🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
13.20 (Step 1) Considerations: Cybersecurity Org Size and Design
🏗️ Cybersecurity Org Size and Design
Company Size Categories (IANS Framework):
Midsize Companies ($50M - $400M revenue)
Small, focused security teams
Multi-hat roles common
Limited specialization
Large Companies ($400M - $6B revenue)
More dedicated teams
Broader security function coverage
Some role specialization
Fortune Companies ($6B+ revenue)
Large specialized workforces
Comprehensive security measures
Highly specialized roles
Teams can range from 50+ to 200+ (e.g., Salesforce GRC team: 200 people)

www.iansresearch.com/resources/all-blogs/post/security-blog/2023/11/15/2023-infosec-org-guidance

🚚 In-House Versus Outsourced Tasks
Companies With Cybersecurity Job Postings in Seattle
Company | Annual Revenue (Billion USD) |
Amazon | 513.9 |
Apple | 394.3 |
282.8 | |
AT&T | 120.7 |
Meta | 116.6 |
Salesforce | 34.9 |
IANS “Fortune” | 6.0+ |
IANS “Large" | 0.4-6.0 |
IANS “Midsize" | 0.05-0.4 |
Key Challenges for Smaller Organizations:
Competing for talent with tech giants
High compensation demands
Frequent talent poaching
Need for creative solutions:
Opening offices in other cities/countries
Strategic outsourcing decisions
Strategic Framework: Three Categories of Tasks
1. Core Tasks (Keep In-House)

Outsource what makes sense
Core tasks
Help the business take smart cyber risks
Deliver higher quality cybersecurity decisions than outsiders would be able to
Establish and maintain critical business relationships with people across the company, so the cybersecurity agenda gets the attention it deserves

Core Task Examples:
Cybersecurity Governance: Developing and implementing policies and frameworks that guide the security posture of the organization. This includes compliance with regulatory requirements and aligning cybersecurity strategies with business objectives.
Incident Response and Management: Establishing and maintaining an incident response team and plan that can quickly and effectively handle security breaches. This is crucial for minimizing damage and restoring operations, and requires intimate knowledge of the company's IT infrastructure and business operations.
Risk Assessment and Management: Continually assessing and managing cyber risks associated with business operations. This involves identifying, evaluating, and prioritizing risks based on their potential impact on the business and devising strategies to mitigate them.
2. Strategic Outsourcing Tasks (60-80% External)
Employees are directly assisted by outside experts who do the majority (60–80%) of the detailed work

Strategic Outsourcing Examples:
Development of First Cyber Risk Management Action Plan: Bringing NIST CSF and Cyber Resilience Practitioner expertise.
Penetration Testing and Vulnerability Assessments: Specialized skills needed for certain assessments.
Security Operations Center (SOC) Services: Outsourcing the monitoring and analysis of security alerts to a third-party provider. While the strategic oversight remains in-house, the day-to-day operations and initial incident handling can be managed by external experts.
3. Commodity Outsourcing Tasks (100% External)
Third party (outsourced) workers perform 100% of the work under the direct oversight of your employee

Commodity Outsourcing Examples:
Quarterly PCI-DSS assessment vulnerability scans: Routine scans by a certified provider for assurance that new vulnerabilities introduced by system changes or newly discovered threats are identified and remediated in a timely manner.
Managed Firewall Services: Outsourcing the routine maintenance, monitoring, and management of firewall infrastructure to a third-party provider. This includes regular updates, rule configuration, and log analysis, which are standard across many organizations.
Patch Management: Utilizing external services to ensure that software patches and updates are applied timely across the organization’s systems and applications. This task is highly standardized and crucial for securing systems from known vulnerabilities.
Email Security Services: Outsourcing email filtering and scanning to detect and block spam, phishing attempts, and other malicious messages. This service is a common necessity and can be standardized for different organizations.
13.21 🧾 Cost of Implementation

Business Language Framework
Key Principles from Jason Dion:
Stop talking tech, start talking business
Use language of money and risk
Frame as business need, not "cyber guys" need
Show tangible value, not just theory
3TCO
3TCO = (Implementation Cost) + (Annual Operating Cost x 3)


6 Example Summary
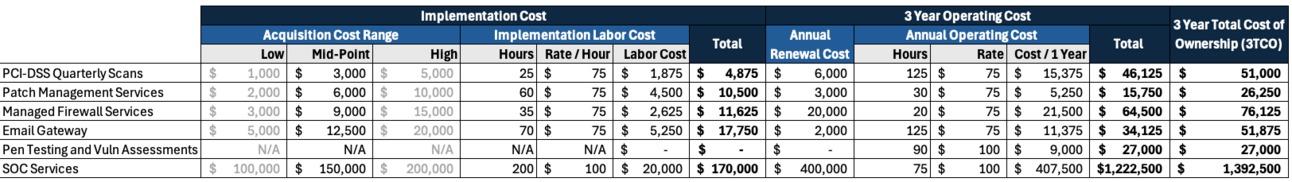
Example 1: Quarterly PCI-DSS assessment vulnerability scans
Assumptions
Acquisition Cost: This may include any initial costs for tools or services needed for scanning, such as software licenses or third-party service providers. This can range from $1,000 to $5,000 initially, depending on the scope and scale of the operations.
Implementation Hours: The setup time can vary, but might include integration with existing systems, configuring the scans, and initial run-throughs. Estimate about 10 to 40 hours for a mid-sized environment.
Labor Cost: Assuming a labor cost of $50 to $100 per hour, consistent with technical cybersecurity expertise.
Annual Renewal Cost: This includes ongoing costs for software updates, license renewals, or continued service provider fees, which might range from $2,000 to $10,000 annually.
Operating Hours per Year: Since PCI-DSS scans are conducted quarterly, additional hours will be required for reviewing scan results, addressing vulnerabilities, and ensuring compliance. Estimate about 50 to 200 hours annually, depending on the complexity and findings of the scans.
Let’s use mid-range values for these parameters:
Acquisition Cost: $3,000
Implementation Hours: 25 hours
Labor Cost: $75/hour
Annual Renewal Cost: $6,000
Operating Hours per Year: 125 hours
Step 1: Calculate Implementation Cost
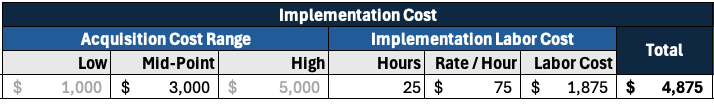
Step 2: Calculate Annual Operating Cost

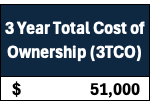
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
=$4,875+(3×$15,375)
=$4,875+$46,125
=$51,000
Example 2: Patch Management Services
Assumptions
For patch management services, which typically involve software tools and services to ensure systems are up-to-date with the latest security patches and updates, the cost estimation involves a few different components compared to hardware-centric solutions. Here’s an estimation breakdown using industry-standard assumptions:
Acquisition Cost: This may include the cost of the software license and any initial setup or integration fees. This can range from $2,000 to $10,000, depending on the complexity and scale.
Implementation Hours: Depending on the size of the environment and the complexity of integration with existing systems, implementation hours could be between 20 to 100 hours.
Labor Cost: Assuming a labor cost of $50 to $100 per hour.
Annual Renewal Cost: This generally includes ongoing software licenses and support services, which might range from $1,000 to $5,000 annually.
Operating Hours per Year: Since this service is largely automated, the annual operating hours for manual tasks (like review and adjustments to policies) might be lower, around 10 to 50 hours.
Let’s use mid-range values for these parameters:
Acquisition Cost: $6,000
Implementation Hours: 60 hours
Labor Cost: $75/hour
Annual Renewal Cost: $3,000
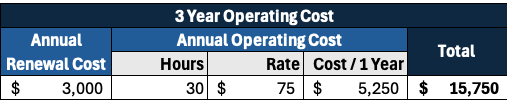
Operating Hours per Year: 30 hours
Step 1: Calculate Implementation Cost
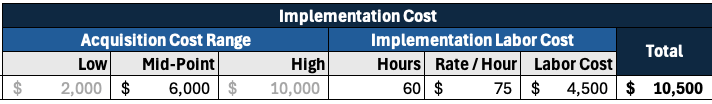
Step 2: Calculate Annual Operating Cost
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
=$10,500+(3×$5,250)
=$10,500+$15,750
=$26,250

Example 3: Managed Firewall Services Example
Assumptions
Acquisition Cost: Generally, this includes the cost of the firewall hardware and any initial setup fees by the service provider. This can vary widely, but for a mid-sized business, this might range from $3,000 to $15,000.
Implementation Hours: Managed services might require less customer-side implementation effort since the provider handles much of the setup. Estimate around 20 to 50 hours.
Labor Cost: For the client's side of implementation, using a similar labor cost as before, $50 to $100 per hour.
Annual Renewal Cost: This includes ongoing management fees, updates, and monitoring services. Typically, this would be a more substantial cost than just renewal of licenses and might range from $10,000 to $30,000 annually.
Operating Hours per Year: With managed services, the operating hours (from the client's perspective) are significantly reduced. We'll estimate about 10 to 30 hours annually, focusing on oversight and coordination rather than direct management.
Choosing mid-range values for these parameters:
Acquisition Cost: $9,000
Implementation Hours: 35 hours
Labor Cost: $75/hour
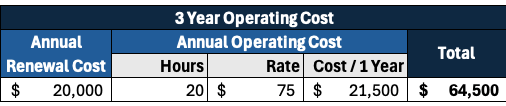
Annual Renewal Cost: $20,000
Operating Hours per Year: 20 hours
Step 1: Calculate Implementation Cost

Step 2: Calculate Annual Operating Cost
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
=$11,625+(3×$21,500)
=$11,625+$64,500=$76,125

Example 4: Email Gateway
Assumptions
Acquisition Cost: $5,000 to $20,000 depending on the capacity, features, and vendor.
Implementation Hours: 40 to 100 hours, considering setup, configuration, and testing.
Labor Cost: Approximately $50 to $100 per hour, based on the expertise required.
Annual Renewal Cost: Typically 10-20% of the acquisition cost.
Operating Hours per Year: 50 to 200 hours for maintenance, updates, and troubleshooting.
Choosing mid-range values for these parameters:
Acquisition Cost: $12,500
Implementation Hours: 70 hours
Labor Cost: $75/hour
Annual Renewal Cost: $2,000 (assuming 16% of the acquisition cost)
Operating Hours per Year: 125 hours
Step 1: Calculate Implementation Cost
Implementation Cost
=$12,500+(70 hours×$75/hour)
=$12,500+$5,250
=$17,750

Step 2: Calculate Annual Operating Cost
Annual Operating Cost
=$2,000+(125 hours×$75/hour)
=$2,000+$9,375
=$11,375
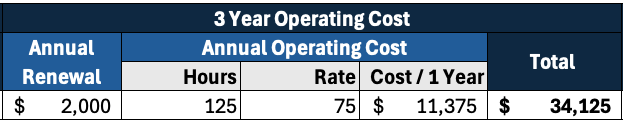
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
=$17,750+(3×$11,375)
=$17,750+$34,125
=$51,875

Example 5: Penetration Testing and Vulnerability Assessments
Assumptions
Acquisition Cost: Not applicable - pay per assessment
Annual Assessments: 1 major penetration test and 2 vulnerability assessments per year
Labor Cost: $100/hour (internal staff managing and coordinating the tests)
Annual Renewal Cost: Not applicable as each assessment is contracted separately
Operating Hours per Year: 30 hours * 3 assessments = 90 hours
Step 1: Calculate Total Annual Assessment Cost
Step 2: Calculate Annual Operating Cost
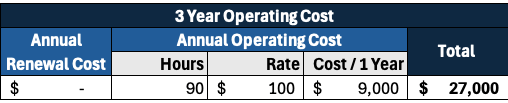
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
= $0 + (3 x $9,000)
= $27,000

Example 6: Security Operations Center (SOC) Services
Assumptions
Acquisition Cost: This could include the cost of setting up the SOC, which may involve physical infrastructure and software tools. The costs can range significantly depending on whether it's an in-house setup or outsourced. For a mid-sized business, this might range from $100,000 to $500,000.
Implementation Hours: If the SOC is being built from scratch, the implementation can be extensive, involving hundreds of hours. For simplicity, I’ll consider outsourced services where the setup time is lower, around 100 to 300 hours.
Labor Cost: This typically includes salaries for skilled cybersecurity personnel. The hourly cost could be high, but for outsourced services, this would be part of the service fee. We will include this in the annual operating costs instead.
Annual Renewal Cost: This would encompass the ongoing service fees for the SOC, including tools, personnel, and incident response services. Annually, this might range from $200,000 to $1,000,000 for a comprehensive service.
Operating Hours per Year: For outsourced SOC services, direct operating hours from the client’s side are significantly reduced, mainly involving periodic reviews and strategic oversight, perhaps 50 to 100 hours per year.
Let’s select typical values for outsourced SOC services for a mid-sized company:
Acquisition Cost: $150,000 (this might include initial setup fees for an outsourced service)
Implementation Hours: 200 hours
Labor Cost: $100/hour (estimated oversight and coordination cost)
Annual Renewal Cost: $400,000 (a typical mid-range annual fee)
Operating Hours per Year: 75 hours
Step 1: Calculate Implementation Cost

Step 2: Calculate Annual Operating Cost
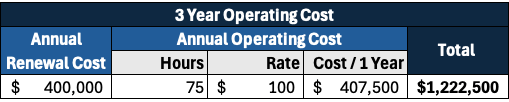
Step 3: Calculate 3-Year Total Cost of Ownership (3TCO)
3TCO
=$170,000+(3×$407,500)
=$170,000+$1,222,500
=$1,392,500

⚖️ 3TCO for Our 8 Gap Closing Actions

Key Takeaways:
Cybersecurity is a business risk, not just an IT issue
Success requires speaking the language of business
3TCO analysis enables better decision-making
Business value must be clearly articulated
Trust is central to all security value propositions
Balance in-house expertise with strategic outsourcing
Responsible disclosure builds trust and saves money
Internal and external marketing are crucial for buy-in
Documentation and metrics support long-term success


