🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
13.14 Governance and Why Policies Matter
Key Concepts
Clear Expectations: Establish comprehensive policies baselined against industry frameworks
Malicious Insider Protection: Without clear policies, malicious insiders can claim ignorance of prohibited actions
Turn on your negative mindset for a moment to risk assess a malicious insider attack scenario, where an insider harms your company and your colleagues, in a way that seems really bad
If your policies weren’t comprehensive enough by being baselined against an industry framework, the justice system is going to have a hard time being effective, because the malicious insider can say, “I didn’t know that wasn’t’ allowed”
Legal Enforceability: Comprehensive policies enable effective legal action against violations
Not legal advice here, of course, but food for thought
Governance and Compliance as Your GRC On-Ramp
And then finally, compliance. This is like your on-ramp to GRC. Compliance is straightforward. There's a list of documented requirements, whether it's PCI (Payment Card Industry), or it is HIPAA (the Health Insurance Portability and Accountability Act). I don't want to say compliance is easy, but compliance is easy to understand. Here's a bunch of things: are you doing them? Yes or no. This is where a lot of GRC people actually start in their career because you audit against the compliance standard.
Some industry resources to check out here are ISO27k, NIST Special Publications, CRI, CIS CSC, COBIT 5, ITIL, PCI DSS, HIPPA, NERC CIP, FedRAMP, STAR and OWASP

13.15 Protecting Data in Transit and at Rest
Security Questionnaire Case Study Question 1: PR.DS Protecting Data in Transit and at Rest

NIST CSF Category Lookup: PR.DS-01 and PR.DS-02
CSF Subcategory ID | Implantation Example(s) |
|---|---|
PR.DS-01: The confidentiality, integrity, and availability of data-at-rest are protected | Ex1: Use encryption, digital signatures, and cryptographic hashes to protect the confidentiality and integrity of stored data in files, databases, virtual machine disk images, container images, and other resources |
PR.DS-02: The confidentiality, integrity, and availability of data-in-transit are protected | Ex1: Use encryption, digital signatures, and cryptographic hashes to protect the confidentiality and integrity of network communications |
Informative References
CIS Controls v8.0
3.11 Encrypt Sensitive Data at Rest
SP 800-53 Rev 5.1.1
CA-03: Information Exchange
CP-09: System Backup
MP-08: Media Downgrading
SC-04: Information in Shared System Resources
SC-07: Boundary Protection
SC-12: Cryptographic Key Establishment and Management
SC-13: Cryptographic Protection
SC-28: Protection of Information at Rest
SC-32: System Partitioning
SC-39: Process Isolation
SC-43: Usage Restrictions
SI-03: Malicious Code Protection
SI-04: System Monitoring
SI-07: Software, Firmware, and Information Integrity
CIS Controls v8.0
3.10 Encrypt Sensitive Data in Transit
SP 800-53 Rev 5.1.1
AU-16: Cross-Organization Audit Logging
CA-03: Information Exchagne
SC-04: Information in Shared System Resources
SC-07: Boundary Protection
SC-08: Transmission Confidentiality and Integrity
SC-11: Trusted Path
SC-12: Cryptographic Key Establishment and Management
SC-13: Cryptographic Protection
SC-16: Transmission of Security and Privacy Attributes
SC-40: Wireless Link Protection
SC-43: Usage Restrictions
SI-03: Malicious Code Protection
SI-04: System Monitoring
SI-07: Software, Firmware, and Information Integrity
CIS Controls
Encryption in transit examples:
Sending an email, from your laptop to a 3rd party Gmail server to the person’s phone you sent it to
Or saving a document on Sharepoint - that file goes from the computer to your cloud to your colleagues
Or typing in your password to log into a service - that’s sensitive data that encryption helps to keep confidential
TLS (Transport Layer Security)
A handshake between an end users web browser, and a back end server, establishing an encrypted session that puts a padlock beside the URL in your browser
SSH (Secure Shell)
Typically used in the Command Line Interface (CLI) for remote management of servers and network hardware.
Frequently used in automated scripts for remote system updates, backups and administrative tasks, or in an Integrated Development Environment (IDE) for connecting to version control systems, remote debugging and deploying applications
Encryption at rest examples:
Operating systems
Bitlocker (WIndows)
Veracrypt (Windows, Ubuntu, macOS)
FileVault (macOS)
Database encryption
Data files on the disk, backup files, logs
Mobile device encryption
Modern hard drives and solid-state drives (SSDs)
NIST SP 800-53
SC-12 Cryptographic Key Establishment and Management
There are two main types of encryption:
Distinct Features | Symmetric (Secret Key) Cryptography | Asymmetric (Public Key Cryptography) |
|---|---|---|
Number of Keys | Single Key | Pair of keys |
Types of Keys | Key is secret | One key is private, and one key is public |
Protection of Keys | Disclosure and modification | Disclosure and modification for private keys and modification for public keys |
Relative Speeds | Faster | Slower |
Asymmetric Encryption
Symmetric Encryption
Uses the same key for both encrypting and decrypting data (block cipher). This key must be shared and kept secret between the sender and the recipient
Examples are AES (Advanced Encryption Standard) and DES (Data Encryption Standard)
Typically faster than asymmetric encryption and is commonly used for encrypting large amounts of data
Often used for encrypting data at rest, such as files on a hard drive, or data in transit in scenarios where secure key exchange has already occurred
SYMMETRIC KEYS
Produce, control, and distribute symmetric cryptographic keys using [Selection: NIST FIPS- validated; NSA-approved] key management technology and processes.
Discussion: [SP 800-56A], [SP 800-56B], and [SP 800-56C] provide guidance on cryptographic key establishment schemes and key derivation methods.
NIST SP 800-53, REV. 5
SP 800-56A: Recommendation for Pair-Wise Key Establishment Using Discrete Logarithm Cryptography
Use of asymmetric (public key) cryptography to securely establish symmetric (shared keys) between two parties.
Although SP 800-56A is primarily about key exchange mechanisms like Diffie-Hellman (DH) and Elliptic Curve Diffie-Hellman (ECDH), the secure keys established can be used with symmetric key algorithms like AES-256 for encrypting data in transit.
AES is considered a “well established cryptographic scheme”
AES is defined in FIPS-197
AES-256 has the largest key length and number of rounds
FIPS-197: Advanced Encryption Standard (AES)
FIPS-198: The Keyed-Hash Message Authentication Code (HMAC)
HMAC (Hash-Based Message Authentication Code) can be used in conjunction with AES (Advanced Encryption Standard) to provide both encryption and integrity protection for data in transit
For example, in a typical TLS session, AES might be used to encrypt the data being transmitted, while HMAC is used to ensure the data integrity and authenticate that the data has not been tampered with during transit
SP 800-56B: Recommendation for Pair-Wise Key Establishment Using Integer Factorization Cryptography
Like 800-56A, it's about secure key exchange, but based on RSA encryption methods.
The keys established can similarly be used with symmetric encryption algorithms such as AES-256 for secure data transmission.
NIST SP 800-56C: Recommendation for Key-Derivation Methods in Key-Establishment Schemes
Key derivation methods are another crucial process that we don’t want to become the weak link
Even if AES-256 encryption is robust, the security of the encryption scheme is largely dependent on the secrecy and integrity of the keys used. If keys are derived or managed poorly, the strength of AES-256 can be undermined
If our vendor adheres to these guidelines, it can add a layer of trust in how they handle key management
13.16 Identity Management and Access Control
Question 2: PR.AA-05 Access Permissions | Principle of Least Privilege

NIST CSF Category Lookup: PR.AA-05
CSF Subcategory ID | Implementation Example(s) |
|---|---|
PR.AA-05: Access permissions, entitlements, and authorizations are defined in a policy, managed, enforced, and reviewed, and incorporate the principles of least privilege and separation of duties | Ex1: Review logical and physical access privileges periodically and whenever someone changes roles or leaves the organization, and promptly rescind privileges that are no longer needed Ex2: Take attributes of the requester and the requested resource into account for authorization decisions (e.g., geolocation, day/time, requester endpoint's cyber health) Ex3: Restrict access and privileges to the minimum necessary (e.g., zero trust architecture) Ex4: Periodically review the privileges associated with critical business functions to confirm proper separation of duties |
Informative References
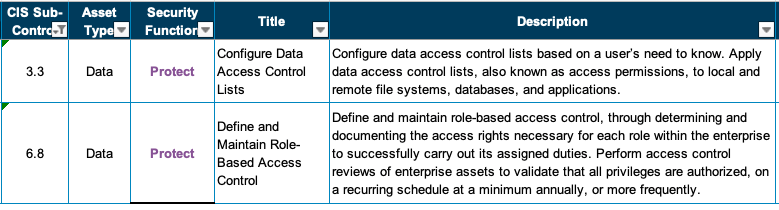
CIS Controls v8.0:
SP 800-53 Rev 5.1.1:
AC-01: Access Control Policy and Procedures
AC-02: Account Management
Authorize access to the system based on:
A valid access authorization;
Intended system usage; and
[Assignment: organization-defined attributes (as required)];
AC-03: Access Enforcement
Role-based access control (RBAC) is an access control policy that enforces access to objects and system functions based on the defined role (i.e., job function) of the subject.
AC-05: Separation of Duties
AC-06: Least Privilege
Employ the principle of least privilege, allowing only authorized accesses for users (or processes acting on behalf of users) that are necessary to accomplish assigned organizational tasks.
AC-10: Concurrent Session Control
AC-16: Security and Privacy Attributes
AC-17: Remote Access
AC-18: Wireless Access
AC-19: Access Control for Mobile Devices
AC-24: Access Control Decisions
Question 3: ID.AM-8 Data Lifecycle | Securely Dispose of Data


NIST CSF Category Lookup: ID.AM-08
CSF Subcategory ID | Implementation Example(s) |
|---|---|
ID.AM-08: Systems, hardware, software, services, and data are managed throughout their life cycles | Ex7: Securely destroy stored data based on the organization's data retention policy using the prescribed destruction method, and keep and manage a record of the destructions |
Informative References
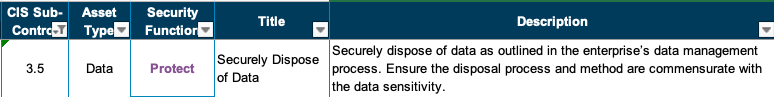
CIS Controls v8.0: 1.1 CIS Controls v8.0: 3.5
SP 800-53 Rev 5.1.1:
CM-09: Configuration Management Plan
CM-13: Information System Monitoring Plan
Control: Develop and document a map of system data actions.
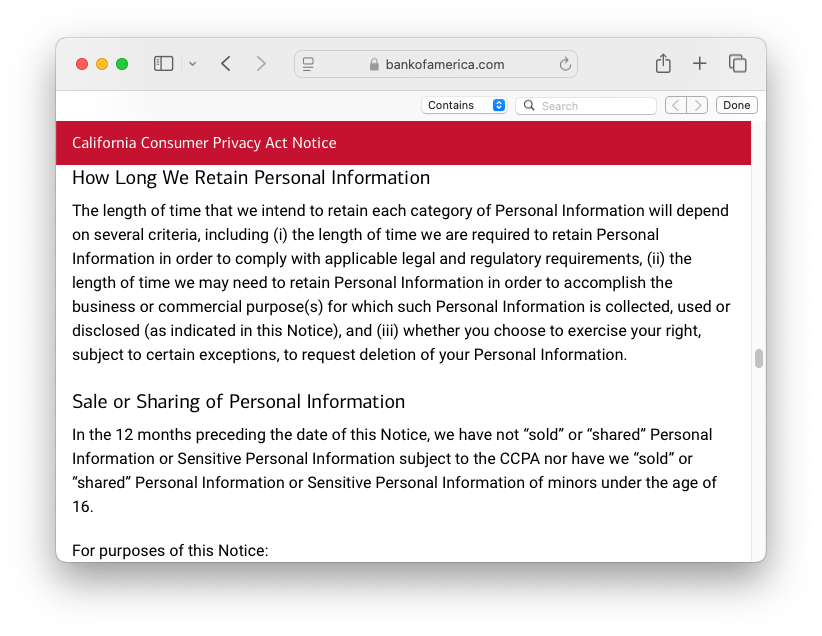
Discussion: Data actions are system operations that process personally identifiable information. The processing of such information encompasses the full information life cycle, which includes collection, generation, transformation, use, disclosure, retention, and disposal.
MA-02: Controlled Maintenance
MA-06: Timely Maintenance
PL-02: System Security Plan
PM-22: Personally Identifiable Information Quality Management
PM-23: Data Governance Body
A Data Governance Body can help ensure that the organization has coherent policies and the ability to balance the utility of data with security and privacy requirements.
SA-03: System Development Life Cycle
SA-04: Acquisition Process
SA-08: Security Engineering Principles
SA-22: Unsupported System Components
SI-12: Information Management and Retention
Information management and retention requirements cover the full life cycle of information, in some cases extending beyond system disposal. Information to be retained may also include policies, procedures, plans, reports, data output from control implementation, and other types of administrative information.
SI-18: Personally Identifiable Information Quality Operations
SR-05: Acquisition Strategies, Tools and Methods
SR-12: Component Disposal

13.17 Identity Management, Authentication, and Access Control - ⭐ ft. Dr. Gerald Auger in the Daily Cyber Threat Briefing
📋 STEP 1 CONTINUED: Close the identified gaps

🚨2, 3. Identity Management, Authentication, and Access Control (PR.AA):
Access to physical and logical assets is limited to authorized users, services, and hardware and managed commensurate with the assessed risk of unauthorized access.
NIST SP 800-53 Security and Privacy Controls for Information Systems and Organizations: Access Control Family
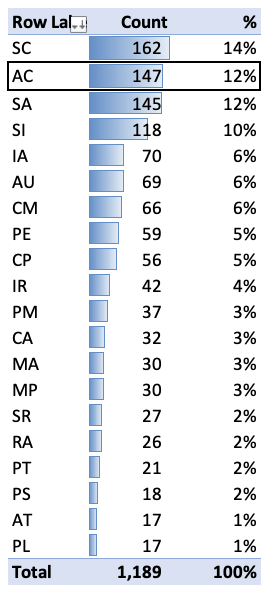
Second largest control family in NIST SP 800-53
147 controls total
12% of all available controls
Critical for: Preventing unauthorized access
Government Example System Security Plan Template
The AC tab of a RMF workbook can be a mountain!
Your CR-MAP Questionnaire Question from PR.AA-01, PR.AA-02, PR.AA-03, PR.AA-04
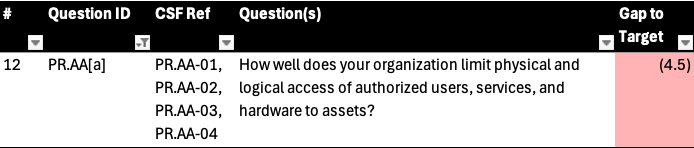
Subcategories |
|---|
PR.AA-01: Identities and credentials for authorized users, services, and hardware are managed by the organization |
PR.AA-02: Identities are proofed and bound to credentials based on the context of interactions |
PR.AA-03: Users, services, and hardware are authenticated |
PR.AA-04: Identity assertions are protected, conveyed, and verified |
PR.AA-01 NIST Implementation Examples
Ex1: Initiate requests for new access or additional access for employees, contractors, and others, and track, review, and fulfill the requests, with permission from system or data owners when needed
Ex2: Issue, manage, and revoke cryptographic certificates and identity tokens, cryptographic keys (i.e., key management), and other credentials
Ex3: Select a unique identifier for each device from immutable hardware characteristics or an identifier securely provisioned to the device
Ex4: Physically label authorized hardware with an identifier for inventory and servicing purposes
PR.AA-02 NIST Implementation Examples
Ex1: Verify a person's claimed identity at enrollment time using government-issued identity credentials (e.g., passport, visa, driver's license)
Ex2: Issue a different credential for each person (i.e., no credential sharing)
PR.AA-03 NIST Implementation Examples
Ex1: Require multifactor authentication
Ex2: Enforce policies for the minimum strength of passwords, PINs, and similar authenticators
e.g. NIST SP 800-63b
Ex3: Periodically reauthenticate users, services, and hardware based on risk (e.g., in zero trust architectures)
Ex4: Ensure that authorized personnel can access accounts essential for protecting safety under emergency conditions
PR.AA-04 NIST Implementation Examples
Ex1: Protect identity assertions that are used to convey authentication and user information through single sign-on systems
Ex2: Protect identity assertions that are used to convey authentication and user information between federated systems
Ex3: Implement standards-based approaches for identity assertions in all contexts, and follow all guidance for the generation (e.g., data models, metadata), protection (e.g., digital signing, encryption), and verification (e.g., signature validation) of identity assertions
Your Recommended Action Plan For Identity Management, Authentication and Access Control (PR.AA-01, PR.AA-02, PR.AA-03, PR.AA-04)
Action 4: Implement Centralized Identity Management with Single Sign-On
Use a centralized identity management system (e.g., IAM solutions like Okta or Azure AD) to manage identities and credentials for users, services, and hardware with single sign-on.
This system should integrate with all critical services and hardware to ensure consistent and secure identity management.

Action 5: Enforce Multi-Factor Authentication (MFA)
Enforce MFA for all access to critical systems, services, and sensitive data. This applies to employees, contractors, and any third parties who require access.
Other Potential Actions
Centralize and Automate Access Request Tickets: For initiating, tracking, and reviewing access requests. Ensure this system requires approval from data or system owners before granting access.

Define Role-Based Access Control (RBAC): Define and implement RBAC in key systems, ensuring that each role has access only to the resources necessary for their job functions.
Exit Procedure for Departing Employees: Implement a strict exit procedure that ensures all access privileges are rescinded immediately when an employee or contractor leaves the organization. This includes revoking physical access, disabling system accounts, and retrieving any company-issued devices.
Quarterly Access Reviews: Conduct quarterly reviews of both logical (e.g., system access) and physical (e.g., office entry) access privileges. Use automated tools to generate reports for review, and ensure that privileges are promptly rescinded for users who no longer require them.
Context-Aware Authorization: Implement context-aware security measures that evaluate attributes such as geolocation, time of access, and the security health of the requester’s device before granting access. This can be achieved through advanced IAM solutions that support conditional access policies.
Zero Trust Architecture: Gradually transition to a Zero Trust security model where every access request, whether internal or external, is authenticated, authorized, and encrypted. Start by segmenting the network and enforcing strict access controls at each segment.
🧠 4. Awareness and Training
Why Training Matters
Defense-in-Depth Limitations: Technical controls alone cannot prevent all attacks
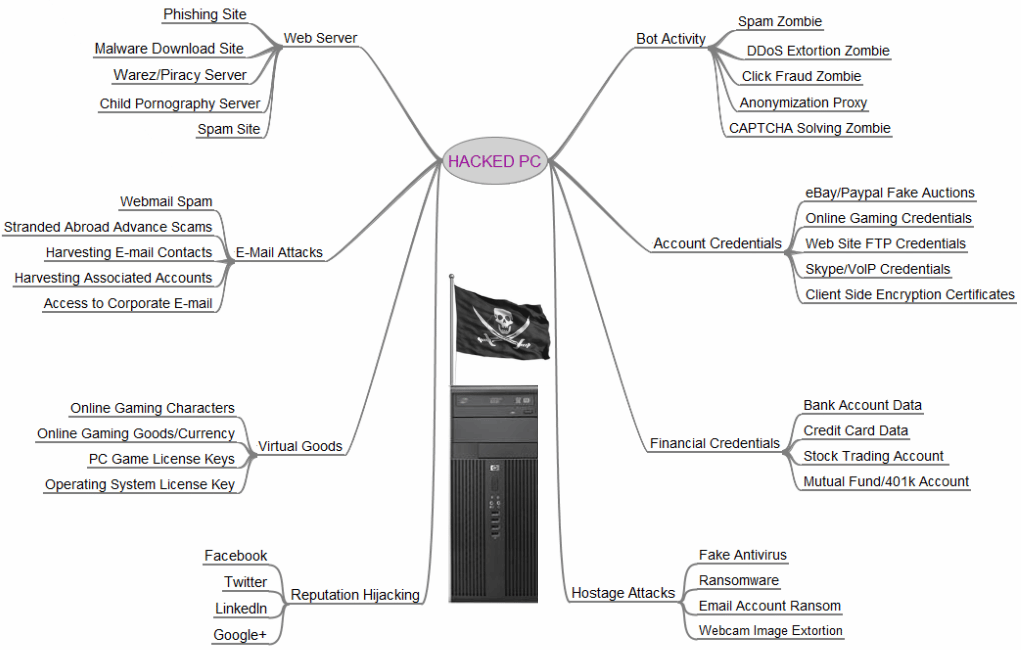
Users Are Targets: Every employee account has value to attackers
Human Factor: Social engineering exploits trust, not technology
"You ARE a target" - Not because you're personally interesting, but because your accounts and data are valuable to attackers
Your Questionnaire Question for PR.AT

Subcategories |
|---|
PR.AT-01: Personnel are provided with awareness and training so that they possess the knowledge and skills to perform general tasks with cybersecurity risks in mind PR.AT-02: Individuals in specialized roles are provided with awareness and training so that they possess the knowledge and skills to perform relevant tasks with cybersecurity risks in mind |
Why is Security Awareness Training Important When We have All of These Defense-In-Depth Layers?
PR.AT-1 NIST Implementation Examples
Ex1: Provide basic cybersecurity awareness and training to employees, contractors, partners, suppliers, and all other users of the organization's non-public resources
Ex2: Train personnel to recognize social engineering attempts and other common attacks, report attacks and suspicious activity, comply with acceptable use policies, and perform basic cyber hygiene tasks (e.g., patching software, choosing passwords, protecting credentials)
Ex3: Explain the consequences of cybersecurity policy violations, both to individual users and the organization as a whole
Ex4: Periodically assess or test users on their understanding of basic cybersecurity practices
Ex5: Require annual refreshers to reinforce existing practices and introduce new practices
PR.AT-2 NIST Implementation Examples
Ex1: Identify the specialized roles within the organization that require additional cybersecurity training, such as physical and cybersecurity personnel, finance personnel, senior leadership, and anyone with access to business-critical data
Ex2: Provide role-based cybersecurity awareness and training to all those in specialized roles, including contractors, partners, suppliers, and other third parties
Ex3: Periodically assess or test users on their understanding of cybersecurity practices for their specialized roles
Ex4: Require annual refreshers to reinforce existing practices and introduce new practices
Your Recommended Action Plan for PR.AT-01, PR.AT-02
Action 6: Provide Basic Cybersecurity Awareness and Training
Implement mandatory annual “Security Essentials” cybersecurity training for all employees, contractors, partners, suppliers, and other users with access to the organization's resources, as well as monthly Intranet blog posts, providing a security team mailbox to ask any questions.
This training should cover fundamental topics such as recognizing phishing and social engineering attacks, reporting suspicious activity, cybersecurity policies and basic cyber hygiene.

PR.AT-02 Specialized Role Cyber Risk Training: LastPass Breach Case Study
Key areas for specialized training:
Acceptable Use Policy and Remote Work Security: The breach originated from a compromised home network, demonstrating the need for security practices that extend beyond the corporate perimeter.
Endpoint Security: Training is essential in ensuring that admins enforce proper endpoint protection, including the removal of unnecessary software and maintaining regular updates.
Privileged Access Management (PAM): The attack highlights the critical need for secure handling of privileged accounts and enforcing strong controls like multifactor authentication (MFA) and secure storage of decryption keys.
Other Potential Actions
Basic Cybersecurity Awareness and Training (PR.AT-01)
Simulated Phishing Campaigns: Execute simulated phishing campaigns, report results to management and require remedial training for employees who click.
Role-Based Cybersecurity Training for Specialized Roles (PR.AT-02):
In-Depth Training for Specialized Roles: Develop and deliver targeted, role-based training programs for individuals in these specialized roles. The training should focus on the specific cybersecurity risks and responsibilities associated with their roles. This may include physical and cybersecurity personnel, finance personnel, senior leadership, and any other roles with access to sensitive or business-critical data.
⚠ 5. Incident Response Reporting and Communication
Your Questionnaire Question from RS.CO

Information Sharing Considerations
ISACs (Information Sharing and Analysis Centers):
Enable anonymous threat intelligence sharing
Sector-specific collaboration
Examples: FS-ISAC (Financial), CCTX (Canada)
Internal Notifications:
HR for insider threats
Legal for breach determinations
PR for external communications
Category RS.CO | Subcategories |
|---|---|
Incident Response Reporting and Communication | RS.CO-2: Internal and external stakeholders are notified of incidents RS.CO-3: Information is shared with designated internal and external stakeholders |
RS.CO-2 NIST Implementation Examples
Ex1: Follow the organization's breach notification procedures after discovering a data breach incident, including notifying affected customers
Ex2: Notify business partners and customers of incidents in accordance with contractual requirements
Ex3: Notify law enforcement agencies and regulatory bodies of incidents based on criteria in the incident response plan and management approval
RS.CO-3 NIST Implementation Examples
Ex1: Securely share information consistent with response plans and information sharing agreements
Ex2: Voluntarily share information about an attacker's observed TTPs, with all sensitive data removed, with an Information Sharing and Analysis Center (ISAC)


Ex3: Notify HR when malicious insider activity occurs
Ex4: Regularly update senior leadership on the status of major incidents
Ex5: Follow the rules and protocols defined in contracts for incident information sharing between the organization and its suppliers
Ex6: Coordinate crisis communication methods between the organization and its critical suppliers
Your Recommended Action Plan for RS.CO
Action 7: Develop a Security Incident Response Playbook
Define clear roles and responsibilities for the security team and relevant stakeholders.
Develop clear thresholds for escalating incidents to senior management, legal, and external partners.
Categorize incidents into tiers (e.g., low, medium, high severity) to streamline decision-making and resource allocation.
Establish protocols for engaging:
The Legal team early in the incident investigation process, to support decisions regarding disclosure, reporting, and mitigation actions
An incident response (IR) company on retainer to support high-severity incidents
The Senior Management team
Set up a secure, out-of-band (OOB) communication system for emergency use during incidents.
Action 8: Conduct an Incident Response Tabletop Exercise (TTX)

Test Roles and Responsibilities:
Ensure that all security team members and relevant stakeholders understand their roles in the incident response process.
Validate that the Security, Legal, IT, Incident Response (IR), and Senior Management teams can efficiently coordinate during an incident.
Simulate Incident Severity Tiers:
Use various incident types (e.g., malware, data breach, insider threat) to categorize and manage incidents in accordance with the defined severity tiers.
Test decision-making and resource allocation according to the tiered classification.
Involve Senior Management:
Engage the Senior Management team in the decision-making process during the simulated incident.
Test the communication flow and ensure senior leaders have all the necessary information to make informed decisions.
Test the Out-of-Band (OOB) Communication System:
Establish a scenario where the primary communication systems are compromised.
Test the functionality of the OOB emergency phone call-out system and secure conference bridge, ensuring all stakeholders are able to communicate effectively.
Regularly test the emergency communication system to ensure it is fully operational and known by key personnel.
🔝 Top 5 Risk Gap Closing Actions Recap
Develop, Socialize and Communicate a Supply Chain Risk Management Policy
Develop an Information Security Addendum to be Included in Vendor Contracts
Regularly Perform Supply Chain Risk Assessments, Integrated with the Procurement Process
Implement Centralized Identity Management with Single Sign-On
Enforce Multi-Factor Authentication (MFA)
Provide Basic Cybersecurity Awareness and Training
Develop a Security Incident Response Playbook
Conduct an Incident Response Tabletop Exercise (TTX)
Key Takeaways
People, Process, Technology: All three elements must be considered for effective implementation
MFA is Foundational: If not implemented, make it your first priority
Communicate in Business Terms: Frame security needs in language executives understand
Third-Party Risk is Your Risk: Vendor breaches affect your reputation
Training is Not Optional: Users are always targets, awareness is critical
Test Your Response: Tabletop exercises reveal gaps before real incidents
Clear Policies Enable Enforcement: Comprehensive policies are essential for legal action
Abandoned Projects are Common: Consider maintenance and operations before implementation