Table of Contents
Exam Objectives 📚
Candidates must be able to understand the key concepts related to the NIST Cybersecurity Framework. Students will be able to:
1.2 Summarize key aspects of the NIST Cybersecurity Framework
Purpose of the NIST Cybersecurity Framework
Components of the NIST Cybersecurity Framework
Framework Core
Framework Policies
Implementation Tiers
Six functions of the NIST Cybersecurity Framework
Govern
Identify
Protect
Detect
Respond
Recover
2.2 Explain how categories are utilized with the six functions
2.3 Explain how subcategories are utilized within the six functions
Six Functions 🔄
Each function:
Plays a vital role, working in tandem
Offers a unique perspective and set of activities to strengthen an organization’s cybersecurity defenses
E.g. risk assessment ➡ implementing access controls ➡ deploying IDS ➡ developing Incident Response plans
Holistic Cybersecurity Framework 🌐
Confidently navigate the complex landscape of cyber threats
Identify vulnerabilities ➡ protect critical assets ➡ detect potential breaches ➡ respond effectively to incidents ➡ recover swiftly from disruptions
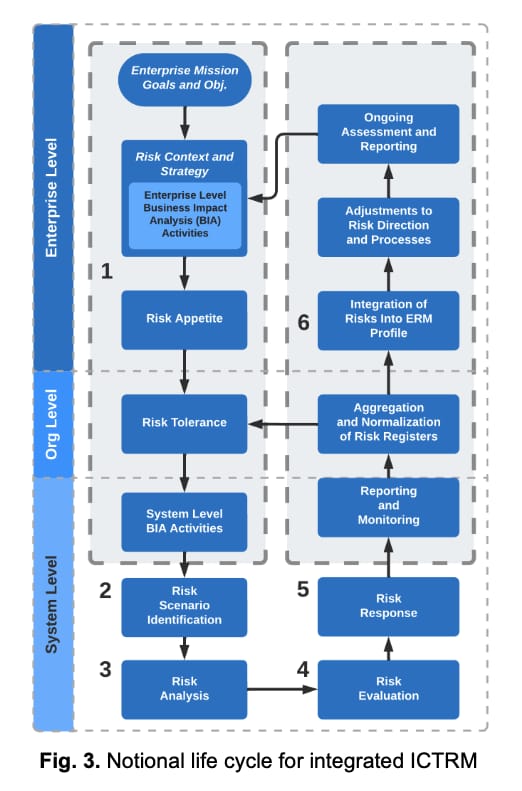
Provides a high-level, strategic view of an orgnaization’s management lifecycle of any given cybersecurity risk
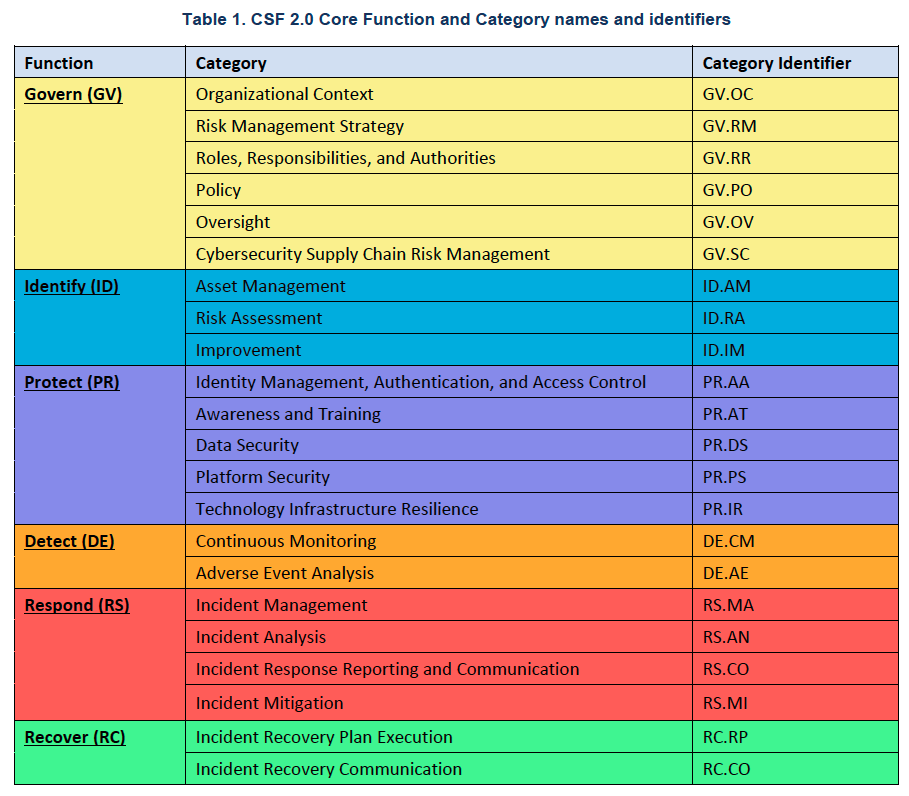
6 Functions ➡ 22 Categories ➡ 106 Subcategories
Each function in the framework is divided into categories.
Each category is labelled using a short code,
E.g. PR.AA signifies that Access to physical and logical Assets is under the PROTECT function
Under each outcome category, there are also subcategories and activities that add a number to the end of a given short code.
E.g. PR.AA-01 represents the activity: “Identities and credentials for authorized users, services, and hardware are managed by the organization”
GOVERN (GV) 📜
Function |
|---|
GOVERN (GV): The organization’s cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored |
Organizational Context (GV.OC)
Category |
|---|
Organizational Context (GV.OC): The circumstances — mission, stakeholder expectations, dependencies, and legal, regulatory, and contractual requirements — surrounding the organization’s cybersecurity risk management decisions are understood |
Subcategory | Implementation Example |
|---|---|
GV.OC-01: The organizational mission is understood and informs cybersecurity risk management | Ex1: Share the organization’s mission (e.g., through vision and mission statements, marketing, and service strategies) to provide a basis for identifying risks that may impede that mission |
GV.OC-02: Internal and external stakeholders are understood, and their needs and expectations regarding cybersecurity risk management are understood and considered | Ex1: Identify relevant internal stakeholders and their cybersecurity-related expectations (e.g., performance and risk expectations of officers, directors, and advisors; cultural expectations of employees) |
GV.OC-03: Legal, regulatory, and contractual requirements regarding cybersecurity — including privacy and civil liberties obligations — are understood and managed | Ex2: Determine a process to track and manage contractual requirements for cybersecurity management of supplier, customer, and partner information |
GV.OC-04: Critical objectives, capabilities, and services that stakeholders depend on or expect from the organization are understood and communicated | Ex2: Determine (e.g., from a business impact analysis) assets and business operations that are vital to achieving mission objectives and the potential impact of a loss (or partial loss) of such operations |
This web server host asset is vital to the Pay Vendor Invoice MTD, RTP and RPO process resilience needs, defined in a Business Impact Analysis:
Subcategory | Implementation Example |
|---|---|
GV.OC-05: Outcomes, capabilities, and services that the organization depends on are understood and communicated | Ex1: Create an inventory of the organization’s dependencies on external resources (e.g., facilities, cloud-based hosting providers) and their relationships to organizational assets and business functions |
Risk Management Strategy (GV.RM)
Category |
|---|
Risk Management Strategy (GV.RM): The organization’s priorities, constraints, risk tolerance and appetite statements, and assumptions are established, communicated, and used to support operational risk decisions |
Subcategory | Implementation Example |
|---|---|
GV.RM-01: Risk management objectives are established and agreed to by organizational stakeholders | Ex1: Update near-term and long-term cybersecurity risk management objectives as part of annual strategic planning and when major changes occur |
GV.RM-02: Risk appetite and risk tolerance statements are established, communicated, and maintained | Ex1: Determine and communicate risk appetite statements that convey expectations about the appropriate level of risk for the organization |
Subcategory | Implementation Example |
|---|---|
GV.RM-03: Cybersecurity risk management activities and outcomes are included in enterprise risk management processes | Ex1: Aggregate and manage cybersecurity risks alongside other enterprise risks (e.g., compliance, financial, operational, regulatory, reputational, safety) |
GV.RM-04: Strategic direction that describes appropriate risk response options is established and communicated | Ex1: Specify criteria for accepting and avoiding cybersecurity risk for various classifications of data |
Subcategory | Implementation Example |
|---|---|
GV.RM-05: Lines of communication across the organization are established for cybersecurity risks, including risks from suppliers and other third parties | Ex1: Determine how to update senior executives, directors, and management on the organization's cybersecurity posture at agreed-upon intervals |
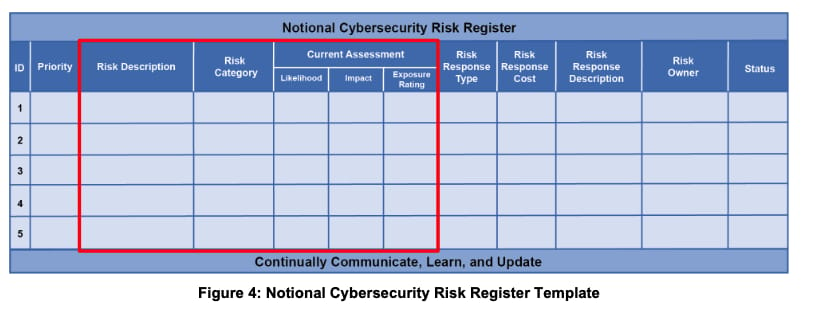
GV.RM-06: A standardized method for calculating, documenting, categorizing, and prioritizing cybersecurity risks is established and communicated | Ex2: Create and use templates (e.g., a risk register) to document cybersecurity risk information (e.g., risk description, exposure, treatment, and ownership) |
GV.RM-07: Strategic opportunities (i.e., positive risks) are characterized and are included in organizational cybersecurity risk discussions | Ex1: Define and communicate guidance and methods for identifying opportunities and including them in risk discussions (e.g., strengths, weaknesses, opportunities, and threats [SWOT] analysis) |
Category |
|---|
Roles, Responsibilities, and Authorities (GV.RR): Cybersecurity roles, responsibilities, and authorities to foster accountability, performance assessment, and continuous improvement are established and communicated |
Subcategory | Implementation Example |
|---|---|
GV.RR-01: Organizational leadership is responsible and accountable for cybersecurity risk and fosters a culture that is risk-aware, ethical, and continually improving | Ex1: Leaders (e.g., directors) agree on their roles and responsibilities in developing, implementing, and assessing the organization's cybersecurity strategy |
GV.RR-02: Roles, responsibilities, and authorities related to cybersecurity risk management are established, communicated, understood, and enforced | Ex3: Include cybersecurity responsibilities and performance requirements in personnel descriptions |
GV.RR-03: Adequate resources are allocated commensurate with the cybersecurity risk strategy, roles, responsibilities, and policies | Ex3: Provide adequate and sufficient people, process, and technical resources to support the cybersecurity strategy |
GV.RR-04: Cybersecurity is included in human resources practices | Ex1: Integrate cybersecurity risk management considerations into human resources processes (e.g., personnel screening, onboarding, change notification, offboarding) |
Policy (GV.PO)
Category |
|---|
Policy (GV.PO): Organizational cybersecurity policy is established, communicated, and enforced |
Subcategory | Implementation Example |
|---|---|
GV.PO-01: Policy for managing cybersecurity risks is established based on organizational context, cybersecurity strategy, and priorities and is communicated and enforced | Ex1: Create, disseminate, and maintain an understandable, usable risk management policy with statements of management intent, expectations, and direction |
GV.PO-02: Policy for managing cybersecurity risks is reviewed, updated, communicated, and enforced to reflect changes in requirements, threats, technology, and organizational mission | Ex1: Update policy based on periodic reviews of cybersecurity risk management results to ensure that policy and supporting processes and procedures adequately maintain risk at an acceptable level |
Oversight (GV.OV)
Category |
|---|
Oversight (GV.OV): Results of organization-wide cybersecurity risk management activities and performance are used to inform, improve, and adjust the risk management strategy |
Subcategory | Implementation Example |
|---|---|
GV.OV-01: Cybersecurity risk management strategy outcomes are reviewed to inform and adjust strategy and direction | Ex1: Measure how well the risk management strategy and risk results have helped leaders make decisions and achieve organizational objectives |
GV.OV-02: The cybersecurity risk management strategy is reviewed and adjusted to ensure coverage of organizational requirements and risks | Ex1: Review audit findings to confirm whether the existing cybersecurity strategy has ensured compliance with internal and external requirements |
GV.OV-03: Organizational cybersecurity risk management performance is evaluated and reviewed for adjustments needed | Ex2: Review key risk indicators (KRIs) to identify risks the organization faces, including likelihood and potential impact |
Cybersecurity Supply Chain Risk Management (GV.SC)
Category |
|---|
Cybersecurity Supply Chain Risk Management (GV.SC): Cyber supply chain risk management processes are identified, established, managed, monitored, and improved by organizational stakeholders |
Subcategory | Implementation Example |
|---|---|
GV.SC-01: A cybersecurity supply chain risk management program, strategy, objectives, policies, and processes are established and agreed to by organizational stakeholders | Ex4: Establish a cross-organizational mechanism that ensures alignment between functions that contribute to cybersecurity supply chain risk management, such as cybersecurity, IT, operations, legal, human resources, and engineering |
GV.SC-02: Cybersecurity roles and responsibilities for suppliers, customers, and partners are established, communicated, and coordinated internally and externally | Ex1: Identify one or more specific roles or positions that will be responsible and accountable for planning, resourcing, and executing cybersecurity supply chain risk management activities |
GV.SC-03: Cybersecurity supply chain risk management is integrated into cybersecurity and enterprise risk management, risk assessment, and improvement processes | Ex1: Identify areas of alignment and overlap with cybersecurity and enterprise risk management |
GV.SC-04: Suppliers are known and prioritized by criticality | Ex1: Develop criteria for supplier criticality based on, for example, the sensitivity of data processed or possessed by suppliers, the degree of access to the organization's systems, and the importance of the products or services to the organization's mission |
GV.SC-05: Requirements to address cybersecurity risks in supply chains are established, prioritized, and integrated into contracts and other types of agreements with suppliers and other relevant third parties | Ex1: Establish security requirements for suppliers, products, and services commensurate with their criticality level and potential impact if compromised |
GV.SC-06: Planning and due diligence are performed to reduce risks before entering into formal supplier or other third-party relationships | Ex1: Perform thorough due diligence on prospective suppliers that is consistent with procurement planning and commensurate with the level of risk, criticality, and complexity of each supplier relationship |
GV.SC-07: The risks posed by a supplier, their products and services, and other third parties are understood, recorded, prioritized, assessed, responded to, and monitored over the course of the relationship | Ex2: Evaluate third parties' evidence of compliance with contractual cybersecurity requirements, such as self-attestations, warranties, certifications, and other artifacts |
Subcategory | Implementation Example |
|---|---|
GV.SC-08: Relevant suppliers and other third parties are included in incident planning, response, and recovery activities | Ex1: Define and use rules and protocols for reporting incident response and recovery activities and the status between the organization and its suppliers |
GV.SC-09: Supply chain security practices are integrated into cybersecurity and enterprise risk management programs, and their performance is monitored throughout the technology product and service life cycle | Ex3: Communicate regularly among cybersecurity risk managers and operations personnel about the need to acquire software patches, updates, and upgrades only from authenticated and trustworthy software providers |
GV.SC-10: Cybersecurity supply chain risk management plans include provisions for activities that occur after the conclusion of a partnership or service agreement | Ex2: Define and implement plans for component end-of-life maintenance support and obsolescence |
IDENTIFY (ID) 🔍
Asset Management (ID.AM)
Category |
|---|
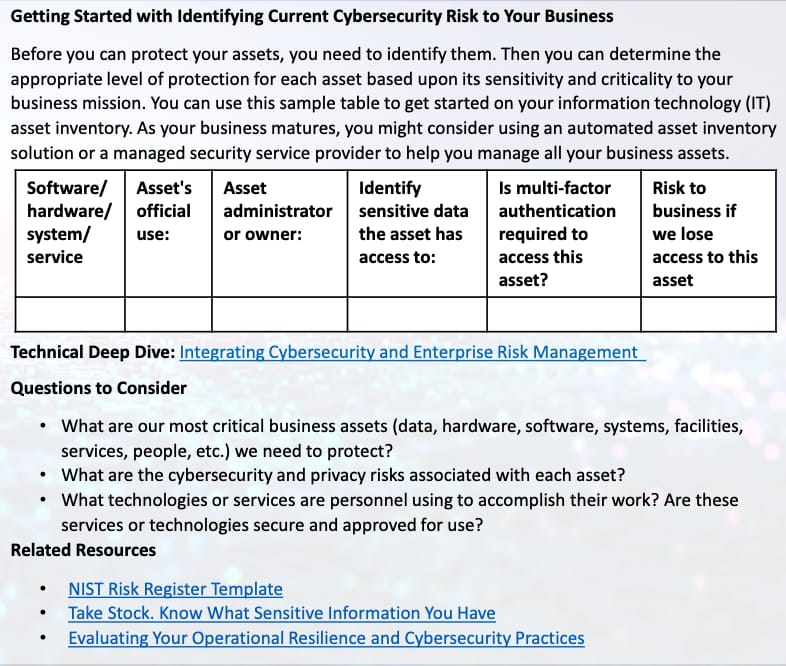
Asset Management (ID.AM): Assets (e.g., data, hardware, software, systems, facilities, services, people) that enable the organization to achieve business purposes are identified and managed consistent with their relative importance to organizational objectives and the organization's risk strategy |
Subcategory | Implementation Example |
|---|---|
ID.AM-01: Inventories of hardware managed by the organization are maintained | Ex1: Maintain inventories for all types of hardware, including IT, IoT, OT, and mobile devices Ex2: Constantly monitor networks to detect new hardware and automatically update inventories |
ID.AM-02: Inventories of software, services, and systems managed by the organization are maintained | Ex1: Maintain inventories for all types of software and services, including commercial-off-the-shelf, open-source, custom applications, API services, and cloud-based applications and services Ex3: Maintain an inventory of the organization's systems |
ID.AM-03: Representations of the organization's authorized network communication and internal and external network data flows are maintained | Ex1: Maintain baselines of communication and data flows within the organization's wired and wireless networks |
Subcategory | Implementation Example |
|---|---|
ID.AM-04: Inventories of services provided by suppliers are maintained | Ex1: Inventory all external services used by the organization, including third-party infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS), and software-as-a-service (SaaS) offerings; APIs; and other externally hosted application services |
ID.AM-05: Assets are prioritized based on classification, criticality, resources, and impact on the mission | Ex1: Define criteria for prioritizing each class of assets |
ID.AM-07: Inventories of data and corresponding metadata for designated data types are maintained | Ex1: Maintain a list of the designated data types of interest (e.g., personally identifiable information, protected health information, financial account numbers, organization intellectual property, operational technology data) |
ID.AM-08: Systems, hardware, software, services, and data are managed throughout their life cycles | Ex1: Integrate cybersecurity considerations throughout the life cycles of systems, hardware, software, and services Ex3: Identify unofficial uses of technology to meet mission objectives (i.e., shadow IT) |
Risk Assessment (ID.RA)
Category |
|---|
Risk Assessment (ID.RA): The cybersecurity risk to the organization, assets, and individuals is understood by the organization |
Subcategory | Implementation Example |
|---|---|
ID.RA-01: Vulnerabilities in assets are identified, validated, and recorded | Ex1: Use vulnerability management technologies to identify unpatched and misconfigured software |
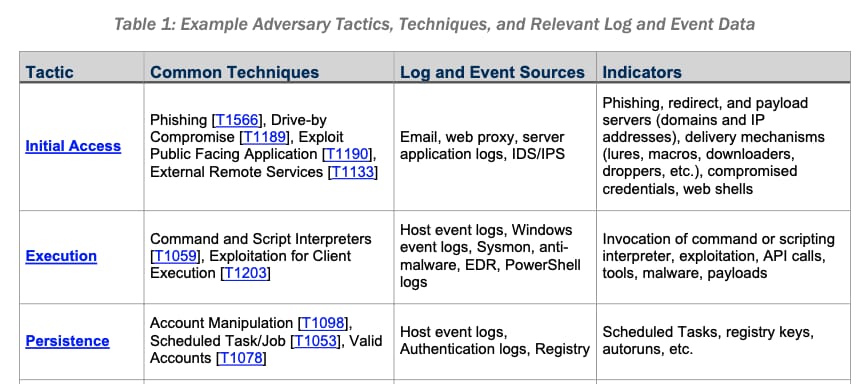
ID.RA-02: Cyber threat intelligence is received from information sharing forums and sources | Ex2: Receive and review advisories from reputable third parties on current threat actors and their tactics, techniques, and procedures (TTPs) |
Subcategory | Implementation Example |
|---|---|
ID.RA-03: Internal and external threats to the organization are identified and recorded | Ex1: Use cyber threat intelligence to maintain awareness of the types of threat actors likely to target the organization and the TTPs they are likely to use |
ID.RA-04: Potential impacts and likelihoods of threats exploiting vulnerabilities are identified and recorded | Ex1: Business leaders and cybersecurity risk management practitioners work together to estimate the likelihood and impact of risk scenarios and record them in risk registers |
Subcategory | Implementation Example |
|---|---|
ID.RA-05: Threats, vulnerabilities, likelihoods, and impacts are used to understand inherent risk and inform risk response prioritization | Ex1: Develop threat models to better understand risks to the data and identify appropriate risk responses |
ID.RA-06: Risk responses are chosen, prioritized, planned, tracked, and communicated | Ex1: Apply the vulnerability management plan's criteria for deciding whether to accept, transfer, mitigate, or avoid risk |
ID.RA-07: Changes and exceptions are managed, assessed for risk impact, recorded, and tracked | Ex1: Implement and follow procedures for the formal documentation, review, testing, and approval of proposed changes and requested exceptions |
ID.RA-08: Processes for receiving, analyzing, and responding to vulnerability disclosures are established | Ex1: Conduct vulnerability information sharing between the organization and its suppliers following the rules and protocols defined in contracts |
ID.RA-09: The authenticity and integrity of hardware and software are assessed prior to acquisition and use | Ex1: Assess the authenticity and cybersecurity of critical technology products and services prior to acquisition and use |
ID.RA-10: Critical suppliers are assessed prior to acquisition | Ex1: Conduct supplier risk assessments against business and applicable cybersecurity requirements, including the supply chain |
Improvement (ID.IM)
Cetegory |
|---|
Improvement (ID.IM): Improvements to organizational cybersecurity risk management processes, procedures and activities are identified across all CSF Functions |
Subcategory | Implementation Example |
|---|---|
ID.IM-01: Improvements are identified from evaluations | Ex2: Invest in third-party assessments or independent audits of the effectiveness of the organization's cybersecurity program to identify areas that need improvement |
ID.IM-02: Improvements are identified from security tests and exercises, including those done in coordination with suppliers and relevant third parties | Ex1: Identify improvements for future incident response activities based on findings from incident response assessments (e.g., tabletop exercises and simulations, tests, internal reviews, independent audits) |
ID.IM-03: Improvements are identified from execution of operational processes, procedures, and activities | Ex2: Annually review cybersecurity policies, processes, and procedures to take lessons learned into account |
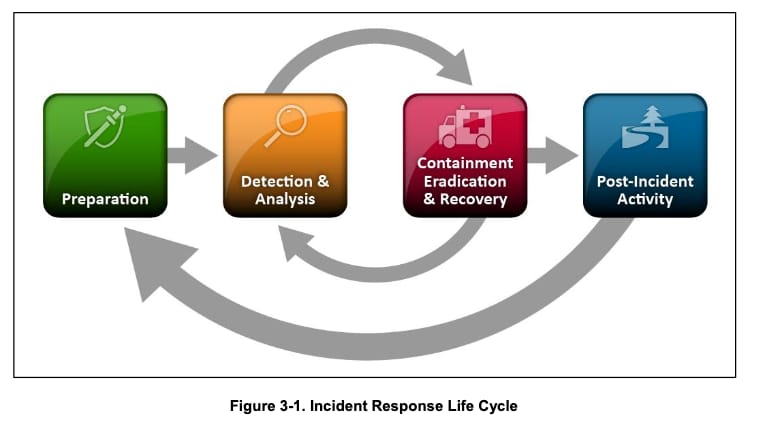
ID.IM-04: Incident response plans and other cybersecurity plans that affect operations are established, communicated, maintained, and improved | Ex1: Establish contingency plans (e.g., incident response, business continuity, disaster recovery) for responding to and recovering from adverse events that can interfere with operations, expose confidential information, or otherwise endanger the organization's mission and viability |
PROTECT (PR) 🛡
Identity Management, Authentication and Access Control (PR.AA)
Category |
|---|
Identity Management, Authentication, and Access Control (PR.AA): Access to physical and logical assets is limited to authorized users, services, and hardware and managed commensurate with the assessed risk of unauthorized access |
Subcategory | Implementation Example |
|---|---|
PR.AA-01: Identities and credentials for authorized users, services, and hardware are managed by the organization | Ex1: Initiate requests for new access or additional access for employees, contractors, and others, and track, review, and fulfill the requests, with permission from system or data owners when needed |
PR.AA-02: Identities are proofed and bound to credentials based on the context of interactions | Ex2: Issue a different credential for each person (i.e., no credential sharing) |
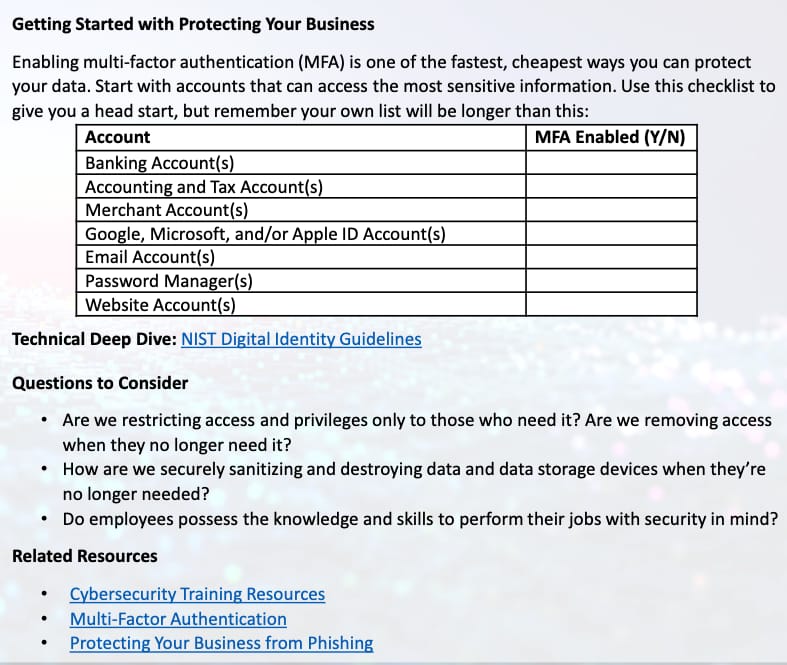
PR.AA-03: Users, services, and hardware are authenticated | Ex1: Require multifactor authentication Ex2: Enforce policies for the minimum strength of passwords, PINs, and similar authenticators |
Subcategory | Implementation Example |
|---|---|
PR.AA-04: Identity assertions are protected, conveyed, and verified | Ex3: Implement standards-based approaches for identity assertions in all contexts, and follow all guidance for the generation (e.g., data models, metadata), protection (e.g., digital signing, encryption), and verification (e.g., signature validation) of identity assertions |
PR.AA-05: Access permissions, entitlements, and authorizations are defined in a policy, managed, enforced, and reviewed, and incorporate the principles of least privilege and separation of duties | Ex1: Review logical and physical access privileges periodically and whenever someone changes roles or leaves the organization, and promptly rescind privileges that are no longer needed |
PR.AA-06: Physical access to assets is managed, monitored, and enforced commensurate with risk | Ex1: Use security guards, security cameras, locked entrances, alarm systems, and other physical controls to monitor facilities and restrict access |
Awareness and Training (PR.AT)
Category |
|---|
Awareness and Training (PR.AT): The organization's personnel are provided with cybersecurity awareness and training so that they can perform their cybersecurity-related tasks |
Subcategory | Implementation Example |
|---|---|
PR.AT-01: Personnel are provided with awareness and training so that they possess the knowledge and skills to perform general tasks with cybersecurity risks in mind | Ex1: Provide basic cybersecurity awareness and training to employees, contractors, partners, suppliers, and all other users of the organization's non-public resources |
PR.AT-02: Individuals in specialized roles are provided with awareness and training so that they possess the knowledge and skills to perform relevant tasks with cybersecurity risks in mind | Ex1: Identify the specialized roles within the organization that require additional cybersecurity training, such as physical and cybersecurity personnel, finance personnel, senior leadership, and anyone with access to business-critical data |
Data Security (PR.DS)
Category |
|---|
Data Security (PR.DS): Data are managed consistent with the organization's risk strategy to protect the confidentiality, integrity, and availability of information |
Subcategory | Implementation Example |
|---|---|
PR.DS-01: The confidentiality, integrity, and availability of data-at-rest are protected | Ex2: Use full disk encryption to protect data stored on user endpoints |
PR.DS-02: The confidentiality, integrity, and availability of data-in-transit are protected | Ex1: Use encryption, digital signatures, and cryptographic hashes to protect the confidentiality and integrity of network communications |
PR.DS-10: The confidentiality, integrity, and availability of data-in-use are protected | Ex1: Remove data that must remain confidential (e.g., from processors and memory) as soon as it is no longer needed |
PR.DS-11: Backups of data are created, protected, maintained, and tested | Ex2: Test backups and restores for all types of data sources at least annually |
Platform Security (PR.PS)
Category |
|---|
Platform Security (PR.PS): The hardware, software (e.g., firmware, operating systems, applications), and services of physical and virtual platforms are managed consistent with the organization's risk strategy to protect their confidentiality, integrity, and availability |
Category |
|---|
Platform Security (PR.PS): The hardware, software (e.g., firmware, operating systems, applications), and services of physical and virtual platforms are managed consistent with the organization's risk strategy to protect their confidentiality, integrity, and availability |
Subcategory | Implementation Example |
|---|---|
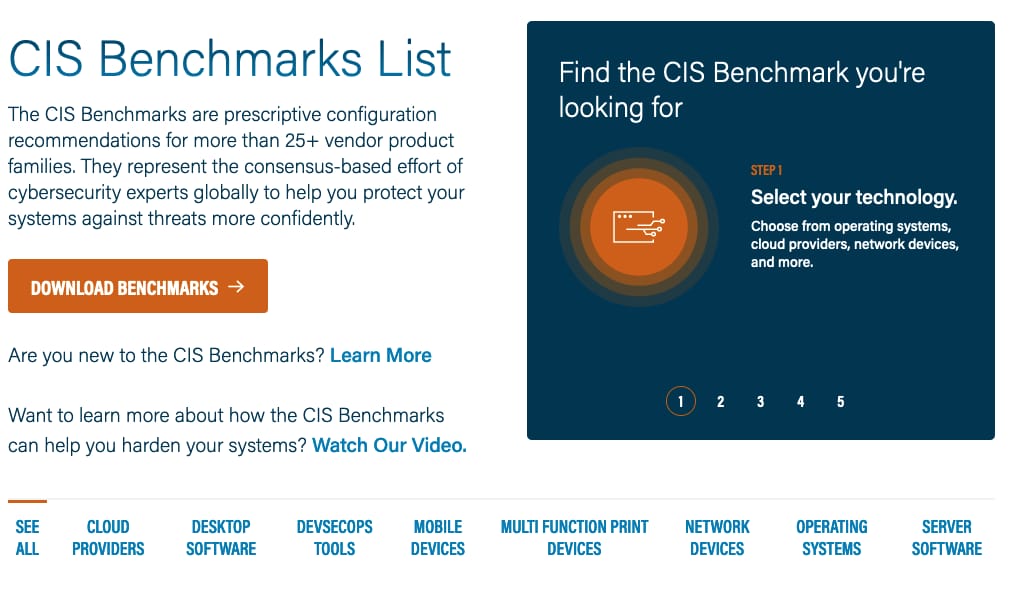
PR.PS-01: Configuration management practices are established and applied | Ex1: Establish, test, deploy, and maintain hardened baselines that enforce the organization's cybersecurity policies and provide only essential capabilities (i.e., principle of least functionality) |
Subcategory | Implementation Example |
|---|---|
PR.PS-02: Software is maintained, replaced, and removed commensurate with risk | Ex1: Perform routine and emergency patching within the timeframes specified in the vulnerability management plan |
PR.PS-03: Hardware is maintained, replaced, and removed commensurate with risk | Ex1: Replace hardware when it lacks needed security capabilities or when it cannot support software with needed security capabilities |
PR.PS-04: Log records are generated and made available for continuous monitoring | Ex2: Configure log generators to securely share their logs with the organization's logging infrastructure systems and services |
PR.PS-05: Installation and execution of unauthorized software are prevented | Ex1: When risk warrants it, restrict software execution to permitted products only or deny the execution of prohibited and unauthorized software |
PR.PS-06: Secure software development practices are integrated, and their performance is monitored throughout the software development life cycle | Ex1: Protect all components of organization-developed software from tampering and unauthorized access |
Technology Infrastructure Resilience (PR.IR)
Category |
|---|
Technology Infrastructure Resilience (PR.IR): Security architectures are managed with the organization's risk strategy to protect asset confidentiality, integrity, and availability, and organizational resilience |
Subcategory | Implementation Example |
|---|---|
PR.IR-01: Networks and environments are protected from unauthorized logical access and usage | Ex1: Logically segment organization networks and cloud-based platforms according to trust boundaries and platform types (e.g., IT, IoT, OT, mobile, guests), and permit required communications only between segments |

Subcategory | Implementation Example |
|---|---|
PR.IR-02: The organization's technology assets are protected from environmental threats | Ex1: Protect organizational equipment from known environmental threats, such as flooding, fire, wind, and excessive heat and humidity |
PR.IR-03: Mechanisms are implemented to achieve resilience requirements in normal and adverse situations | Ex1: Avoid single points of failure in systems and infrastructure |
PR.IR-04: Adequate resource capacity to ensure availability is maintained | Ex1: Monitor usage of storage, power, compute, network bandwidth, and other resources |
DETECT (DE) ⚠
Continuous Monitoring
Category |
|---|
Continuous Monitoring (DE.CM): Assets are monitored to find anomalies, indicators of compromise, and other potentially adverse events |
Subcategory | Implementation Example |
|---|---|
DE.CM-01: Networks and network services are monitored to find potentially adverse events | Ex1: Monitor DNS, BGP, and other network services for adverse events |

Subcategory | Implementation Example |
|---|---|
DE.CM-02: The physical environment is monitored to find potentially adverse events | Ex1: Monitor logs from physical access control systems (e.g., badge readers) to find unusual access patterns (e.g., deviations from the norm) and failed access attempts |
DE.CM-03: Personnel activity and technology usage are monitored to find potentially adverse events | Ex1: Use behavior analytics software to detect anomalous user activity to mitigate insider threats |
DE.CM-06: External service provider activities and services are monitored to find potentially adverse events | Ex1: Monitor remote and onsite administration and maintenance activities that external providers perform on organizational systems |
DE.CM-09: Computing hardware and software, runtime environments, and their data are monitored to find potentially adverse events | Ex1: Monitor email, web, file sharing, collaboration services, and other common attack vectors to detect malware, phishing, data leaks and exfiltration, and other adverse events |
Adverse Event Analysis (DE.AE)
Category |
|---|
Adverse Event Analysis (DE.AE): Anomalies, indicators of compromise, and other potentially adverse events are analyzed to characterize the events and detect cybersecurity incidents |
Subcategory | Implementation Example |
|---|---|
DE.AE-02: Potentially adverse events are analyzed to better understand associated activities | Ex1: Use security information and event management (SIEM) or other tools to continuously monitor log events for known malicious and suspicious activity |
DE.AE-03: Information is correlated from multiple sources | Ex2: Use event correlation technology (e.g., SIEM) to collect information captured by multiple sources |
Subcategory | Implementation Example |
|---|---|
DE.AE-04: The estimated impact and scope of adverse events are understood | Ex1: Use SIEMs or other tools to estimate impact and scope, and review and refine the estimates |
DE.AE-06: Information on adverse events is provided to authorized staff and tools | Ex1: Use cybersecurity software to generate alerts and provide them to the security operations center (SOC), incident responders, and incident response tools |
DE.AE-07: Cyber threat intelligence and other contextual information are integrated into the analysis | Ex3: Rapidly acquire and analyze vulnerability disclosures for the organization's technologies from suppliers, vendors, and third-party security advisories |
DE.AE-08: Incidents are declared when adverse events meet the defined incident criteria | Ex1: Apply incident criteria to known and assumed characteristics of activity in order to determine whether an incident should be declared |
RESPOND (RS) 🚨
Incident Management (RS.MA)
Category |
|---|
Incident Management (RS.MA): Responses to detected cybersecurity incidents are managed |
Subcategory | Implementation Example |
|---|---|
RS.MA-01: The incident response plan is executed in coordination with relevant third parties once an incident is declared | Ex3: Designate an incident lead for each incident |
Subcategory | Implementation Example |
|---|---|
RS.MA-02: Incident reports are triaged and validated | Ex2: Apply criteria to estimate the severity of an incident |
Subcategory | Implementation Example |
|---|---|
RS.MA-03: Incidents are categorized and prioritized | Ex2: Prioritize incidents based on their scope, likely impact, and time-critical nature |
RS.MA-04: Incidents are escalated or elevated as needed | Ex2: Coordinate incident escalation or elevation with designated internal and external stakeholders |
RS.MA-05: The criteria for initiating incident recovery are applied | Ex1: Apply incident recovery criteria to known and assumed characteristics of the incident to determine whether incident recovery processes should be initiated |
Incident Analysis (RS.AN)
Category |
|---|
Incident Analysis (RS.AN): Investigations are conducted to ensure effective response and support forensics and recovery activities |
Subcategory | Implementation Example |
|---|---|
RS.AN-03: Analysis is performed to establish what has taken place during an incident and the root cause of the incident | Ex1: Determine the sequence of events that occurred during the incident and which assets and resources were involved in each event Ex2: Attempt to determine what vulnerabilities, threats, and threat actors were directly or indirectly involved in the incident Ex3: Analyze the incident to find the underlying, systemic root causes |
Subcategory | Implementation Example |
|---|---|
RS.AN-06: Actions performed during an investigation are recorded, and the records' integrity and provenance are preserved | Ex2: Require the incident lead to document the incident in detail and be responsible for preserving the integrity of the documentation and the sources of all information being reported |
Subcategory | Implementation Example |
|---|---|
RS.AN-07: Incident data and metadata are collected, and their integrity and provenance are preserved | Ex1: Collect, preserve, and safeguard the integrity of all pertinent incident data and metadata (e.g., data source, date/time of collection) based on evidence preservation and chain-of-custody procedures |
RS.AN-08: An incident's magnitude is estimated and validated | Ex1: Review other potential targets of the incident to search for indicators of compromise and evidence of persistence |
Incident Response Reporting and Communication (RS.CO)
Category |
|---|
Incident Response Reporting and Communication (RS.CO): Response activities are coordinated with internal and external stakeholders as required by laws, regulations, or policies |
Subcategory | Implementation Example |
|---|---|
RS.CO-02: Internal and external stakeholders are notified of incidents | Ex1: Follow the organization's breach notification procedures after discovering a data breach incident, including notifying affected customers |
RS.CO-03: Information is shared with designated internal and external stakeholders | Ex1: Securely share information consistent with response plans and information sharing agreements |
Incident Mitigation (RS.MI)
Category |
|---|
Incident Mitigation (RS.MI): Activities are performed to prevent expansion of an event and mitigate its effects |
Subcategory | Implementation Example |
|---|---|
RS.MI-01: Incidents are contained | Ex1: Cybersecurity technologies (e.g., antivirus software) and cybersecurity features of other technologies (e.g., operating systems, network infrastructure devices) automatically perform containment actions Ex2: Allow incident responders to manually select and perform containment action |
RS.MI-02: Incidents are eradicated | Ex1: Cybersecurity technologies and cybersecurity features of other technologies (e.g., operating systems, network infrastructure devices) automatically perform eradication actions Ex2: Allow incident responders to manually select and perform eradication action |
RECOVER (RC) 🛠
Incident Recovery Plan Execution (RC.RP)
Category |
|---|
Incident Recovery Plan Execution (RC.RP): Restoration activities are performed to ensure operational availability of systems and services affected by cybersecurity incidents |
Subcategory | Implementation Example |
|---|---|
RC.RP-01: The recovery portion of the incident response plan is executed once initiated from the incident response process | Ex1: Begin recovery procedures during or after incident response processes |
RC.RP-02: Recovery actions are selected, scoped, prioritized, and performed | Ex1: Select recovery actions based on the criteria defined in the incident response plan and available resources |
RC.RP-03: The integrity of backups and other restoration assets is verified before using them for restoration | Ex1: Check restoration assets for indicators of compromise, file corruption, and other integrity issues before use |
RC.RP-04: Critical mission functions and cybersecurity risk management are considered to establish post-incident operational norms | Ex2: Work with system owners to confirm the successful restoration of systems and the return to normal operations |
RC.RP-05: The integrity of restored assets is verified, systems and services are restored, and normal operating status is confirmed | Ex1: Check restored assets for indicators of compromise and remediation of root causes of the incident before production use |
RC.RP-06: The end of incident recovery is declared based on criteria, and incident-related documentation is completed | Ex1: Prepare an after-action report that documents the incident itself, the response and recovery actions taken, and lessons learned |
Incident Response Reporting and Communication (RC.CO)
Category |
|---|
Incident Response Reporting and Communication (RS.CO): Response activities are coordinated with internal and external stakeholders as required by laws, regulations, or policies |
Subcategory | Implementation Example |
|---|---|
RC.CO-03: Recovery activities and progress in restoring operational capabilities are communicated to designated internal and external stakeholders | Ex1: Securely share recovery information, including restoration progress, consistent with response plans and information sharing agreements |
RC.CO-04: Public updates on incident recovery are shared using approved methods and messaging | Ex1: Follow the organization's breach notification procedures for recovering from a data breach incident |
Conclusion and TouchPoints ✅
6 functions ➡ 22 Categories ➡ 106 Subcategories
It is important that you can relate a given subcategory or activity to the appropriate category and the category to the appropriate function.
A/CCRF Exam vs Real Life
You will not be asked to expand a given short code from memory, such as DE, for the exam, but it would be fair to ask you to identify the function or category to which DE.AE-03 is linked.
💡 Just know that DE is the detect function and AE is the Adverse Event Analysis category.
When you are working in the field as a practitioner, you can always carry a copy of the NIST Cybersecurity Framework version 2.0 to reference the individual subcategories and activities, as needed.
It is important to remember that within the 22 categories are specific subcategories and their corresponding activities, such as:
Inventorying physical devices and systems
Mapping organizational communication and data flows
Establishing cybersecurity roles and responsibilities
These 106 subcategories and activities enable organizations to prioritize resources, understand their organizational context, assess risks, and develop effective risk management strategies.
As you work in the field, you will find that you don’t need to use all 106 subcategories and outcomes that we covered in this section with every organization.
Instead, it is more important that you review them all during your engagements and select the activities that best align with organizational objectives and overall risk management strategies being pursued.