So you want to become a GRC Analyst?
Awesome! Here’s a free Career Development Plan template full of resources that I think you’ll find helpful.
It’s the best-of-the-best I’ve discovered in my mid-career transition to GRC, broken into Harvard’s recommended ratio to grow yourself faster of:
10% Education
20% Relationships
70% Experiences
This template format and the menu of resources inside it would also be helpful to a broad range of other target job areas and career stages.
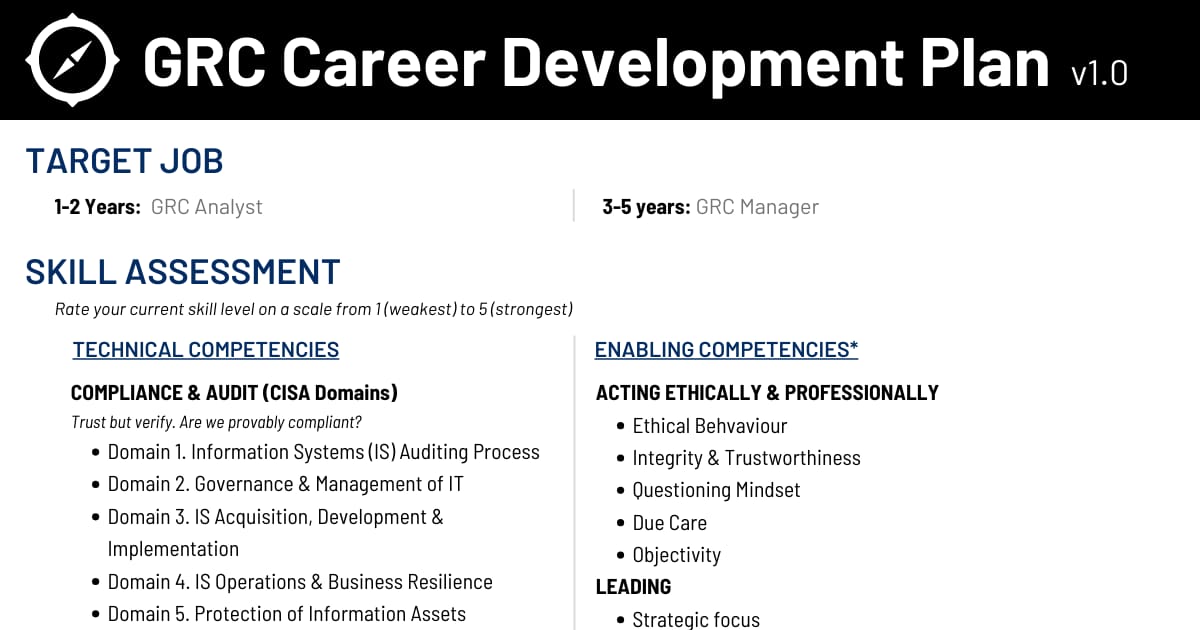
GRC Career Development Plan
Your Name: | |
Target Role: | |
Target Timeline (months) | |
Date Created: |
SKILL SELF-ASSESSMENT
Rate your current skill level: 1 (Learning) to 3 (Competent) to 5 (Expert)
Technical Competencies
Competency | Rating (1-5) | Priority Focus? |
|---|---|---|
COMPLIANCE & AUDIT | ||
Audit Planning & Execution | 1 2 3 4 5 | Yes/No |
Evidence Collection & Testing | 1 2 3 4 5 | Yes/No |
Control Documentation | 1 2 3 4 5 | Yes/No |
Regulatory Requirements (SOC 2, ISO, HIPAA, etc.) | 1 2 3 4 5 | Yes/No |
RISK MANAGEMENT | ||
Risk Assessment Methodology | 1 2 3 4 5 | Yes/No |
Third-Party/Vendor Risk | 1 2 3 4 5 | Yes/No |
Risk Quantification & Reporting | 1 2 3 4 5 | Yes/No |
Risk Treatment & Remediation Tracking | 1 2 3 4 5 | Yes/No |
GOVERNANCE | ||
Policy & Procedure Development | 1 2 3 4 5 | Yes/No |
Security Awareness Program | 1 2 3 4 5 | Yes/No |
Framework Alignment (NIST CSF, CIS, ISO) | 1 2 3 4 5 | Yes/No |
Metrics & Executive Reporting | 1 2 3 4 5 | Yes/No |
TECHNICAL FOUNDATIONS | ||
Networking Basics (TCP/IP, DNS, Firewalls) | 1 2 3 4 5 | Yes/No |
Cloud Security Concepts (AWS/Azure/GCP) | 1 2 3 4 5 | Yes/No |
Identity & Access Management | 1 2 3 4 5 | Yes/No |
Security Operations Basics | 1 2 3 4 5 | Yes/No |
Technical Score: ______ / 80