🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
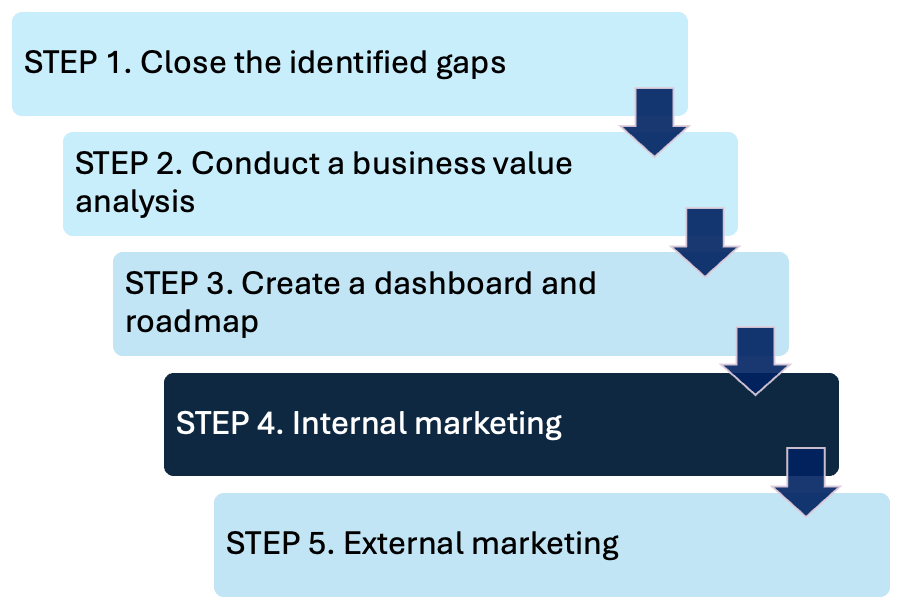
13.22-23 📈 Step 2: Business value analysis

Even up to a couple years ago everyone always looked at cyber as a cost center: it was something that cost our business money it wasn't something that enabled business functionality that made us money.

Speed of Trust Key Principles
Trust leads to speed and lower costs
In a high-trust environment, people collaborate more effectively, and decisions are made faster, with less bureaucracy. Conversely, in a low-trust environment, processes slow down, and costs increase due to inefficiencies, misunderstandings, and undue friction (e.g. from the cybersecurity team).
The economics of trust
Covey emphasizes the "trust tax" and "trust dividend" concepts. A low-trust environment incurs a "tax" in the form of inefficiencies, whereas a high-trust environment yields a "dividend" through improved relationships, reduced friction, and faster execution.
13 specific ways you can build and sustain trust
Talk straight
Demonstrate respect
Create transparency
Right wrongs
Show loyalty
Deliver results
Get better (continuous improvement)
Confront reality
Clarify expectations
Practice accountability
Listen first
Keep commitments
Extend trust (while balancing with appropriate caution)
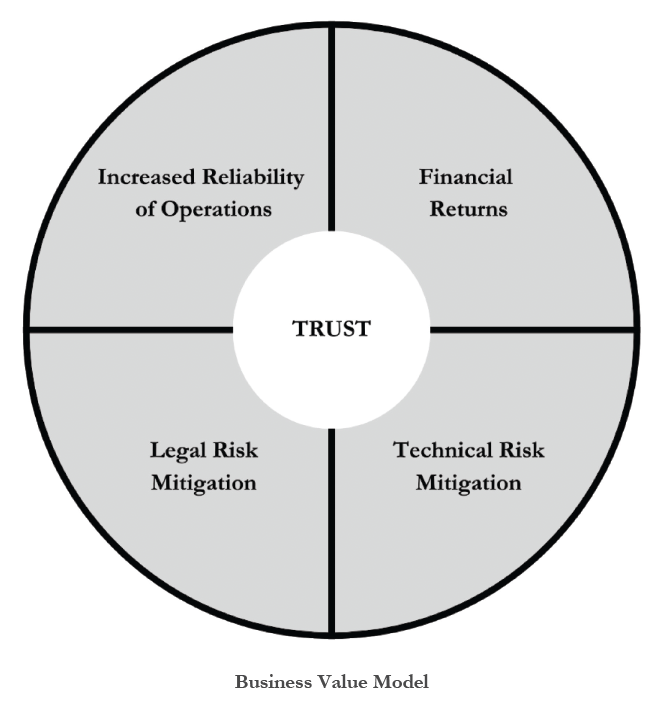
13.23 Business Value Model
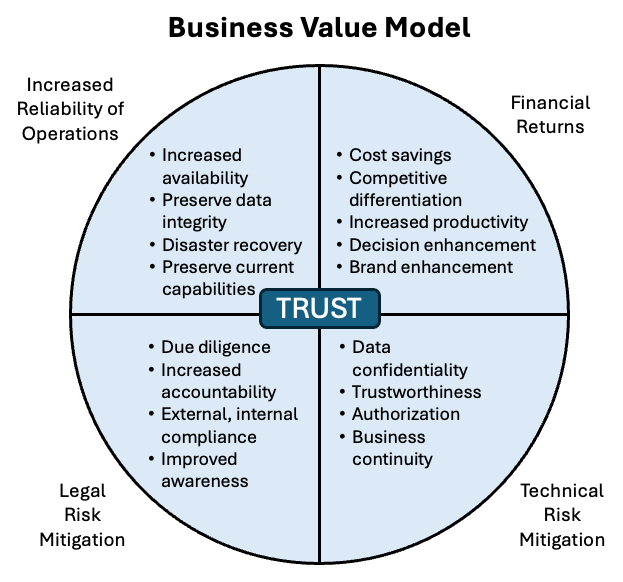
Financial Returns
1. Cost Savings
Prevention of Data Breaches: Implementing strong cybersecurity practices reduces the likelihood of costly data breaches, which can result in significant financial penalties, legal fees, and remediation costs.
Example: $75 million ransom paid to Dark Angels gang (2024)
Operational Downtime Reduction: Protecting systems from ransomware, malware, and other attacks ensures business continuity, avoiding the downtime that could disrupt operations and lead to revenue loss.

Year | Company | Security Incident | Cost |
2020 | Cognizant | Ransomware Attack | $50-$70 million |
2021 | Colonial Pipeline | Ransomware Incident | Undisclosed (Significant Impact) |
2017 | Maersk | NotPetya Ransomware Attack | $300 million |
2013 | Target | POS Malware Breach | Undisclosed |
Insurance Premium Reduction: Businesses with robust cybersecurity measures can often negotiate lower premiums on cyber insurance policies.
2. Competitive Differentiation
Trust and Reputation
Trust centres
Compliance with Industry Standards
SOC2 reports, ISO27k certifications
Request for Information (RFI), Request for Proposals (RFP)
Security questionnaires

Regulatory Compliance Examples:
SEC requirements and enforcement actions
SolarWinds case precedent
3. Increased Productivity
Reduced Downtime: With strong cybersecurity protocols in place, systems are less likely to suffer from disruptions due to attacks, leading to less downtime and higher productivity.
Automation and Streamlining: from centralizing processes into secure, modern solutions
Example: Identity and Access Management (IAM) Evolution
Legacy Process Issues:
Manually provisioning and de-provisioning user accounts,
Manually managing user access to systems, and ensuring that permissions were updated when roles or responsibilities changed
Slow, inefficient, and prone to errors, especially with scale
Centralized, Automated IAM Benefits:
Automated User Provisioning and De-provisioning: New employee accounts are automatically created when a user joins the organization, and access is terminated immediately when they leave, based on HR system triggers.
Single Sign-On (SSO): Centralizes authentication so that users can access multiple applications and services with a single set of credentials, simplifying user experience and enhancing productivity.
Self-Service Password Reset (SSPR): Employees can reset their passwords without contacting IT, reducing downtime and freeing IT resources.
Role-Based Access Control (RBAC): Automatically assigns access permissions based on the employee's role, ensuring the principle of least privilege.
4. Decision Enhancement
Informed Risk Management: A well-structured cybersecurity strategy helps businesses assess and manage risks better, supporting leadership in making informed decisions about investments, partnerships, and new ventures.
Data Integrity: Cybersecurity ensures the integrity of critical data, enabling businesses to make decisions based on accurate, unaltered information. Secure data collection and storage practices protect against data corruption or theft, which could lead to poor business decisions.
5. Brand Enhancement
Customer Confidence: A strong cybersecurity posture demonstrates to customers that their data is safe, which enhances brand loyalty and customer retention.
Positive Public Perception: Being known for robust cybersecurity practices can enhance the overall image of the company, positioning it as responsible and forward-thinking, which is especially valuable in industries prone to data breaches.
Avoidance of Negative Publicity: By avoiding high-profile security breaches, companies maintain a positive brand image, preventing the negative media attention and loss of customer trust that often follows a breach.
Technical Risk Mitigation
1. Data Confidentiality
Encryption of data at rest and in transit
Access controls to restrict data exposure
Data masking or tokenization for sensitive information
Network segmentation to isolate critical data
Multi-factor authentication (MFA) for data access

2. Trustworthiness
Digital certificates for secure communication
Secure software development practices (e.g., code signing)
Regular vulnerability assessments to ensure systems are trustworthy
Data integrity checks (e.g., hashing algorithms)

Role-Based Access Control (RBAC) or Attribute-Based Access Control (ABAC)
Least privilege enforcement to limit permissions
Privileged Access Management (PAM) for critical system access
Session timeout and automatic logouts for inactive users
Audit trails for monitoring and validating access rights
4. Business Continuity
Disaster recovery plans (DRP) for system and data recovery
Redundancy in critical systems (e.g., failover servers)
Regular backups and backup integrity checks
Business impact analysis (BIA) to prioritize recovery
Cloud failover solutions for rapid scalability and recovery
Increased Reliability of Operations
Key Focus Areas:
Increased availability
Preservation of data integrity
Disaster recovery capabilities
Preservation of current capabilities
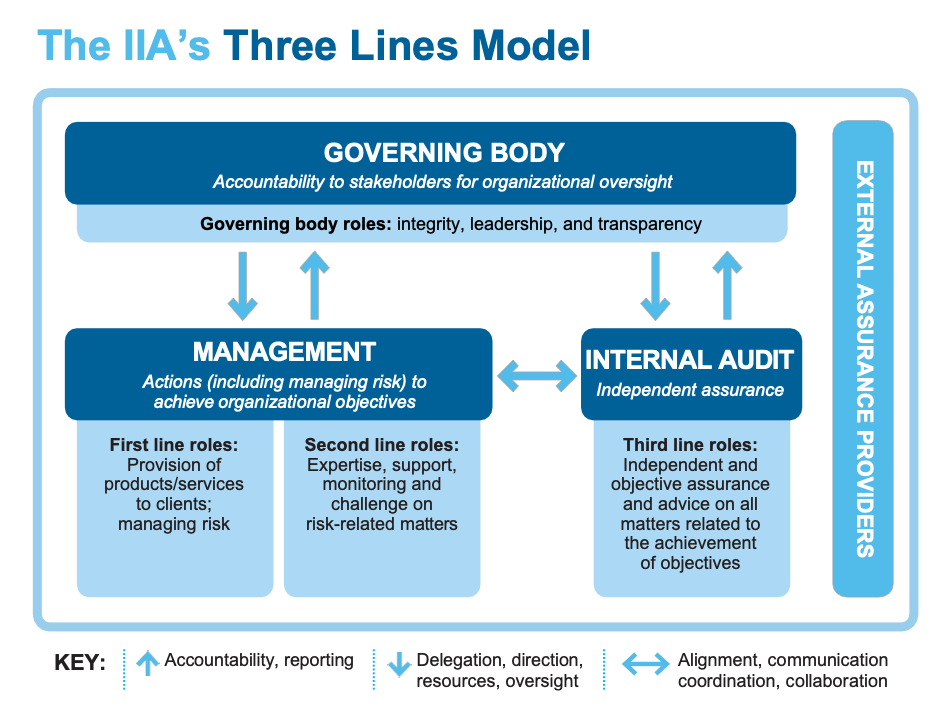
Legal Risk Mitigation
Due Diligence and Due Care
Due diligence is establishing a plan, policy, and processes to protect the interests of the organization.
Due care is practising the individual activities that maintain the due diligence effort.
For example, due diligence is developing a formalized security structure containing a security policy, standards, baselines, guidelines, and procedures. Due care is the continued application of this security structure into the IT infrastructure of an organization.
In today’s business environment, prudence is mandatory. Showing due diligence and due care is the only way to disprove negligence and occurrence of loss. Senior management must show due care and due diligence to reduce their culpability and liability when a loss occurs.
Key Legal Risk Mitigation Components
Increased Accountability: When accountability is clearly defined and enforced within an organization, individuals are held responsible for their actions, including compliance with legal requirements. This reduces the risk of non-compliance, as employees understand their responsibilities and the consequences of failure. Increased accountability can also improve an organization’s defense if legal action is taken, showing that proper oversight and controls were in place.
External and Internal Compliance: Compliance with both internal policies and external regulations ensures that the organization operates within the bounds of the law. This reduces the risk of legal penalties, fines, or lawsuits due to regulatory breaches. Demonstrating compliance through audits and documentation can also help defend against claims of negligence or wrongdoing.
Improved Awareness: Raising awareness of legal obligations and risks across an organization ensures that employees are informed and vigilant about potential issues. Training and communication about legal risks help prevent accidental breaches, non-compliance, or misconduct. When employees are more aware of legal expectations, they can avoid actions that might expose the organization to legal consequences.
13.24 🧭 Step 3: Create a dashboard and roadmap
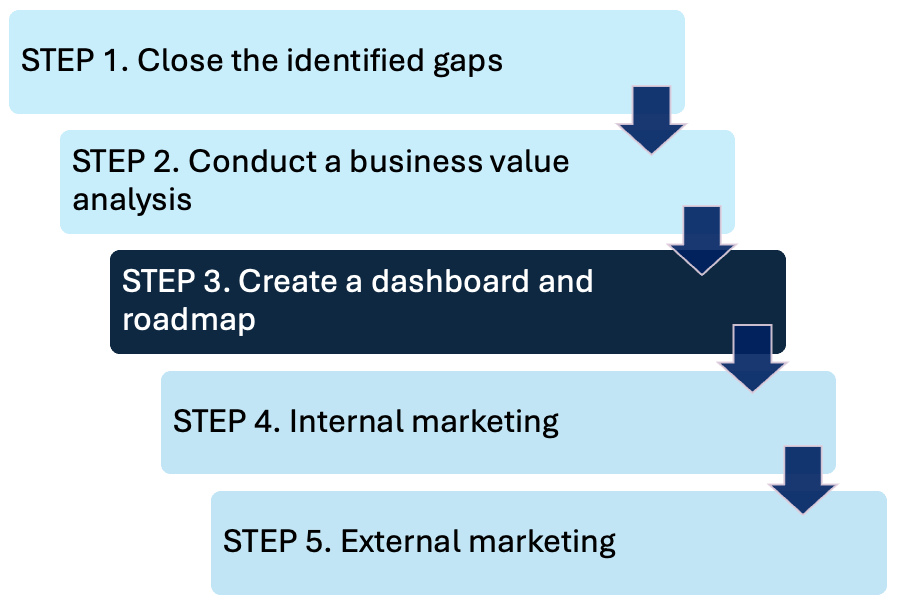
Internal Marketing
Secure buy-in from key internal stakeholders:
Clarify the goals and objectives
Communicate the costs of mitigations, including financial investment and time commitment
Articulate the intended outcomes and purpose behind the chosen approach
Establish how you will measure success
Define KPIs to create transparency and provide a clear benchmark for evaluating effectiveness of the initiatives
Communicate the timeline with milestones
Designate responsible leaders or champions
External Marketing
Have a clear and comprehensive cybersecurity narrative, if needed for key external stakeholders:
Large customers
Investors
A state regulator
Even a judge or jury
13.25 🏢 Step 4: Conduct internal marketing
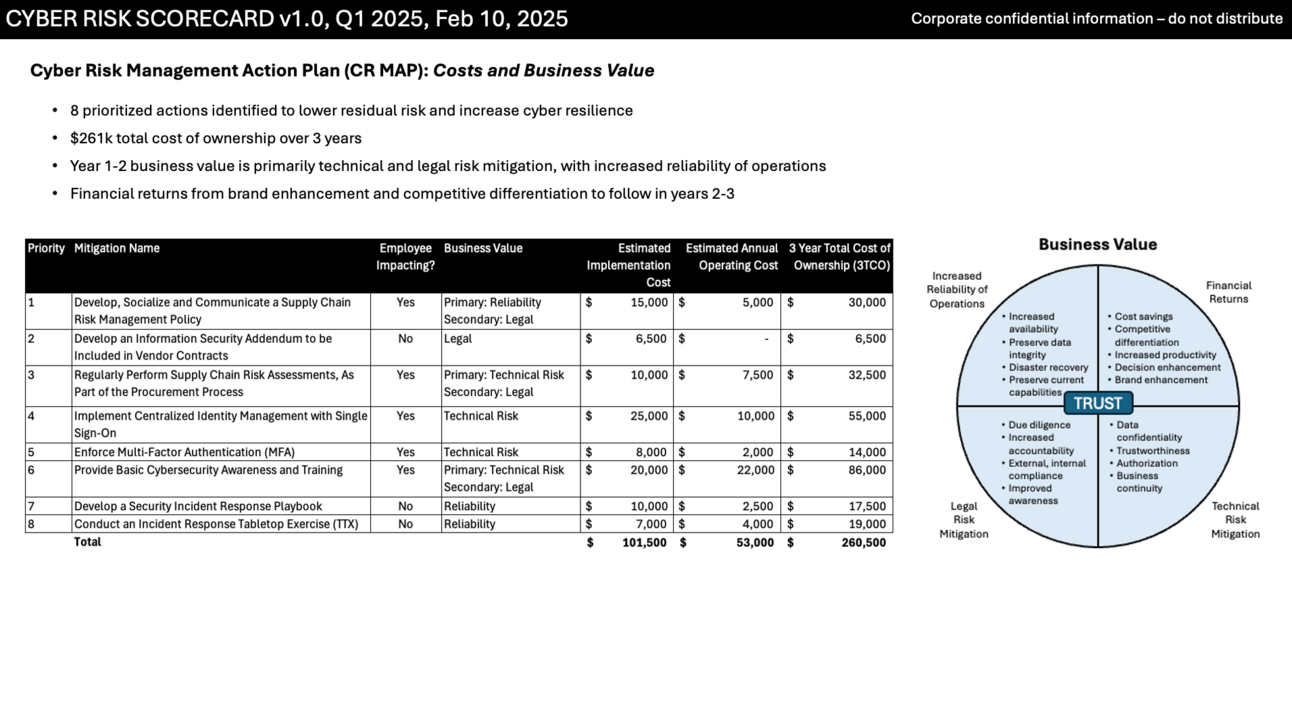
Cyber Risk Scorecard v1.0, Q1 2025, Feb 10, 2025



13.26 Internal Marketing Key Success Factors
Secure Buy-In from Key Stakeholders
Force Field Analysis
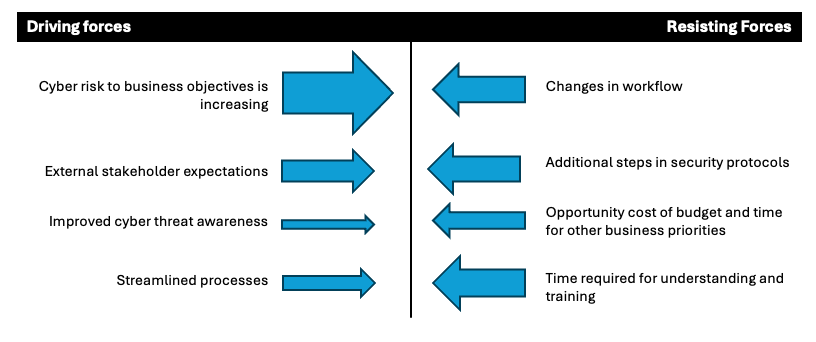
Strengthen driving forces with:
Involving cross functional teams in the CR MAP process
Regularly communicating CR MAP progress
Highlighting the business value and emphasis on reasonable cyber resilience
Providing support during transitions
Reduce resisting forces with:
Prioritize
Control the rate of change
Keep it simple
Adequate training
Introducing scalable processes
Showing executive team and project champion support
Stakeholder Analysis
Power/Interest | Category | Engagement Strategy |
|---|---|---|
High Power, High Interest | Key players | Fully engage (e.g., cross-functional cyber risk experts, middle managers) |
High Power, Low Interest | Keep satisfied | Don't overload with details |
Low Power, High Interest | Keep informed | Regular updates |
Low Power, Low Interest | Minimal effort | Basic communication only |

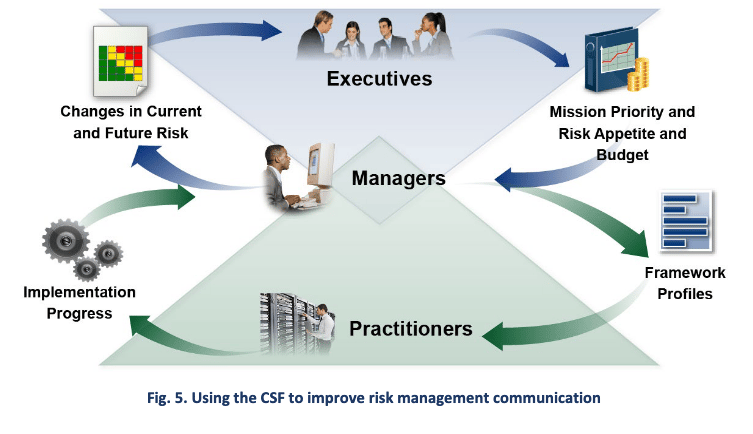
Data for Decision Making - Essential Elements:
What: Top 5 risks from threat and vulnerability perspectives
Why: CSF functions and categories analysis
When: Timeline with Gantt chart
How Much: 3-Year Total Cost of Ownership (3TCO)
Who: Roles and responsibilities in action register
Key Performance Indicators (KPIs)
Create transparency
Provide clear benchmarks
Evaluate initiative effectiveness
Report quarterly at checkpoints
13.27 🌐 Step 5: Conduct external marketing

Summary Scorecard Best Practices
Security Measures:
Exclude organization name and logo
Include "Confidential Information – Do Not Distribute" label
Add publication date and version number
Use anonymous tracking codes (e.g., WHJ-597)
Require NDAs for external viewers
Apply need-to-know principle for access
Content Elements:
Overall Summary chart
Top Five Cyber Risks chart
Radar diagram showing gaps
CSF category scores (actual vs. target)
Business value justification
3TCO analysis
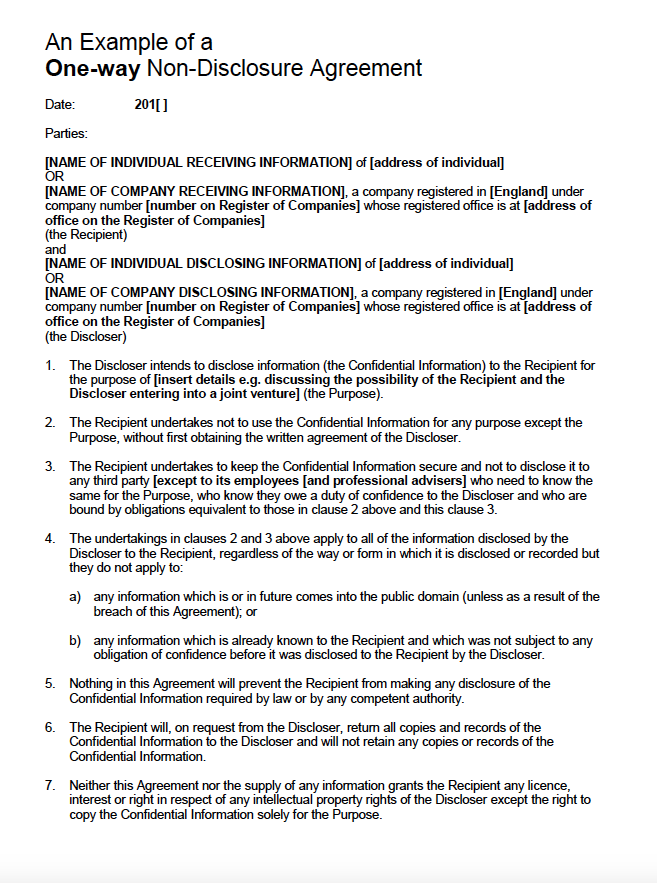
Legal Protections
Use signed Non-Disclosure Agreements (NDAs)
Work under attorney-client privilege where appropriate
Document all decisions and rationale for future reference
Summary Scorecard

NDA
13.28 ✅ Conclusion and Touchpoints
Prioritize Top Cyber Risks and Develop a Plan: By identifying and prioritizing your company’s top cyber risks, and developing a plan to manage them, you’ve taken crucial steps to protect your organization and its stakeholders.
Gain Buy-in: Secure support from decision-makers and employees, while ensuring the necessary budget is allocated for effective implementation.
Consequences of Inaction: Without these proactive changes, your company risks data loss, resource depletion, reputational damage, and even potential physical harm.
Transparent Communication: Learn from companies like AsusTek—many failed to communicate their cybersecurity breaches publicly. Use this plan to reduce breach risks and leverage incidents as opportunities to build trust with your customers.
Build Customer Confidence: By handling breaches transparently and effectively, you show your commitment to cybersecurity, strengthening customer confidence.
Ongoing Process: Cyber risk management isn’t a one-time effort. Continuously executing and improving your plan is key to long-term protection.
More Than Tools: Cybersecurity goes beyond tools and technology; it’s about consistently implementing best practices and staying ahead of risks.
Stay Vigilant: By staying vigilant and proactive, you can safeguard your organization, maintain customer trust, and minimize the impact of cyber threats.
Key Takeaways
Timeline: 60-Day Engagement Structure
Month 1: Risk identification through fieldwork
Month 2: Action planning and cost analysis
Day 60+: Executive approval and implementation begins
4 Change Management Essentials
Force Field Analysis - Balance what drives vs. resists change
Stakeholder Mapping - Engage based on power/interest levels
Clear Vision - Make the compelling business case
Measurable Results - KPIs prove value delivered
External Communication Must-Haves
One-page executive scorecard
Visual radar diagrams
Anonymous coding for security
NDAs for sensitive data
Version control for audit trails
Smart Implementation Approach
Two-Track System:
Track 1: Invisible backend changes
Track 2: Employee-facing changes requiring training
Prioritize Based On:
Size of security gaps
Business impact potential
Available resources
Organization's change capacity
Critical Success Factors
Executive sponsorship is non-negotiable
Data drives decisions (3TCO, risk scores, business value)
Speak business language, not tech jargon
Transparency builds trust through regular updates
Quarterly checkpoints to measure, adjust, and celebrate wins
Document everything for legal protection and future reference