Annual summit planning
QUICK COVERAGE:
AI augmentation
4:25-4:50 PM | Practice Exam Questions
Domain 1: 20% (CR-MAP Fundamentals)
Domain 2: 36% (CR-MAP Phase One: Determining Top Cyber Risks) - MOST IMPORTANT
Domain 3: 27% (CR-MAP Phase Two: Create a CR-MAP)
Domain 4: 17% (CR-MAP Phase Three: Maintenance and Updates)
4:50-5:00 PM | Wrap-up Q&A
FOCUS:
Key takeaways
Q&A