🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
12.7-12.9 📋 Step 4: Generate the Questionnaire
Align with NIST Cybersecurity Framework
Purpose: Create questions tailored to NIST CSF to evaluate organizational capabilities
Framework Coverage: Must assess all six functions:
Govern
Identify
Protect
Detect
Respond
Recover
Federal Trade Commission (FTC) Safeguards Rule of 2023
“Requires non-banking financial institutions to develop, deploy, and maintain a comprehensive security program to keep customer financial data safe.”
Compliance Method: Implementing NIST CSF + Cyber Risk Management Action Plan (CR-MAP)
Start With Six Questions for a Comprehensive Plan
How well does the organization govern its risk management strategy, expectations, and policy?
How well does the organization identify digital assets and cyber risks?
How well does the organization protect your assets against those risks?
How well does the organization detect cybersecurity breaches?
How well does the organization respond to those breaches?
How well does the organization recover from those breaches?
Tune and Tailor for the Organization

Very different threats and vulnerabilities for:
Company | Industry | Key Cyber Risk Considerations |
|---|---|---|
Equifax | Credit Reporting and Information Services | Data breaches, personal information exposure, regulatory compliance |
Home Depot | Big Box Retail | Large physical infrastructure, supply chain for physical goods |
Time Warner | Entertainment | IP theft, media piracy |
Visa | Financial | Payment card fraud, transaction security, PCI-DSS compliance |
Los Alamos National Labratory | Nuclear | National security, protecting sensitive nuclear weapons data, insider threats, espionage risks |
Example of More In-Depth Questions

Mastering Cyber Resilience p.187, AKYLADE

NIST SP800-30 Risk Matrix Heat Map
Risk Appetite Statement
At [Organization Name], we are committed to achieving our strategic objectives while maintaining a balanced approach to risk management. Our risk appetite reflects our willingness to accept, manage, and mitigate risks to ensure the long-term success and sustainability of our organization.
Key Principles:
Strategic Alignment: We align our risk-taking with our strategic goals and objectives, ensuring that all risks are assessed in terms of their potential impact on our long-term vision.
Operational Risk: We have a low tolerance for risks that could compromise the safety, security, and well-being of our employees, customers, and assets. We strive for operational excellence and compliance with all relevant regulations and standards.
Financial Risk: We maintain a moderate risk appetite concerning financial exposures. We are willing to accept risks that offer a reasonable expectation of return, provided they do not threaten our financial stability or liquidity.
Reputational Risk: We have a low tolerance for risks that could damage our brand, reputation, or relationships with stakeholders. We prioritize ethical behavior and transparency in all our operations.
Innovation and Growth: We support innovation and growth initiatives, recognizing that they may involve higher levels of risk. We are open to taking calculated risks in pursuit of new opportunities, provided they are well-researched and managed.
Compliance and Legal Risk: We have zero tolerance for risks that would result in non-compliance with legal, regulatory, or ethical standards. We are committed to upholding the highest standards of governance and accountability.
Our risk appetite is designed to empower our leaders and employees to make informed decisions that balance opportunity and risk. We continually review and adjust our risk appetite to reflect changes in our external environment, strategic priorities, and risk landscape. This approach ensures that we remain resilient, adaptable, and focused on creating value for our stakeholders.
Risk-to-Cost-of-Controls Curve
Key Concept: Balance is Critical
It is possible to have too much (or too little) security
Too Little Security:
Vulnerability to threats
Potential for major incidents
Compliance failures
Too Much Security:
Wasted resources (time & money)
User friction
Damaged security culture
Employees become insider threats by bypassing controls


Reference: The Phoenix Project
Key Lesson: Avoid becoming "the office of the CIS-NO"
Better Approach:
"Be brief, be brilliant, be gone"
Support organizational objectives
Create safe space to discuss risk
Balance protection with enablement
⚖ Protect and Enable for Reasonable Cybersecurity


Example 10 Score (Over-Engineering): $100k garage for a $5k car
Resources could be better allocated elsewhere
Creates unnecessary complexity
Avoid being the problem

Typical Number of Questions
Typical number: 31 questions (from 22 CSF categories)
Minimum: 6 questions
Maximum: 106 questions
Best Practice: Include function/category/subcategory IDs as question numbers


Numbering Questions

🎯 Step 5: Determine Your Target Scores
Five Approaches to Target Score Setting
1. Minimum Score Approach
Target: All functions = 5.0
Philosophy: Meet baseline acceptable security across the board
Pros:
Simple to understand
Clear baseline for all areas
Cons:
No prioritization
May not address specific risks



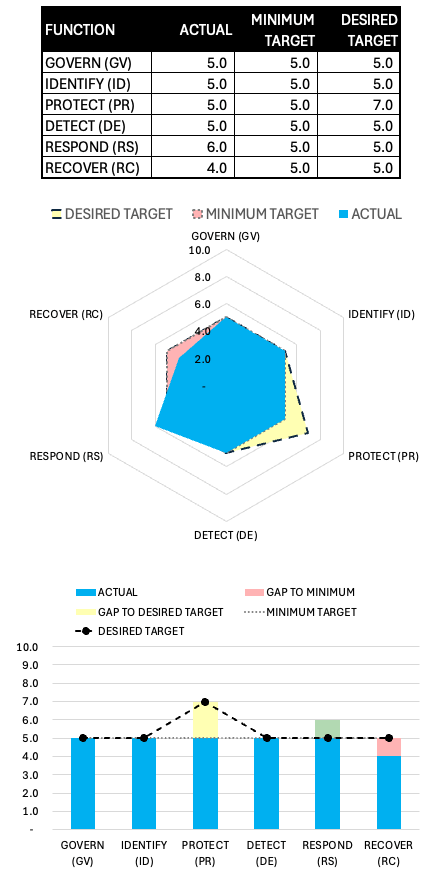
2. Strong Castle Approach
Target: Protect = 7.0, all others = 5.0
Philosophy: Build strong perimeter defense ("hard shell, soft center")
Characteristics:
Focus on preventive controls
Common in on-premise environments
Like medieval fortress design
Weaknesses:
Vulnerable to modern threats (social engineering)
Less effective as attacks evolve
Declining in popularity


3. First Responder Approach
Target: Respond = 7.0, all others = 5.0
Philosophy: Excel at incident response to compensate for other areas
Use Cases:
Online services prioritizing availability
Organizations without critical IP
Fast-paced environments


4. Big City Approach
Target: Respond = 7.0, Recover = 7.0, all others = 5.0
Philosophy: Zero-trust mentality; assume breach will occur
Characteristics:
Modern, mature perspective
Treats network like a city, not a fortress
All users treated as untrusted
Ready to respond and recover quickly


5. World Class Approach
Target: All functions = 8.0
Philosophy: Excellence in all areas
Reality Check:
Very expensive and difficult
Only practical for:
Very small organizations
Government agencies (NSA, CIA)
Organizations with unlimited budgets


Case Study Examples
SaaS Company ($10M Annual Revenue)
Sensitive Assets:
Customer names, addresses, credit card info
Source code
Trade secrets
Recommended Approach: Modified Strong Castle
Protect = 6-7
Others = 5
Rationale: High value digital assets need strong protection

Multinational Corporation ($1B Annual Revenue)
Characteristics:
Geographically dispersed
Large security budget
Complex threat landscape
Recommended Approach: Big City
Respond = 7
Recover = 7
Others = 5-6
Rationale: Incidents inevitable; focus on resilience

Real-World Insights
Why Radar Diagrams Are "Spiky" in Practice
Left of Boom vs Right of Boom Functions
Left of Boom (Prevention): Identify & Protect
Easier for GRC professionals to understand
More comfortable for less technical backgrounds
Tangible progress (data inventories, firewall implementations)
Well-known controls (MFA, EDR, network segmentation)
Right of Boom (Resilience): Detect, Respond, Recover
More technical and complex
Harder to implement and refine
Less frequently exercised (quarterly tabletops vs daily operations)
Mature slower in most organizations
Cyber Resiliency vs Cybersecurity
Security: Implies complete protection (unrealistic)
Resiliency:
Reduces impact when incidents occur
Minimizes likelihood of occurrence
True essence of GRC
Common Misconceptions
"EDR = Detection": Detection is more complex than just having tools
"Backups = Recovery": Recovery involves much more than just backups
Protection feels more productive: Easier to see and measure results
Industry Maturity Pattern
Organizations start with Identify & Protect
Once locked down, shift to Detect, Respond, Recover
Different businesses have different objectives → different spiky patterns
Industry moving from protection focus to resilience focus
Key Takeaways for Exam
What to Expect
Visual Elements:
Radar diagrams (most common)
Tables with scores
Possibly bar charts (though less common)
Scenarios: Case studies requiring target score recommendations
Critical Concepts to Remember
Balance is key: Too much security can be as problematic as too little
Tailoring is essential: One size does NOT fit all
Framework is voluntary: Adapt to organizational needs
Maturity varies: Organizations develop different functions at different rates
Business objectives drive strategy: Not technology
Scoring Reminders
5 = Minimum acceptable (not 0 or 1)
8 = Fully optimized (not 10)
9-10 = Excessive/wasteful
Unknown and N/A are valid responses