🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
12.13 🤝 Step 6: Conduct the Interviews
Enabling Competency: Communication

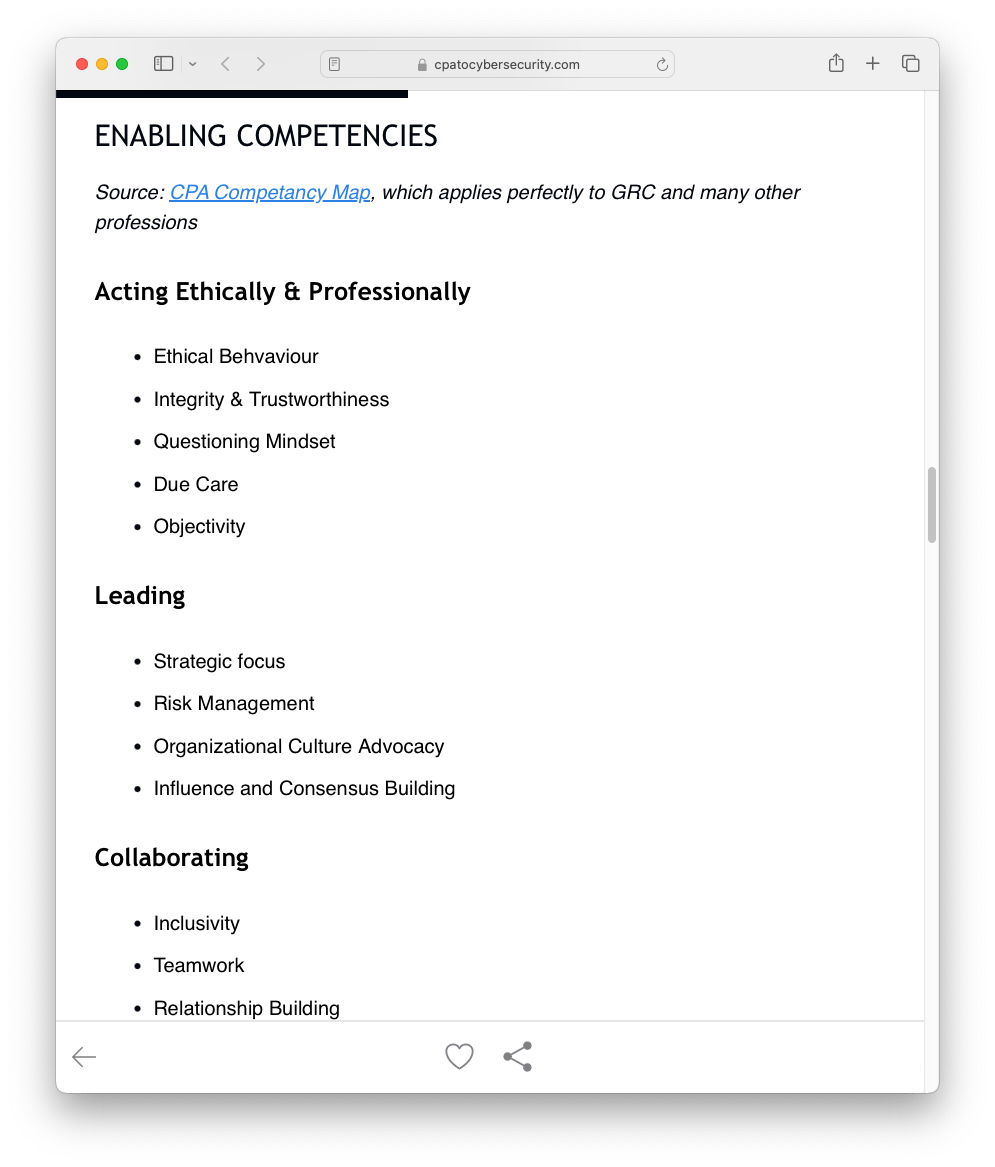

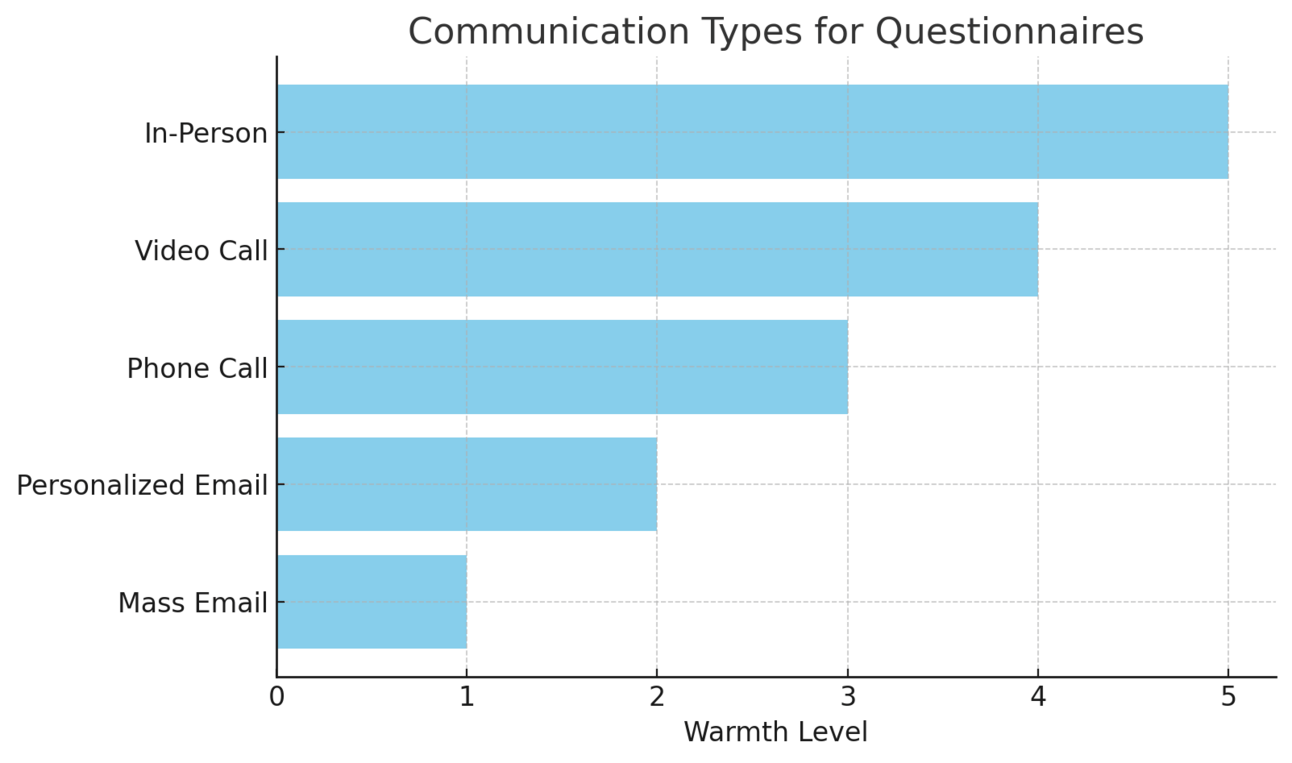
Communication Methods (Ranked by Effectiveness)
The warmer the communication type the better
In-person interviews (Most effective)
Allows for reading body language
Builds stronger rapport
Enables real-time clarification
Video calls with cameras on
Maintains visual connection
More personal than audio-only
Screen sharing capabilities for score key
Phone calls
Good alternative when video isn't possible
Still allows for real-time dialogue
Email (Least preferred)
Loses emotional context
Higher risk of misunderstanding
Difficult to build trust
Interview Best Practices
Tips from the Interview Pros:
It's a training opportunity
Most interviewees are unfamiliar with cyber resilience concepts
Use this as a chance to educate while gathering data
Build security awareness throughout the organization
Consider who conducts the interview
Having a respected senior employee lead can increase buy-in
Neutral outsiders bring objectivity
Avoid having direct supervisors conduct interviews (may inhibit candor)
Provide printed score key
Hand out physical copy during interview
Ensures consistent reference point
Helps maintain uniform scoring across all interviewees

Managing Transformative Shift
"Who Moved My Cheese?" Philosophy:
Change is inevitable - Organizations must adapt or fail
Historical examples:
Blockbuster - Failed to adapt to streaming (stuck in old model)

Netflix - Successfully pivoted from DVDs to streaming to original content
IBM - Transformed from hardware to services in the 1990s
Kodak - Struggled with digital photography transition
Applying to Cybersecurity:
Expect resistance to new security measures
Foster adaptability through empathetic communication
Emphasize collaboration - Everyone has a role in transformation
Align with business objectives - Show how security enables success
Foster a candid and respectful atmosphere

Physical space considerations:
Private, quiet location
Comfortable temperature
Minimal distractions
Psychological safety elements:
Non-judgmental tone
Active listening
Validate their expertise
Thank them for their time
Professional boundaries:
Keep discussions focused
Avoid blame or criticism
Maintain neutrality
Document objectively
📋 Pre-Interview Checklist
✅ Have a meaningful subject line and agenda in your calendar appointment
✅ Show up early
✅ Prepare thoroughly
✅ Get the meeting room logistics right
✅ Get the teleconference audio/visual tech right
📋 Interview Checklist
✅ First 10 minutes: overview of the process
✅ Reiterate that this is not an external audit
✅ Provide the zero-to-ten scoring key and ask if any questions
✅ Encourage the expert to be candidly respectful in their responses
✅ Assure interviewees that their scores will remain confidential: no specific comments or scores will be attributed to individuals
✅ Maintain a brisk tempo and keep it under an hour
✅ Avoid requesting any justifications for scores, but if interviewees voluntarily provide explanations, be sure to record them

Additional Pro Tips
Managing Interview Challenges:
"I don't know about cybersecurity"
Response: "You know your department's practices better than anyone"
Emphasize their operational expertise is what's needed
Remind them perceptions are valuable data points
Handling zero scores
Zero is not a failure - it's honest feedback
Ask for context (not justification)
Document the explanation for Phase 2 planning
Building psychological safety
When people feel heard, they feel respected
Active listening increases buy-in for changes
Creates allies for transformation efforts
Interview Tempo Management:
Keep it efficient
Interviews should not be arduous
Respect expertise and time
Leave positive impression
Pacing guidelines:
10 minutes: Introduction and setup
40 minutes: Core questions (≈2 minutes per question)
10 minutes: Wrap-up and next steps
Sample Introduction Script:
"Thank you for joining me today. We're conducting a management-driven assessment - not an audit - to understand our current cyber risk posture. Your candid input based on your department's practices is invaluable. All responses will be kept confidential and aggregated with others. Let's review the scoring system together before we begin..."
🧮 Step 7: Compile and Average the Scores
Overview
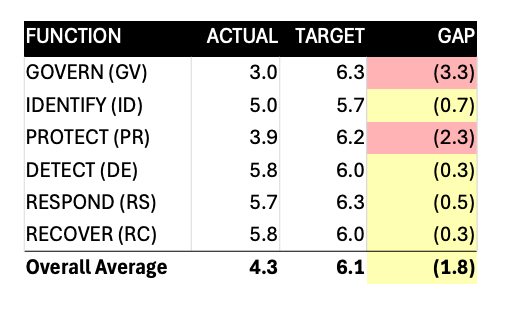
Once you've completed all interviews and recorded the scores, the next step is to average them and compare actuals to target for every function, category, and activity in the NIST Cybersecurity Framework based on your questionnaire.
Understanding the Radar Diagram
In the example from the textbook:
Outer dashed ring = Target score (6.0 in this example)
Inner dotted ring = Minimum acceptable risk level (5.0)
Solid jagged line = Actual average response scores from interviewees
Gap analysis = Difference between actual and target scores

Identifying Top 5 Cyber Risks (Ranked by Gap Size)
GV.SC[a] - Cybersecurity Supply Chain Risk Management
PR.AA[a] - Identity Management, Authentication & Access Control
GV.OC - Organizational Context
RS.AN - Incident Analysis
PR.AT - Awareness and Training

Managing "Junk Data"
Common Causes of Junk Data:
Knowledge gaps - Interviewee lacks visibility into actual practices
Overconfidence - Assuming IT department has everything covered
Interview fatigue - Rushing to complete the interview
Misunderstanding - Not grasping the scoring scale properly
Best Practices for Handling Junk Data:
DON'T delete the data - This is the most common mistake
DO exclude from calculations - Keep it separate from averaged scores
DO document patterns - Note if specific groups (e.g., executives, operations) consistently provide unrealistic scores
DO analyze root causes - Use insights to identify organizational themes
DO incorporate findings - Address these issues in Phase 2 or 3 of CR-MAP
Examples of Junk Data Patterns:
All executives scoring 8+ across the board (disconnect from operations)
All operations personnel defaulting to 8 (interview fatigue)
Consistent "unknown" responses from people who should know (wrong interviewees selected)

🗣️ Step 8: Communicate Your Top Five Cyber Risks
When Results Fall Short of Expectations
Reality check: "We're at 4.3 when we want to be at 6.0"
Follow-up actions:
Conduct additional discussions with cyber risk experts
Validate gap analysis with subject matter experts
Calibrate scores to ensure accuracy
Prepare supporting data for executive presentations
Determine “So What, What’s Next,” From the Data
Analyze the data to uncover narratives
Common Organizational Themes:
Strong in PROTECT function
Heavy investment in firewalls, antivirus, access controls
Traditional IT security focus
Weak in DETECT and RECOVER functions
Limited monitoring capabilities
Insufficient incident response planning
Lack of recovery procedures

Why These Patterns Emerge:
Historical perspective: Cyber risks viewed primarily as IT problems
Resource allocation: Most budget goes to prevention tools
Detection gaps:
Excel at detecting service outages
Miss potential data breaches
Limited visibility into advanced threats
Recovery challenges:
Unaccustomed to public scrutiny
Marketing departments unprepared for breach communications
Lack of crisis management expertise
Bottom-Line Communication Strategy
Lead with business impact, not technical details
Use visual aids (heat maps, radar diagrams, tables)
Provide context from your organization's specific data
Avoid fear-mongering from headlines or vendor narratives
Focus on actionable insights rather than problems

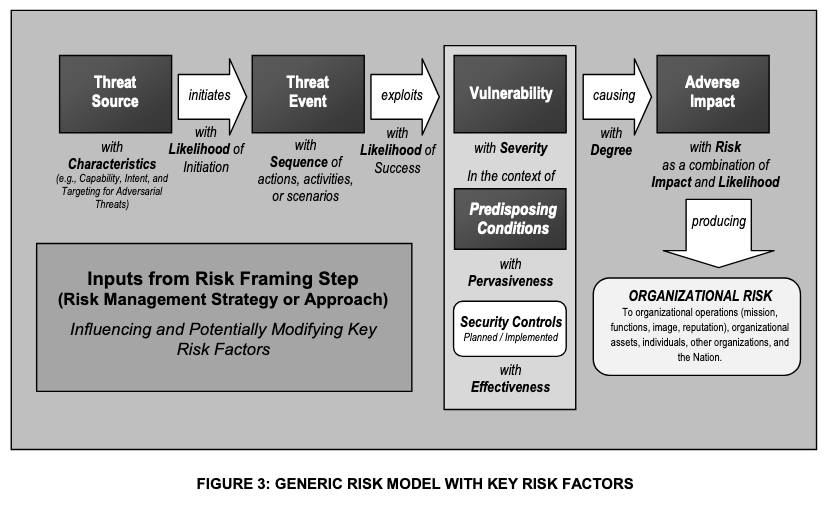
Instructor Note on Vulnerability vs Threat Perspectives in Cyber Risk Presentations
Risk = Threat x Vulnerability ⚠️
✅ Conclusion and Touchpoints
Phase One: Discovering Top Cyber Risks
Effective Risk Prioritization: Adds value by protecting and enabling the business within resource limits.
Broaden Cybersecurity Scope: Consider beyond just technological defenses.
Set Proper Expectations: Learn from companies like Expeditors, Blockbuster, and Netflix.
Employee Buy-In: Critical for successful cybersecurity changes.
Candid Communication: Encourage honesty in the interview process.
Respect Time: Keep interviews brisk and efficient, provide score key handouts.
Target Specific Functions: Focus on NIST Cybersecurity Framework (functions 5-8).
Tailored Approach: Align efforts with unique organizational needs and risks.
Top Five Risks: Identify patterns like strengths in protection and gaps in detection/recovery.
Business Perspective: Treat cyber risks as business risks, not just tech issues.
Avoid Fear-Mongering: Base decisions on organizational risks, not headlines or vendor stories.