Table of Contents
13.1 Introduction & Exam Objectives
📚️ Exam Objectives

13.2 ASUS Responsible Disclosure Case Study (2016)
🧭 Phase 2: Creating a CR-MAP
ASUS marketed its routers as including numerous security features that the company claimed could “protect computers from any unauthorized access, hacking, and virus attacks” and “protect [the] local network against attacks from hackers.” Despite these claims, the FTC's complaint alleges that ASUS didn’t take reasonable steps to secure the software on its routers
Hackers used readily available tools to locate vulnerable ASUS routers and exploited these security flaws to gain unauthorized access to over 12,900 consumers’ connected storage devices.

Failure Points:
Hid vulnerabilities instead of disclosing
Prioritized reputation over customer safety
Continued selling defective products
Consequences:
Consumers harmed at scale
Lost control of narrative
Greater long-term reputational damage
Responsible Disclosure
More than just the right thing to do
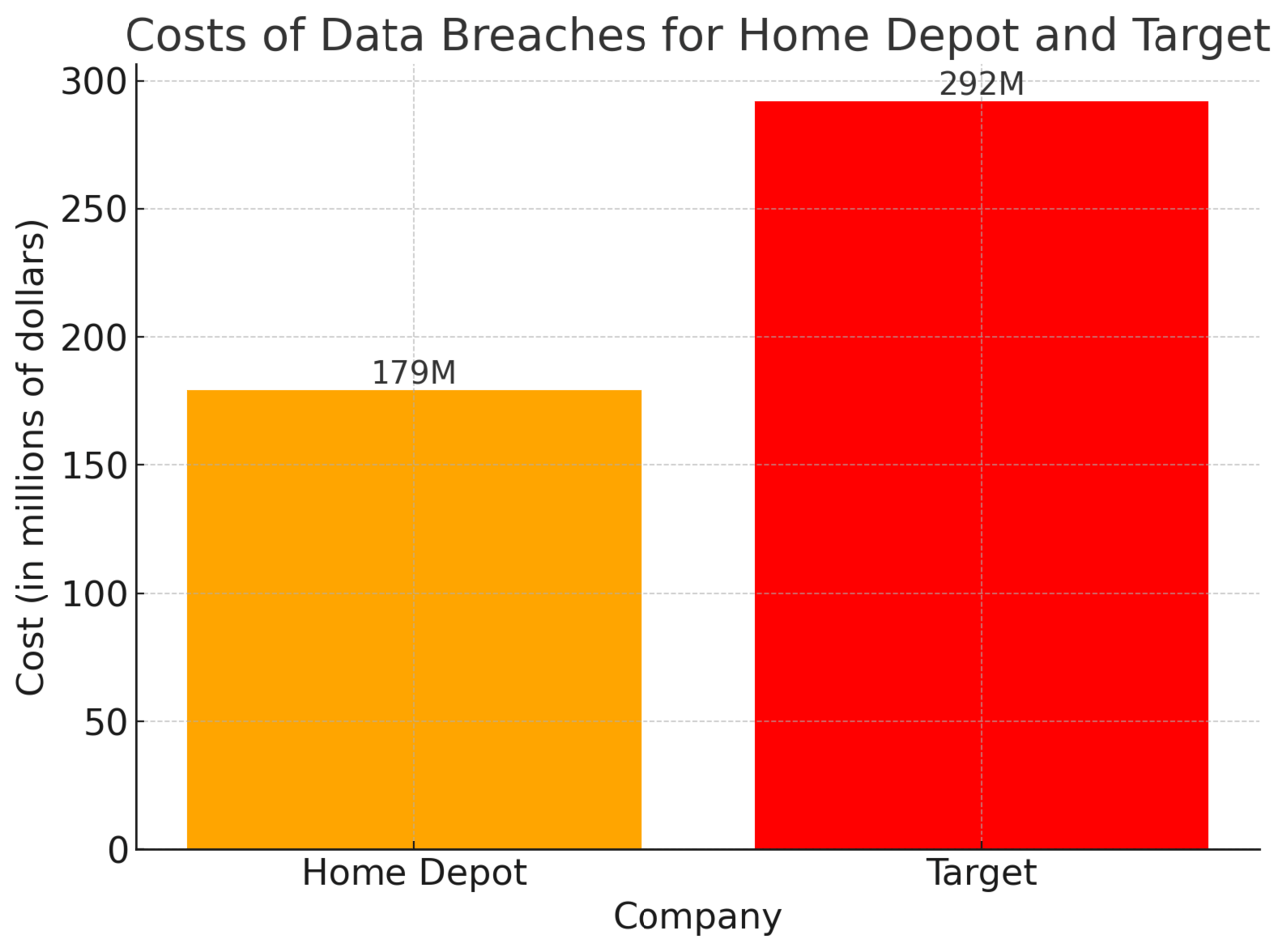
Home Depot vs Target: Comparison of Breach Response and Results
Home Depot (2014)
56 million credit cards stolen
Prompt, transparent response
Total cost: $179 million
Maintained consumer trust
Target (2013)
40 million credit cards stolen
Delayed disclosure by one week
Total cost: $292 million
CEO fired after 35 years
Crowdstrike: 2024
To our Customers and Partners, I want to sincerely apologize directly to all of you for today’s outage
Nothing is more important to me than the trust and confidence that our customers and partners have put into CrowdStrike. As we resolve this incident, you have my commitment to provide full transparency on how this occurred and steps we’re taking to prevent anything like this from happening again.
CrowdStrike (2024)
Software update caused widespread system failures
CEO provided immediate, direct apology
Committed to full transparency
Successfully managed crisis communication
Facebook: 2018
Context: In the wake of the Cambridge Analytica scandal in 2018, it was revealed that the data of 87 million Facebook users had been improperly accessed and used for political purposes.
Apology: Mark Zuckerberg, CEO of Facebook, issued multiple public apologies, including full-page ads in newspapers, acknowledging the company's failure to protect users' data and promising to improve security measures.
"We have a responsibility to protect your data, and if we can't then we don't deserve to serve you."
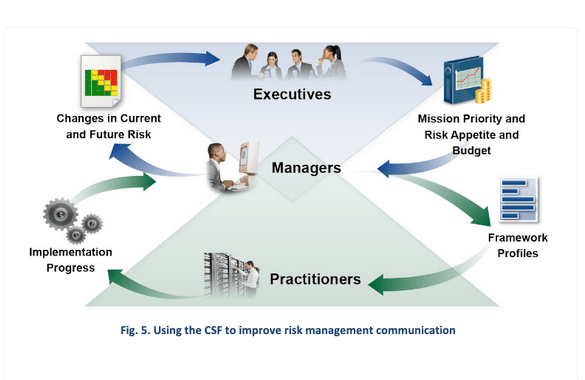
Subcategory | Implementation Examples |
|---|---|
GV.OC-02: Internal and external stakeholders are understood, and their needs and expectations regarding cybersecurity risk management are understood and considered | Ex2: Identify relevant external stakeholders and their cybersecurity-related expectations (e.g., privacy expectations of customers, business expectations of partnerships, compliance expectations of regulators, ethics expectations of society) |
GV.OC-03: Legal, regulatory, and contractual requirements regarding cybersecurity - including privacy and civil liberties obligations - are understood and managed | Ex2: Determine a process to track and manage contractual requirements for cybersecurity management of supplier, customer, and partner information |
GV.SC-05: Requirements to address cybersecurity risks in supply chains are established, prioritized, and integrated into contracts and other types of agreements with suppliers and other relevant third parties | Ex2: Include all cybersecurity and supply chain requirements that third parties must follow and how compliance with the requirements may be verified in default contractual language Ex9: Contractually require suppliers to provide evidence of performing acceptable security practices through, for example, self-attestation, conformance to known standards, certifications, or inspections |
Equifax: 2017
Context: Equifax, one of the largest credit reporting agencies in the U.S., suffered a massive data breach in 2017, exposing personal information, including Social Security numbers, of approximately 147 million people.
Apology: Richard Smith, then CEO of Equifax, issued multiple apologies, including in testimonies before Congress. He admitted that the breach was due to a failure to patch a known vulnerability, expressing deep regret for the impact on customers and pledging to improve security measures.
"This breach happened on my watch. I take full responsibility."
This breach happened on my watch. I take full responsibility
McAfee: 2010: Dave DeWalt
Context: In 2010, McAfee released a faulty antivirus update (DAT 5958) that mistakenly identified a critical Windows system file (svchost.exe) as a virus and caused widespread problems, including system crashes and failures, particularly affecting corporate customers.
Apology: Dave DeWalt, who was the CEO of McAfee at the time, issued a public apology for the incident. McAfee quickly released a fix and offered compensation to affected customers. DeWalt acknowledged the severity of the issue, which disrupted operations for many businesses, and expressed the company’s commitment to preventing such occurrences in the future.
We deeply regret the impact this flawed update had on our customers and we’re doing everything we can to make it right.

🗝 Keys to Success in Phase Two
Prioritization
Roles and responsibilities
Understanding the scale
Keeping it simple
Controlling the rate of change
🔝Prioritization

Why it matters:
Unlimited risks vs. limited resources
Need for tough choices
Requirement for quality data
Challenges:
Gaining stakeholder buy-in
Defending choices to critics
Competing with other business priorities
👥 Roles and Responsibilities

Subcategory | Implementation Example |
|---|---|
PR.AA-01: Identities and credentials for authorized users, services, and hardware are managed by the organization | Ex1: Initiate requests for new access or additional access for employees, contractors, and others, and track, review, and fulfill the requests, with permission from system or data owners when needed |
PR.AA-05: Access permissions, entitlements, and authorizations are defined in a policy, managed, enforced, and reviewed, and incorporate the principles of least privilege and separation of duties | Ex1: Review logical and physical access privileges periodically and whenever someone changes roles or leaves the organization, and promptly rescind privileges that are no longer needed |

Distribution of duties:
Assign cybersecurity roles across organization
Update job descriptions
Embed security into existing functions
Examples:
Managers: Manage privilege access (PR.AA-01)
Review access periodically (PR.AA-05)
Revoke access when employees leave
Support requirements:
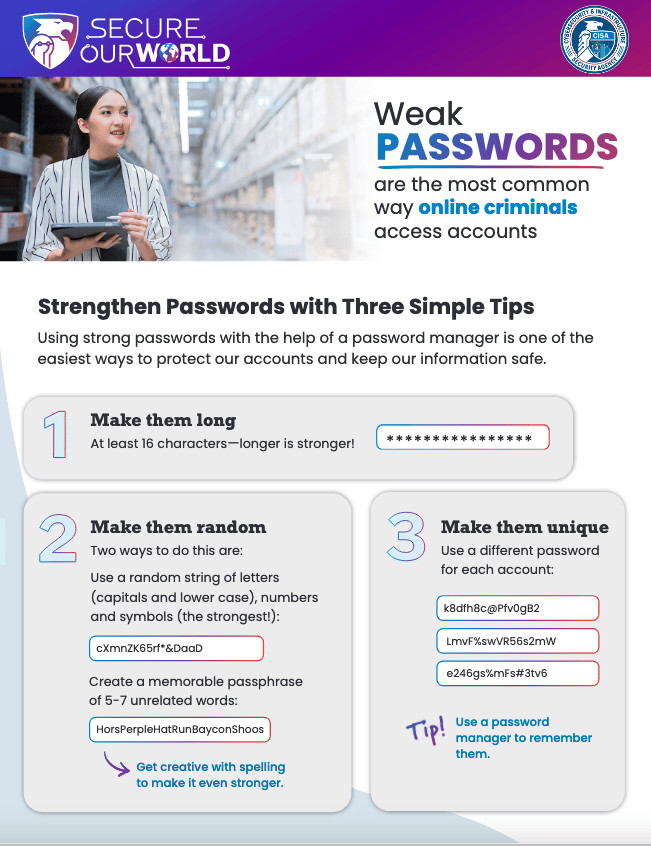
Provide necessary tools (e.g., password managers)
Deliver security awareness training
Monitor compliance through centralized reporting
Understanding Scale

Small scale sole proprietorship vs larger scale with more complexity and need for communication
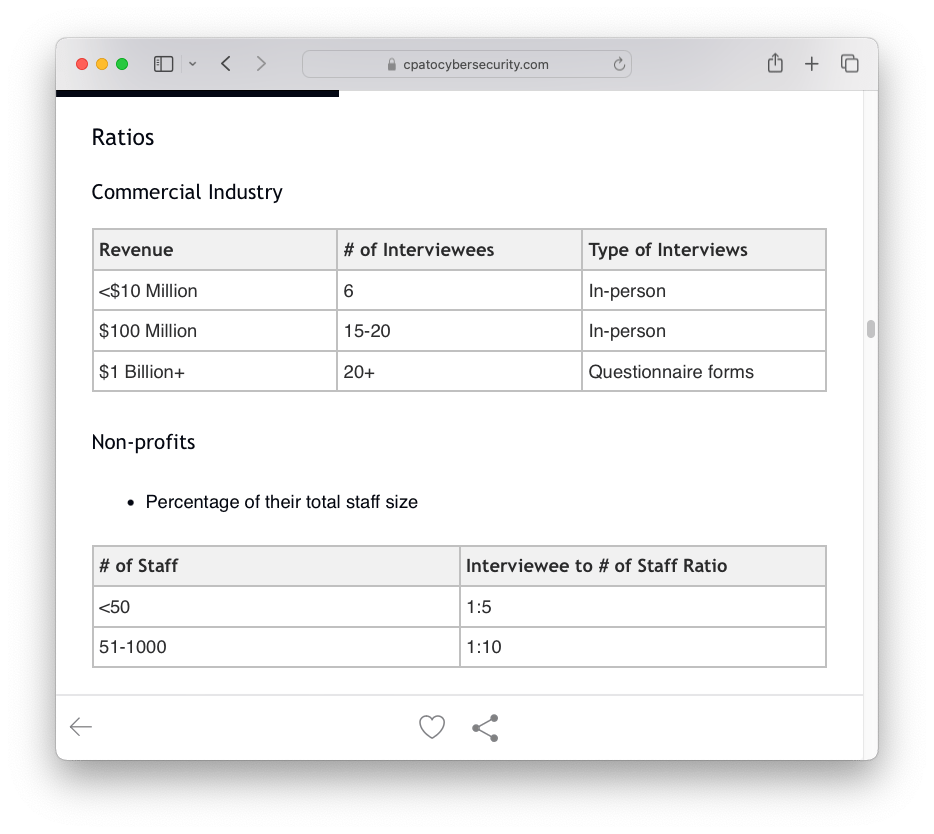
Mastering Cyber Resilience Chapter 12
Small organizations (<$10M revenue):
Simple, straightforward implementation
Direct communication
Minimal complexity
Large organizations ($1B+ revenue):
Orders of magnitude more complex
Requires culture change management
Greater potential impact
Need for sophisticated communication
✂️ Keep it Simple (KISS Principle)

Core strategies:
Focus on top 5 risks
Use plain language policies
Minimize bureaucracy
Streamline procedures
1. Prioritize and Focus on the Essentials
Identify the Top 5 Risks: Focus on risks that have the greatest impact on the business

Simplify Risk Mitigation: Develop clear, concise action plans to address each of the top 5 risks. Avoid over complicating the process; instead, focus on straightforward controls that are easy to implement and understand

Streamline Policies and Procedures
Create Simple, Clear Policies: Write cybersecurity policies in plain language, ensuring they are easy to read and understand. Focus on the most critical areas relevant to the top 5 risks, such as password management, data protection, and incident response.
Reduce Bureaucracy:

Implement Easy-to-Use Tools
Automate Key Processes: Use automation tools to handle repetitive tasks like patch management, threat detection, and incident response. This reduces the manual effort required from employees and ensures consistency in managing cybersecurity risks.
User-Friendly Security Solutions: Deploy security tools that are easy for employees to use. For example, provide a single sign-on (SSO) solution to simplify authentication processes or use a password manager to help employees create and store strong passwords.
Educate and Empower Employees
Focused Training on Top Risks: Offer targeted training sessions that focus specifically on the top 5 risks. Use real-world examples and simulations to demonstrate how these risks can affect the organization and how employees can mitigate them.
Encourage a Security-First Mindset: Reinforce the importance of cybersecurity in everyday activities. Encourage employees to report suspicious activities and recognize their role in protecting the organization from cyber threats.
Monitor Progress and Adjust
Regularly Review Risk Status: Schedule regular check-ins to assess the effectiveness of the measures implemented. Use metrics and KPIs to track progress in reducing the top 5 risks and adjust strategies as needed.
Communicate Successes: Share progress updates and successes with the entire organization. Highlighting achievements, such as a reduction in phishing incidents or quicker incident response times, can reinforce the importance of cybersecurity and maintain momentum.
By keeping the approach simple, focused, and user-friendly, you can effectively elevate the cybersecurity culture within the organization while addressing the most critical risks.
Minimize the number of steps required to follow cybersecurity procedures.
Streamline processes to make them as intuitive as possible, so employees can easily comply without feeling overwhelmed.
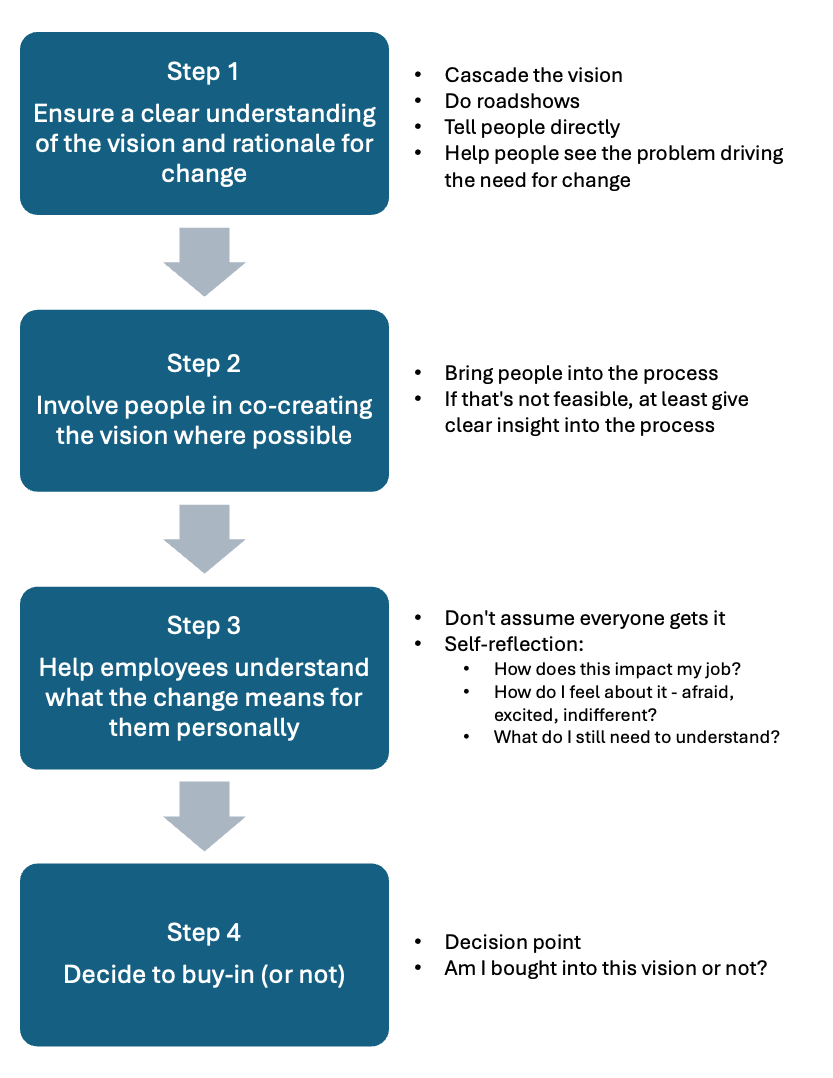
⚙ Controlling the Rate of Change
Steps in Organizational Change Adoption
Change management principles:
Avoid overwhelming staff
Sequence changes carefully
Balance with other initiatives

Not all mitigations will directly involve active changes from staff

Behind-the-scenes mitigations:
Email Filtering and Anti-Phishing Tools: Deploy advanced email filtering solutions that automatically detect and quarantine suspicious emails before they reach employees’ inboxes.
Firewalls: Deploy firewalls that automatically block unauthorized access to the network and can also detect and mitigate more complex threats like malware or ransomware.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): These systems monitor network traffic for suspicious activity and can automatically block potential threats without staff involvement.
Security Information and Event Management (SIEM): Utilize SIEM tools to automatically collect and analyze security event data in real-time, helping to identify potential threats and enabling swift automated responses.
Encryption at Rest and in Transit: Ensure that all sensitive data is encrypted both at rest and in transit. This makes it harder for attackers to access or read data even if they manage to breach security defenses.