Table of Contents
13.8 Backgrounder on Supply Chain Risk Management
Key Learning Objectives
Understand the shared responsibility model in supply chain risk management
Develop comprehensive supply chain risk management policies
Create effective information security addendums for vendor contracts
Integrate supply chain risk assessments into procurement processes
Apply NIST CSF subcategories GV.SC-01, GV.SC-05, and GV.SC-07
✍️ Developing an Action Plan


✋ Five Steps to Developing an Action Plan

📋 STEP 1: Close the identified gaps



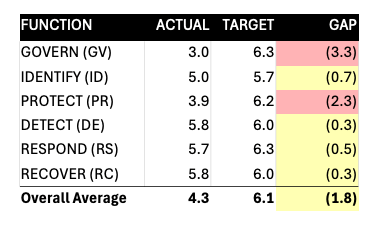

🚨1. Cybersecurity Supply Chain Risk Management (GV.SC) Gaps
Core Principle: Cyber supply chain risk management processes are identified, established, managed, monitored, and improved by organizational stakeholders.
Key Considerations:
Contractual Limitations
Shared Responsibility Model
Platform provider responsibilities (e.g., AWS, Azure, Google Cloud)
Application provider responsibilities (e.g., SaaS vendors)
End user responsibilities
Risk Cascade Example:
Credit card processor → Cloud provider → Customers → End consumers
Security incident at any level impacts entire chain
Reputation damage ripples through supply chain

🗣 Communicate expectations to customers (like with the AWS shared responsibility model) in a Master Services Agreement or similar contract
Shared Responsibility Model
Cloud Service Provider Responsible For: Security OF the cloud
Physical infrastructure
Network controls
Hypervisor
Customer Responsible For: Security IN the cloud
Data encryption
Access management
Application security
Your Questionnaire Questions from SC-01
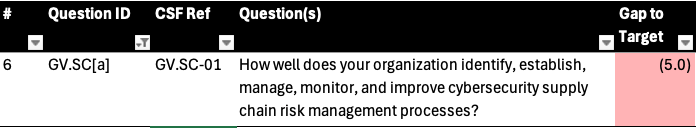
Subcategory GV.SC-01: |
|---|
A cybersecurity supply chain risk management program, strategy, objectives, policies, and processes are established and agreed to by organizational stakeholders |
GV.SC-01 NIST Implementation Examples
Ex1: Establish a strategy that expresses the objectives of the cybersecurity supply chain risk management program
Ex2: Develop the cybersecurity supply chain risk management program, including a plan (with milestones), policies, and procedures that guide implementation and improvement of the program, and share the policies and procedures with the organizational stakeholders
Ex3: Develop and implement program processes based on the strategy, objectives, policies, and procedures that are agreed upon and performed by the organizational stakeholders
Ex4: Establish a cross-organizational mechanism that ensures alignment between functions that contribute to cybersecurity supply chain risk management, such as cybersecurity, IT, operations, legal, human resources, and engineering
Your Recommendation Action Plan for SC-01
Action 1: Develop, Socialize and Communicate a Supply Chain Risk Management Policy:
Create a comprehensive policy that outlines how the organization will identify, assess, manage, monitor, and improve cybersecurity risks within its supply chain.
This policy should define roles, responsibilities, and procedures for conducting risk assessments on suppliers and integrating cybersecurity risk management into the procurement process.
Regularly review and update this policy to reflect changes in the threat landscape and business practices.
Government Example
Commercial Example
Supply Chain Risk Management Policy
Owner: Chief Information Security Officer
Document Status: Approved
Last Updated: [Insert Date]
1. Overview
The goal of the Supply Chain Risk Management Policy is to establish controls to protect [Company Name] from risks related to its external suppliers, vendors, and other third-party entities involved in the supply chain. [Company Name] is committed to managing supply chain risks in a way that protects its operations, reputation, and security, while also fostering a business culture based on trust and integrity.
Effective risk management is a collaborative effort involving all employees, vendors, and affiliates. Each stakeholder must understand and adhere to this policy to reduce cybersecurity, operational, and reputational risks stemming from supply chain activities.
2. Purpose
The purpose of this policy is to support resilience of [Company Name]’s supply chain by outlining requirements for identifying, assessing, and managing risks posed by suppliers, vendors, and third-party service providers. This policy is in alignment with cybersecurity best practices in the NIST Cybersecurity Framework (CSF).
3. Scope
This policy applies to all [Company Name] employees, contractors, and consultants, working with third party service providers that access, store, process or transmit [Company] data.
4. Policy
4.1 General Use and Ownership
[Company Name] proprietary information shared with third-party vendors or suppliers remains the sole property of [Company Name]. This information must be protected in accordance with the company’s Data Protection Standard.
All employees and third-party vendors must report any unauthorized disclosure, theft, or compromise of proprietary or sensitive information immediately to the Information Security team.
Access to [Company Name] proprietary information is granted only to the extent necessary for fulfilling the duties of the assigned role or contract. Any access beyond this scope must be explicitly authorized.
Vendors and suppliers must comply with the security requirements outlined in their contracts.
4.2 Supply Chain Security and Risk Management
All third-party vendors and suppliers that access, store, process or transmit [Company Name] data must undergo risk tiering and assessment prior to engagement. This assessment will evaluate cybersecurity practices, legal and compliance risks, financial stability, and operational resilience.
Legal must ensure that contracts with third parties must include appropriate security and risk management clauses addressing vendor obligations for maintaining data security, breach notification, and compliance with regulatory standards.
Critical (tier 1) suppliers and vendors must provide evidence of their cybersecurity programs, including third-party audits (e.g., SOC 2, ISO 27001)
Vendors are required to notify [Company Name] of any significant changes to their security practices, ownership, or business structure that may introduce new risks.
Cybersecurity will maintain an inventory of all critical vendors and will periodically reassess supply chain risks based on changes in the vendor landscape, emerging threats, or changes in business operations.
4.3 Unacceptable Practices
The following activities are strictly prohibited and may result in termination of contracts or relationships with suppliers:
Failing to disclose security breaches or incidents that affect [Company Name] or its customers.
Providing access to [Company Name] data or systems to unauthorized third parties or subcontractors.
Failing to comply with industry standards or regulatory requirements for data protection, risk management, or cybersecurity.
Introducing malicious software, hardware, or other components that may compromise the integrity of [Company Name]’s systems or data.
Violating intellectual property laws, including improper use of [Company Name]’s proprietary information.
4.4 Incident Response and Recovery
Vendors and suppliers must have incident response procedures in place and must coordinate with [Company Name] in the event of a cybersecurity incident or operational disruption.
Vendors are required to notify [Company Name] of security incidents, breaches, or compromises involving [Company Name] data or systems within 24 hours of discovery.
[Company Name] and vendors will collaborate on incident response actions, including data recovery, forensics, and communication with affected stakeholders.
Recovery procedures must be developed to ensure that supply chain disruptions are minimized and that services and products are restored as quickly as possible.
5. Policy Compliance
5.1 Compliance Measurement
The Cybersecurity team will monitor and verify compliance with this policy through audits, vendor assessments, and feedback from internal teams and vendors.
5.2 Exceptions
Exceptions to this policy must be reviewed and approved by the Information Security team.
5.3 Non-Compliance
An employee found to have violated this policy may be subject to disciplinary action in accordance with HR policies.
6. Related Standards, Policies, and Procedures
Data Protection Standard
Incident Response Policy
Business Continuity and Disaster Recovery Plan
7. Definitions and Terms
The following definitions and terms are provided to assist with understanding:
Vendor: A third-party entity providing goods or services to [Company Name].
Supply Chain Risk: The potential for adverse consequences to [Company Name] due to vulnerabilities or disruptions in third-party suppliers or services.
Incident Response: The process for detecting, responding to, and recovering from cybersecurity incidents or breaches.
For more information or updates to this policy, please contact the Information Security team at [email address].
Other Potential Recommended Actions
Create a RACI: Develop a RACI (Responsible, Accountable, Consulted, Informed) matrix for cybersecurity supply chain activities. This matrix should clarify who is responsible for each aspect of supply chain security and how they should collaborate with others.
Integrate Roles into Job Descriptions: Update job descriptions to include specific cybersecurity supply chain risk management responsibilities. This ensures that new hires and current employees understand their role in managing these risks.
Establish Performance Goals: Set measurable performance goals for employees with cybersecurity responsibilities. Regularly review these goals to ensure continuous improvement in managing supply chain risks.
Develop Supplier and Partner Roles and Access Patterns: Define and communicate the cybersecurity roles and responsibilities of your suppliers and partners. Integrate these roles into contracts and agreements, ensuring clear accountability.
Establish Information Sharing Protocols: Create formal rules for sharing cybersecurity information with suppliers. This could include protocols for reporting vulnerabilities, incidents, and updates related to supply chain security.
Contractual Protections:
Master Services Agreement (MSA) Components:
Clear expectations and responsibilities
Shared responsibility model documentation
Service Level Agreements (SLAs)
Indemnification Provisions:
Include an indemnification provision specifying the financial responsibility in the event of a cybersecurity failure
Define liability limits:
Standard cap (preferred)
Super cap (for critical services)
❌ Never agree to unlimited liability
Your Questionnaire Question from SC-05 (and SC-07)

Subcategory |
|---|
GV.SC-05: Requirements to address cybersecurity risks in supply chains are established, prioritized, and integrated into contracts and other types of agreements with suppliers and other relevant third parties |
GV.SC-07: The risks posed by a supplier, their products and services, and other third parties are understood, recorded, prioritized, assessed, responded to, and monitored over the course of the relationship |
SC-05 NIST Implementation Examples
Ex1: Establish security requirements for suppliers, products, and services commensurate with their criticality level and potential impact if compromised
Ex2: Include all cybersecurity and supply chain requirements that third parties must follow and how compliance with the requirements may be verified in default contractual language
Ex3: Define the rules and protocols for information sharing between the organization and its suppliers and sub-tier suppliers in agreements
Ex4: Manage risk by including security requirements in agreements based on their criticality and potential impact if compromised
Ex5: Define security requirements in service-level agreements (SLAs) for monitoring suppliers for acceptable security performance throughout the supplier relationship lifecycle
Ex6: Contractually require suppliers to disclose cybersecurity features, functions, and vulnerabilities of their products and services for the life of the product or the term of service
Ex7: Contractually require suppliers to provide and maintain a current component inventory (e.g., software or hardware bill of materials) for critical products
Ex8: Contractually require suppliers to vet their employees and guard against insider threats
Ex9: Contractually require suppliers to provide evidence of performing acceptable security practices through, for example, self-attestation, conformance to known standards, certifications, or inspections
Ex10: Specify in contracts and other agreements the rights and responsibilities of the organization, its suppliers, and their supply chains, with respect to potential cybersecurity risks
Your Recommended Action Plan for SCRM Contract Integration (SC-05)
Action 2: Develop an Information Security Addendum to be Included in Vendor Contracts
This should include obligations for suppliers to adhere to specific cybersecurity standards, timely reporting of security incidents, and regular provision of evidence demonstrating compliance with agreed-upon cybersecurity practices.
Example Information Security Addendum
Information Security Addendum
This Information Security Addendum (“Addendum”) is entered into as part of the agreement (“Agreement”) between [Client Name] (“Client”) and [Provider Name] (“Provider”). This Addendum establishes minimum security expectations and obligations for the Provider.
1. Objective
The objective of this Addendum is to define and enforce the implementation of security measures to protect the confidentiality, integrity, and availability of information processed and stored on the Provider’s platform.
2. Scope
This Addendum applies to all systems, data, and services provided by the Provider under the Agreement, including, but not limited to, systems, user data, and related digital assets.
3. Security Controls and Requirements
The Provider agrees to meet minimum security requirements [Company Name] would expect from any supplier with access to store, process or transmit [Company Name] data.
3.1 Govern (GV)
Roles and Responsibilities: Define security roles and responsibilities across the organization, including the designation of a security officer or equivalent responsible for overseeing security governance.
3.2 Identify (ID)
Asset Management: Maintain an inventory of all hardware, software, data, and information resources involved in delivering services to the Client.
Risk Management: Conduct regular risk assessments to identify potential threats and vulnerabilities related to information assets and systems, documenting risks and mitigation measures.
3.3 Protect (PR)
Access Control: Implement strong access control measures, ensuring role or attribute based access and least-privilege principles for all users and administrators.
Multi-factor authentication (MFA) must be required for privileged accounts.
Access to sensitive data must be logged and monitored.
Awareness and Training: Ensure that employees involved in the delivery of services are trained on security best practices, including identifying phishing, social engineering attacks, and handling of sensitive data.
Data Security: Encrypt all sensitive data at rest and in transit using industry-standard encryption protocols (e.g., AES-256 for data at rest and TLS 1.2 or higher for data in transit).
Maintenance and Patching: Regularly update and patch systems, applications, and services to address vulnerabilities. All critical security patches must be applied within [Insert period] of release.
3.4 Detect (DE)
Security Monitoring: Implement continuous monitoring of network traffic, systems, and activities related to the Client’s data to detect and respond to potential security incidents.
Log Management: Maintain logs of security-related activities, including access logs, system events, and security alerts. Logs must be retained for a minimum of [Insert period].
3.5 Respond (RS)
Incident Response Plan: Develop, document, and maintain an incident response plan aligned with the NIST Incident Response Lifecycle (Preparation, Detection, Analysis, Containment, Eradication, and Recovery). The plan should include:
Notification procedures to inform the Client within [Insert period] upon detecting a security incident affecting their data.
Steps for mitigation and recovery.
Breach Notification: Notify the Client within [Insert period] of any confirmed or suspected data breach involving the Client’s data.
3.5 Recover (RC)
Recovery Planning: Implement recovery plans to restore services and data in the event of an incident or data loss, ensuring minimal disruption to the Client.
Backup Procedures: Ensure that data is regularly backed up and stored securely. Backups must be tested periodically to confirm their integrity and functionality.
Compliance and Auditing
The Provider agrees to perform regular internal and external audits to assess compliance with the security controls set forth in this Addendum. The Client reserves the right to review audit results and conduct independent audits of the Provider’s security controls at least annually, or more frequently if necessary.
5. Data Privacy and Confidentiality
The Provider must comply with all applicable data privacy laws and regulations, including [Insert applicable laws, e.g., GDPR, CCPA, etc.]. Confidential data must not be disclosed, accessed, or used for any purpose other than fulfilling the obligations under this Agreement.
6. Third-Party Providers
If the Provider uses third-party services or vendors to support the delivery of services, the Provider shall ensure that those third parties comply with the security controls and requirements of this Addendum. The Provider remains liable for the security of Client data when handled by third parties.
7. Termination
Upon termination of the Agreement, the Provider agrees to securely delete or return all Client data within [Insert period] unless otherwise legally required to retain the data. The method of deletion must be compliant with NIST SP 800-88 (Guidelines for Media Sanitization).
8. Breach of Security Obligations
In the event of a material breach of the security obligations outlined in this Addendum, the Client reserves the right to terminate the Agreement and seek damages, including but not limited to the cost of remediation and recovery from a security incident.
9. Governing Law
This Addendum will be governed by and construed in accordance with the laws governing the Agreement.
10. Amendments
This Addendum may be amended only by mutual written agreement of both parties.
[Client Name]
By: [Client Representative Name]
Title: [Title]
Date: [Date]
[E-learning Platform Provider Name]
By: [Provider Representative Name]
Title: [Title]
Date: [Date]
AI “fabric” prompt: check_agreement
Background context if you’re hearing about Fabric for the first time:
fabric_demo pbpaste | fabric -p check_agreement -s
# DOCUMENT SUMMARY:
This Information Security Addendum establishes minimum security requirements for a provider to protect the confidentiality, integrity, and availability of client data and systems.
# CALLOUTS:
1. The provider must maintain an inventory of all hardware, software, data, and information resources.
2. Regular risk assessments must be conducted to identify potential threats and vulnerabilities.
3. Strong access control measures, including MFA for privileged accounts, must be implemented.
4. All sensitive data must be encrypted at rest (AES-256) and in transit (TLS 1.2+).
5. Systems, applications, and services must be regularly updated and patched to address vulnerabilities.
6. Continuous monitoring of network traffic, systems, and activities related to client data is required.
7. An incident response plan aligned with the NIST Incident Response Lifecycle must be maintained.
8. The client must be notified within a specified period of any security incidents or breaches.
9. Regular internal and external audits must be performed to assess compliance with security controls.
10. Upon termination, the provider must securely delete or return all client data within a specified period.
# CRITICAL:
1. Failure to encrypt sensitive data at rest and in transit using industry-standard protocols.
2. Lack of an incident response plan aligned with the NIST Incident Response Lifecycle.
3. Non-compliance with applicable data privacy laws and regulations, such as GDPR or CCPA.
# IMPORTANT:
1. Absence of regular risk assessments to identify potential threats and vulnerabilities.
2. Insufficient access control measures, including lack of MFA for privileged accounts.
3. Inadequate monitoring of network traffic, systems, and activities related to client data.
4. Failure to perform regular internal and external audits to assess compliance with security controls.
# OTHER:
1. Incomplete inventory of hardware, software, data, and information resources.
2. Lack of regular updates and patches for systems, applications, and services.
3. Insufficient employee training on security best practices and handling sensitive data.
# RESPONSES:
1. CRITICAL: Encryption
- Request: Please confirm that all sensitive data will be encrypted at rest using AES-256 and in transit using TLS 1.2 or higher. If these encryption standards cannot be met, please provide a detailed explanation and propose alternative industry-standard encryption protocols.
2. CRITICAL: Incident Response Plan
- Request: Please provide a copy of your incident response plan aligned with the NIST Incident Response Lifecycle. The plan should include detailed procedures for preparation, detection, analysis, containment, eradication, and recovery, as well as timelines for client notification in the event of a security incident or breach.
3. IMPORTANT: Risk Assessments
- Request: Please confirm that regular risk assessments will be conducted to identify potential threats and vulnerabilities related to information assets and systems. Provide details on the frequency of these assessments and how risks and mitigation measures will be documented and communicated to the client.
4. IMPORTANT: Access Control Measures
- Request: Please confirm that strong access control measures will be implemented, including multi-factor authentication (MFA) for all privileged accounts. Provide details on how access to sensitive data will be logged and monitored, and how the principle of least privilege will be enforced.
➜ fabric_demo Your Questionnaire Question from SC-07 (and SC-05)

Subcategory |
|---|
GV.SC-07: The risks posed by a supplier, their products and services, and other third parties are understood, recorded, prioritized, assessed, responded to, and monitored over the course of the relationship |
SC-07 NIST Implementation Examples
Ex1: Adjust assessment formats and frequencies based on the third party's reputation and the criticality of the products or services they provide
Ex2: Evaluate third parties' evidence of compliance with contractual cybersecurity requirements, such as self-attestations, warranties, certifications, and other artifacts
Ex3: Monitor critical suppliers to ensure that they are fulfilling their security obligations throughout the supplier relationship lifecycle using a variety of methods and techniques, such as inspections, audits, tests, or other forms of evaluation
Ex4: Monitor critical suppliers, services, and products for changes to their risk profiles, and reevaluate supplier criticality and risk impact accordingly
Ex5: Plan for unexpected supplier and supply chain-related interruptions to ensure business continuity
Example Supply Chain Risk Assessment, Integrated with the Procurement Process
Implementation Framework:
Integration Points:
Procurement initiation
Contract renewal
Periodic reviews
Incident triggers
Assessment Tailoring:
Risk tier determination
Criticality evaluation
Data classification consideration
Business impact analysis
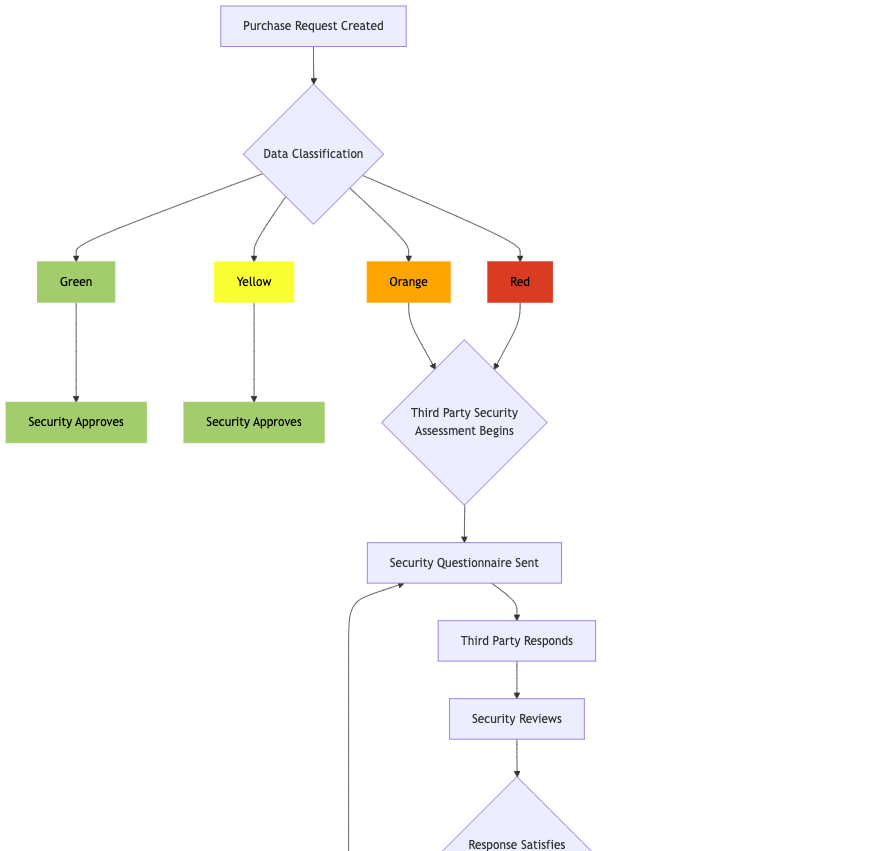
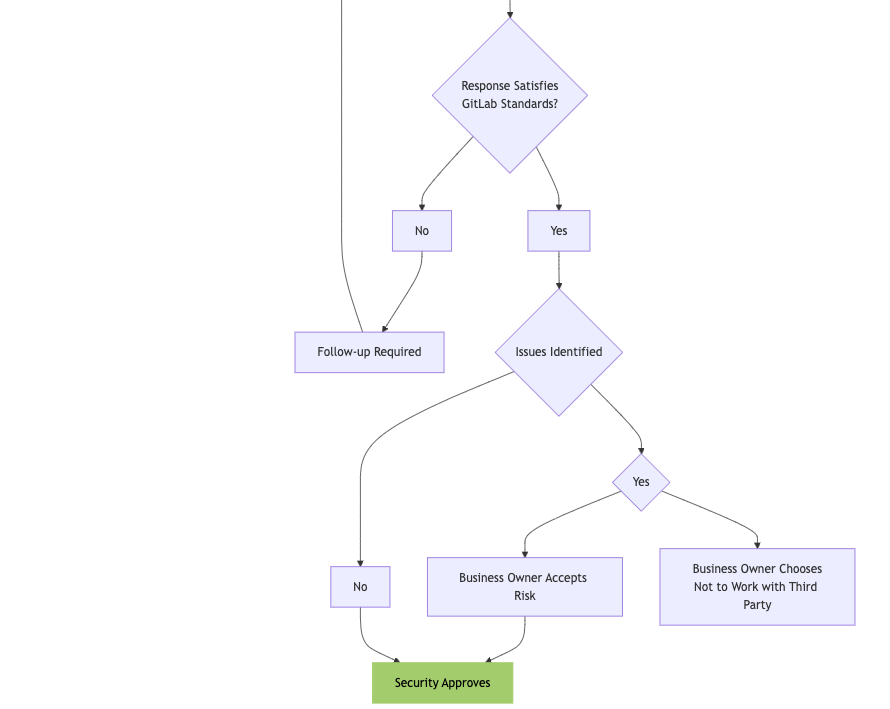
Your Recommended Action Plan for Supply Chain Risk Assessments (SC-07)
Action 3: Regularly Perform Supply Chain Risk Assessments, Integrated with the Procurement Process
Add a checkpoint during the Procurement process for supplier risk assessments, with an emphasis on those critical to operations.
These assessments should be tailored appropriately to different tiers or levels of vendor risk.
Example Supply Chain Risk Management Record
Vendor Name: Salesforce.com
Date of Assessment: [Date]
Assessment ID: [ID Number]
Completed by: [Assessor Name]
Data Classification: Red (Highest)
Vendor Tier: 1 (Highest)
1. Vendor Overview
Vendor Name: Salesforce.com, Inc.
Service Provided: Customer Relationship Management (CRM) Software as a Service (SaaS)
Headquarters: San Francisco, California, USA
Vendor Contact: [Vendor Contact Name & Info]
Business Impact: High – Salesforce serves as a critical platform for managing customer data, workflows, and sales processes.
2. Scope of the Assessment
The assessment focuses on evaluating the risk associated with Salesforce.com’s services to [Your Company], particularly the storage and processing of sensitive customer data, system integrations, and the potential for third-party access to sensitive information.
3. Data Classification: Red
Personal Identifiable Information (PII), financial data, and customer records are processed within the platform, requiring the highest level of cybersecurity controls.
4. Security Certifications & Compliance
Certification/Attestation | Compliant | Date |
|---|---|---|
ISO 27001 | Yes | [Date] |
SOC 2 Type II | Yes Unqualified opinion and only minor exceptions noted by EY (see attached) [Your Company] CUECs reviewed and operating effectively | [Date] |
5. Data Handling & Privacy
Data Location: Salesforce stores data across global data centers, with options for regional hosting depending on compliance requirements (e.g., EU-based customers may use EU data centers).
Data Encryption: Salesforce encrypts data both at rest and in transit using AES-256 encryption.
Retention Policy: Customizable data retention policies allow clients to configure how long data is retained before being purged.
6. Sub-Processor Risk
List of Sub-Processors: Salesforce utilizes third-party sub-processors (e.g., AWS) for specific functions such as hosting and cloud storage.
Sub-Processor Review: Salesforce provides transparency into the sub-processors used and ensures they are compliant with relevant security and privacy regulations.
Contractual Obligations: All sub-processors are contractually bound by the same security and data protection requirements Salesforce adheres to.
7. Incident Response
Incident Reporting Process: Salesforce has a formal incident response plan. They offer 24/7 monitoring and have an established protocol for reporting security incidents to clients within 72 hours (per GDPR requirements).
Breach History: No major breaches reported in the last [number] years.
8. Compliance with Legal & Regulatory Requirements
GDPR: Yes
CCPA: Yes
PCI-DSS: Not applicable to the core CRM product, but payment integrations are compliant.
9. Risk Ratings
Risk Category | Residual Risk Level | Details |
|---|---|---|
Data Privacy | Moderate | Salesforce processes personal data, including customer PII. Risk related to data breaches or non-compliance with GDPR, CCPA, etc. |
Cybersecurity | Low | Salesforce has strong track record of transparency and security investments across the cybrsecurity framework functions - as seen in their Trust Center |
Business Continuity | Low | Business continuity plans are in place, and Salesforce provides high service availability (99.9% uptime SLA). |
Third-Party Dependencies | Moderate | Salesforce may rely on sub-processors, potentially introducing indirect risk. |
Compliance | Low | Salesforce complies with GDPR, HIPAA, and other regional laws and industry standards. |
Financial Stability | Low | Salesforce is a financially stable, publicly traded company with a strong market presence. |
10. Final Risk Rating & Recommendation
Final Risk Rating: Moderate
Recommendation: Salesforce.com, Inc. is a mature, well-established vendor with robust security controls and compliance to relevant legal standards.
However, attention should be given to ensuring that strong contractual agreements are in place to mitigate risks related to data privacy and operational disruptions, and that [Company Name] configures this SaaS securely, implementing and testing controls for it’s role in the shared responsibility model.
Example Supply Chain Risk assessment Tools
Financial Health and Legal History Services: Evaluating a vendor’s financial stability and legal track record is also important for assessing reputation and risk.
Examples: Dun & Bradstreet, LexisNexis, Experian Business Credit
Vendor Risk Management Platforms: These platforms allow organizations to conduct assessments and continuously monitor the cybersecurity practices of their third-party vendors. These services can also help determine whether a third party complies with industry standards (e.g., ISO 27001, SOC 2).
Examples: OneTrust, RiskLens
Security Rating Platforms: These platforms continuously assess third-party vendors and provide security ratings based on their digital footprint. They monitor factors like open vulnerabilities, historical breaches, and external threats.
Examples: BitSight, SecurityScorecard, UpGuard, RiskRecon
Key Takeaways
Core Principles:
Shared Responsibility: Clear delineation of security obligations
Risk Tiering: Appropriate controls based on vendor criticality
Continuous Monitoring: Ongoing assessment throughout vendor lifecycle
Integration: Embed SCRM into procurement and business processes
Implementation Priorities:
Establish Policy Framework (SC-01)
Develop Contract Requirements (SC-05)
Implement Assessment Process (SC-07)
Deploy Monitoring Tools
Maintain Continuous Improvement
Success Factors:
Executive sponsorship and support
Cross-functional collaboration
Clear communication channels
Regular training and awareness
Metrics and reporting
Continuous improvement mindset






