Table of Contents
Exam Objectives 📚
Candidates must be able to understand the Implementation Tiers as they relate to the NIST Cybersecurity Framework. Students will be able to:
3.1 Explain how Implementation Tiers are utilized in the NIST Cybersecurity Framework, including how they differ from a maturity model:
NIST Cybersecurity Implementation Tiers
ISO/IEC 27001
Capability Maturity Model Integration (CMMI)
Cybersecurity Capability Maturity Model (C2M2)
Cybersecurity Maturity Model Certification (CMMC)
3.2 Given a scenario, analyze an organization’s Implementation Tier based on its current cybersecurity posture:
Tier 1 (Partial)
Tier 2 (Risk Informed)
Tier 3 (Repeatable)
Tier 4 (Adaptive)
3.3 Given a scenario, recommend strategies for moving an organization between Implementation Tiers:
Assess the current state
Define the target state
Develop a plan of action
Implement the plan of action
Monitor and adjust
Implementation Tiers 🪜
There’s no strict order in which the core, tiers, and profiles must be implemented and utilized.
Typically :
First, Choose an implementation tier
Implementation Tiers
Then, create a profile based on the selected tier
Creating a Profile
Then, use the core to determine which categories and activities should become part of your organization’s planned implementation, monitoring and maintenance requirements

Framework Core
Back to Basics: Six Functions
Reminder 🧠
Before you begin to implement the framework using this sequence, it’s vital that you have a good understanding of the basics of the framework core

It’s an iterative process to revisit and refine over time
Adapt to evolving threats and changing business requirements
Choosing an Implementation Tier 🤔

Begins with an assessment

CSF Subcategory | Description |
|---|---|
GV.OC-01 | The organizational mission is understood and informs cybersecurity risk management |
Current State Attribute | Description |
|---|---|
Current Priority | |
Current Status | |
Current Policies, Processes, and Procedures | |
Current Internal Practices | |
Current Roles and Responsibilities | |
Current Selected Informative References | |
Current Artifacts and Evidence |
Identify strengths and weaknesses in the cybersecurity domains, e.g.
Risk management
Threat intelligence
Incident response
Security controls
Understanding current tier level ➡ gain insight into cybersecurity posture ➡ prioritize efforts
Considerations for choosing an implementation tier
Risk tolderance
Available resources
Business objectives
Cybersecurity maturity level they aspire to attain
Key success factors:
Align to the organization’s risk appeitite
Align to the organization’s long-term cybersecurity goals
Ensures realistic and achievable targets for the organization
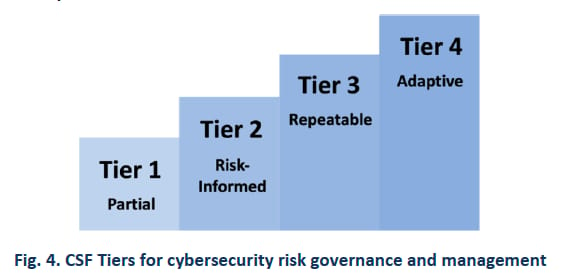
4 Tiers: Least to Most Mature

Tier 1 - Partial

Tier 2 - Risk Informed

Tier 3 - Repeatable

Tier 4 - Adaptive
Tier | Description | So What? |
|---|---|---|
Tier 1 - Partial | Ineffective and inconsistant methods Lack processes Fragmented practices | Limited awareness of cybersecurity risks Ad hoc and reactive |
Time & Energy Management Priority Matrix
URGENT | NOT URGENT | |
|---|---|---|
IMPORTANT | Crisis Tier 1 - Partial DETECT RESPOND RECOVER | GOVERN IDENTIFY —> BIAs PROTECT Planning, preparation Prevention Relationship building Personal growth |
NOT IMPORTANT | DMs (unless boss, etc 👩💼) | Binge watching (unless GoT, etc ⚔ ) |
Tier | Description | So What? |
|---|---|---|
Tier 2 - Risk Informed | Developed formalized processes and risk management methods Still evolving and room for improvement | Risk management methods are informal and underdeveloped. Have an awareness of cybersecurity risks at an organization level, but they lack an organization-wide approach to managing those risks |
Tier 3 - Repeatable | Robust risk management programs Proactive approach to cybersecurity Consistent results | Proactive: Structured methods, well defined processes, routinely review risk management participation Now we can continuously improve! |
Tier | Description | So What? |
|---|---|---|
Tier 4 - Adaptive | Advanced capability to adapt Seek out emerging technologies Continuously strive for excellence | Keep pace with evolving cybersecurity risk Risk management methods with feedback loops that aid the organization in learning from experience to continually get better over time |
Choosing an implementation tier
1⃣ Assess current level
2⃣ Set goals to advance tiers
3⃣ Improve resilience
Implementation Tier Progression 🏋
Choosing the Right Goal

Tier 1 - Partial

Tier 2 - Risk Informed

Tier 3 - Repeatable

Tier 4 - Adaptive
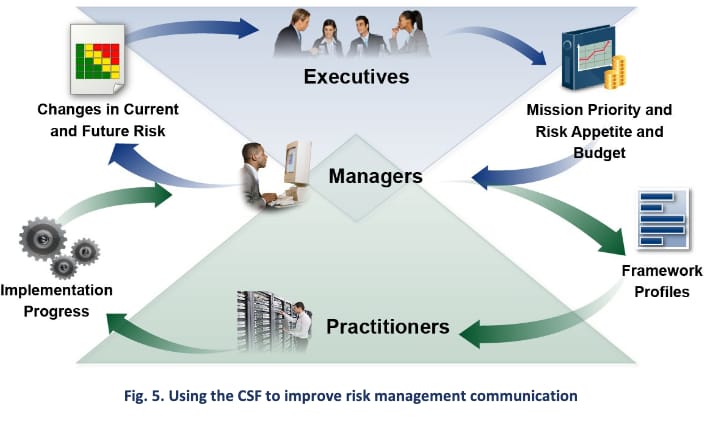
Three dimensions of cyber risk management
Risk management process
Integrated Risk Management program
External participation
Risk Management Process
How well does the organization establish and execute a risk management process that aligns with its risk tolerance, objectives, and the overall business strategy?
Integrated Risk Management Program
To what extent is cyber risk management integrated into organizational governance?
How repeatable are the outcomes that the cybersecurity program produces?
External Participation
Maturity Models 🏃 🚶
Term | Definition | So What? |
|---|---|---|
Maturity Models | A structured framework that assesses and guides the progression of an organization’s capabilities and maturity levels in a specific domain, providing a roadmap for improvement and growth | Maturity models typically provide a structured progression of maturity levels CSF implementation tiers focus on evaluating the effectiveness of cybersecurity practices, rather than the organization’s maturity level |
Commonly Used Maturity Models
Capability Maturity Model Integration (CMMI)
ISO/IEC 27001 maturity model
Cybersecurity Maturity Model Certification (CMMC)
Cybersecurity Capability Maturity Model (C2M2)
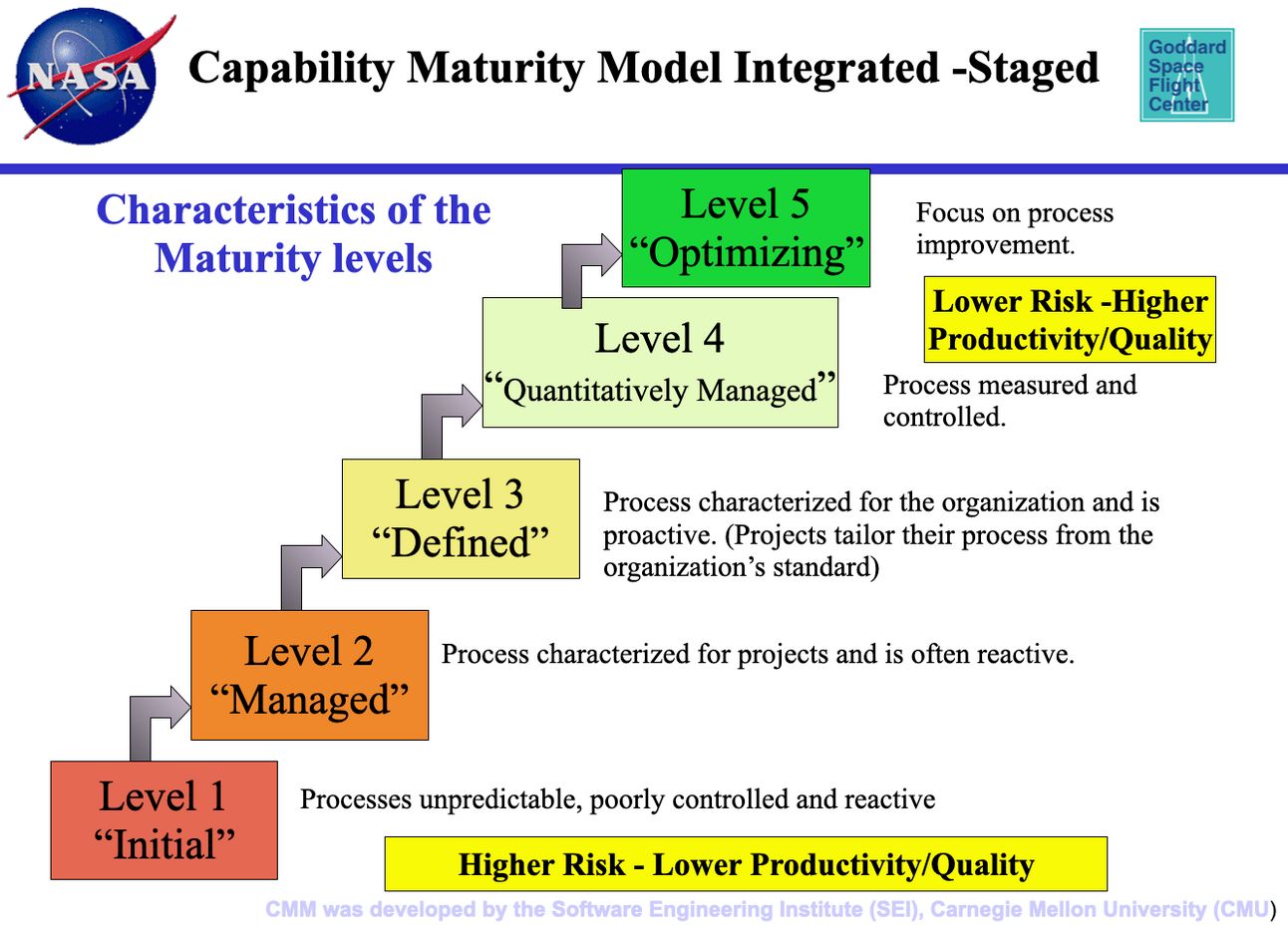
Capability Maturity Model Integration (CMMI)
5 Maturity Levels
ISO/IEC 27001 Maturity Model
Defines a set of criteria and indicators to assess the effectiveness, efficiency, and sustainability of the organization’s Information Security Management System (ISMS)
ISMS
Includes people, process and IT systems
Plan-Do-Check-Act continuous improvement (Deming) cycle
Typical Components:
Clause | Description |
|---|---|
4. Context of the Organization | This clause requires the organization to determine external and internal issues relevant to its purpose and strategic direction, and that affect its ability to achieve the intended outcomes of its ISMS. Includes understanding the needs and expectations of interested parties. |
5. Leadership | Leadership and top management must demonstrate leadership and commitment to the ISMS, establish policies, and ensure that responsibilities and authorities are assigned and communicated within the organization. |
6. Planning | Involves the assessment of information security risks (risk assessment) and the decision on necessary security controls (risk treatment), as well as the establishment of information security objectives. |
7. Support | Covers all aspects of resourcing the ISMS, including human resources, organizational knowledge, and the management of documented information. |
8. Operation | Detailed execution and management of the ISMS processes, including the assessment and treatment of information security risks. |
9. Performance Evaluation | Monitoring, measurement, analysis, and evaluation of the ISMS to ensure that it meets the organization's expectations. It also includes an internal audit program and a management review. |
10. Improvement | Focuses on continual improvement of the ISMS, aiming to enhance its suitability, adequacy, and effectiveness over time. This includes addressing nonconformities and taking corrective actions. |
The ISO/IEC 27001 maturity model identifies areas for improvement, prioritizes efforts, and establishes a roadmap for advancing information security capabilities
Cybersecurity Maturity Model Certification (CMMC)
US DoD
Developed by the U.S. Department of Defense (DoD) to assess and certify the cybersecurity maturity of organizations participating in DoD contracts: the Defense Industrial Base (DIB)
NIST SP800-171 Protecting Controlled Unclassified Information (CUI) in Non-Federal Systems
3 levels
Cybersecurity Capability Maturity Model (C2M2)
US DoD
Initially focused on the energy sector
Expanded more broadly into infrastructure
Comprehensive framework with various cybersecurity domains, such as risk management, incident response, secure configuration management, and security awareness
3 levels
Initiated
Performed
Managed
CSF Implementation Tiers are Not Maturity Levels
While organizations identified as Tier 1 (Partial) are encouraged to consider moving to Tier 2 or greater, Tiers do not represent maturity levels.
CSF implementation tiers focus on evaluating the effectiveness of cybersecurity practices
Maturity models offer a broader perspective on the overall maturity and capability of an organization’s cybersecurity program
By leveraging both the NIST CSF implementation tiers and relevant maturity models, organizations can develop a comprehensive approach to enhance their cybersecurity practices and maturity, aligning with their specific goals and industry requirements
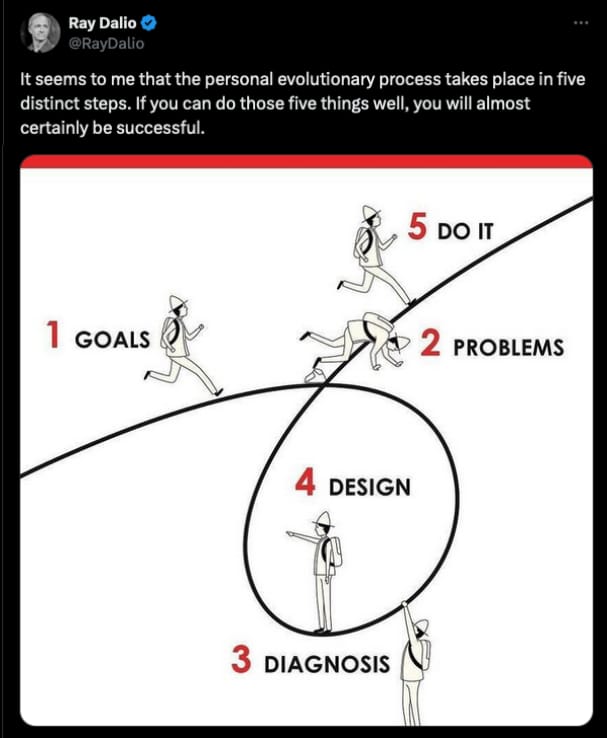
Strategies for Moving Between Implementation Tiers ♟️
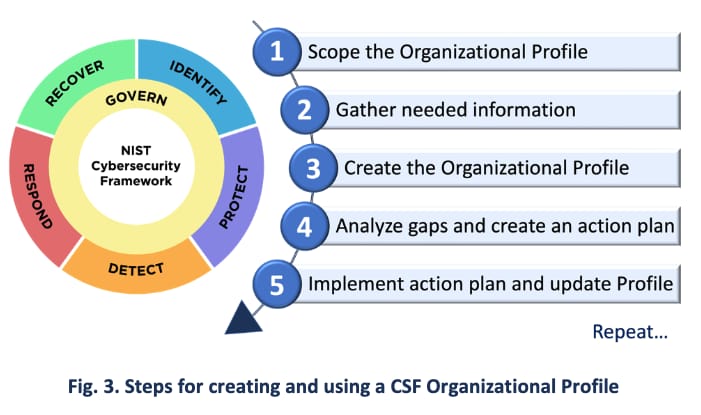
5 Step Process
Step | Description |
|---|---|
1. Assess | Current state implementation tier Starting point |
2. Define target | Desired state implementation tier What will be different when we get there? |
3. Develop a plan of action | Who, what, when? May include purchasing and installing new technologies, writing new policies or training employees |
4. Implement the plan | Example: Develop formalized policies and create a basic risk management program |
5. Monitor and adjust | Improving cyber risk management does not happen overnight! Are desired results being achieved? If not, return to step 3. |
Need Profiles
Conclusion and Touchpoints ✅
CSF implementation tiers have a role in evaluating an organization’s cybersecurity practices.
There is no strict order in which the core, tiers, and profiles must be implemented, but following a logical sequence can lead to a comprehensive and effective implementation.
Four implementation tiers:
Tier 1 (Partial)
Tier 2 (Risk Informed)
Tier 3 (Repeatable)
Tier 4 (Adaptive)
Each tier represents a level of maturity in an organization’s cybersecurity practices, with Tier 4 being the highest level of maturity
Even though the term maturity is used heavily when describing the implementation tiers, it is important to note that the implementation tiers are not a maturity model
Instead, organizations can select a compatible maturity model if they wish to certify their maturity
Capability Maturity Model Integration (CMMI)
ISOIEC 27001 maturity model
Cybersecurity Maturity Model Certification (CMMC)
Cybersecurity Capability Maturity Model (C2M2)
With implementation tier progression, organizations can strategically advance their cybersecurity capabilities
Progression from one tier to the next involves setting clear objectives, allocating resources effectively, and developing targeted action plans
By understanding the dimensions of the risk management process, integrated risk management program, and external participation, organizations can evaluate their current tier level and chart a path toward higher maturity
Moving between different implementation tiers is not meant to be seen as a linear progression, it’s more agile and spiral in nature as we identify current practices, attempts to improve them, monitors the results and then adapts a new plan
The CSF implementation tiers are framework to assess and enhance cybersecurity practices
Guideposts: to identify their current capabilities, set targets for improvement, and allocate resources effectively
Implementing CSF in a systematic and progressive manner is very powerful, to build a strong foundation that improves cybersecurity posture and resilience