🔐 Simply Cyber Course Materials - Community Access Welcome! This content is shared with enrolled students as part of our commitment to inclusion and value delivery in cybersecurity education. We believe in supporting each other's learning journey through ethical collaboration. Please help us maintain this open educational environment by keeping this URL within our course community. Sharing this link publicly undermines our ability to freely provide these materials. Questions? Reach out to your instructor—we're here to support your success!
Table of Contents
Exam Objectives 📚
Candidates must be able to understand the Framework Profiles as they relate to the NIST Cybersecurity Framework. Students will be able to:
4.1 Summarize how profiles are used to tailor the Framework for varying risk management strategies
Key components of a profile
Core functions
Categories
Subcategories
Utilizing profiles
Current profile versus target profile
Map profiles to an organization’s cybersecurity posture
4.2 Given a scenario, utilize a profile to tailor the NIST Cybersecurity Framework to specific organizational needs
Tailor profiles to support risk management strategies
Tailor profiles to support regulatory compliance requirements
Utilize profiles to measure an organization’s cybersecurity posture over time
Identify relevant core functions, categories, and subcategories
4.3 Explain the use of profiles in the Framework
Profile templates
Sector-specific profiles
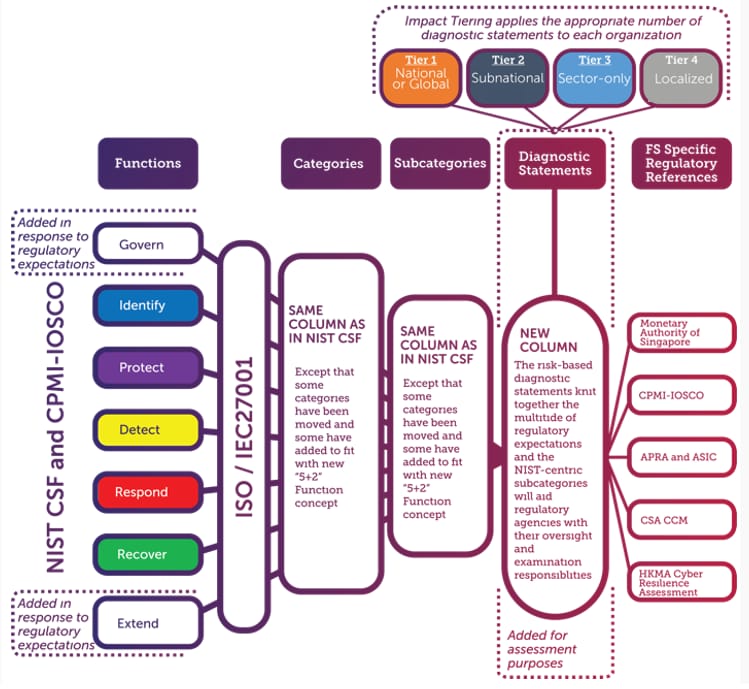
Cyber Risk Institute (CRI) Profile
Manufacturing profile
Election infrastructure profile
Hybrid Satellite Network profile
Smart grid profile
Connected vehicle profile
Payroll profile
Maritime profile
Communications profile
Profiles 🛤️
Term | Definition | So What? |
|---|---|---|
Profiles | An organization’s cybersecurity objectives, current state, and target state, providing a roadmap for aligning cybersecurity activities and priorities with the organization’s business requirements | 🫵 Your customization and alignment of the framework to an organization’s unique needs, goals and risk management strategies is the key to how much value you can add |
Framework Core
Building blocks for managing cybersecurity risks

What is the Framework Core and how is it used?
The Framework Core is a set of cybersecurity activities, desired outcomes, and applicable references that are common across critical infrastructure sectors. An example of Framework outcome language is, "physical devices and systems within the organization are inventoried."
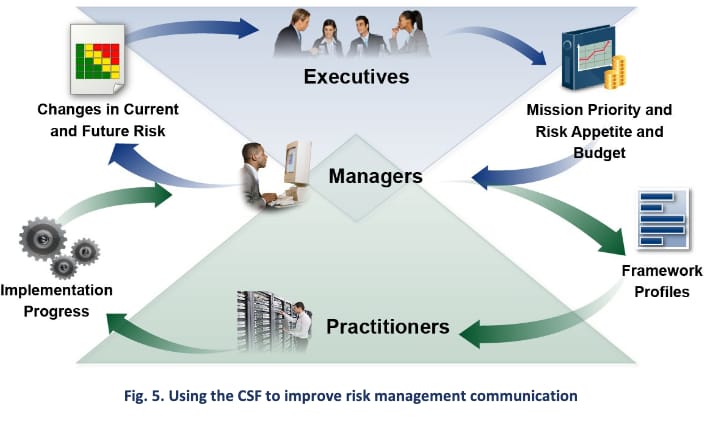
The Core presents industry standards, guidelines, and practices in a manner that allows for communication of cybersecurity activities and outcomes across the organization from the executive level to the implementation/operations level. The Framework Core consists of five concurrent and continuous Functions—Identify, Protect, Detect, Respond, Recover. When considered together, these Functions provide a high-level, strategic view of the lifecycle of an organization's management of cybersecurity risk. The Framework Core then identifies underlying key Categories and Subcategories for each Function, and matches them with example Informative References, such as existing standards, guidelines, and practices for each Subcategory.
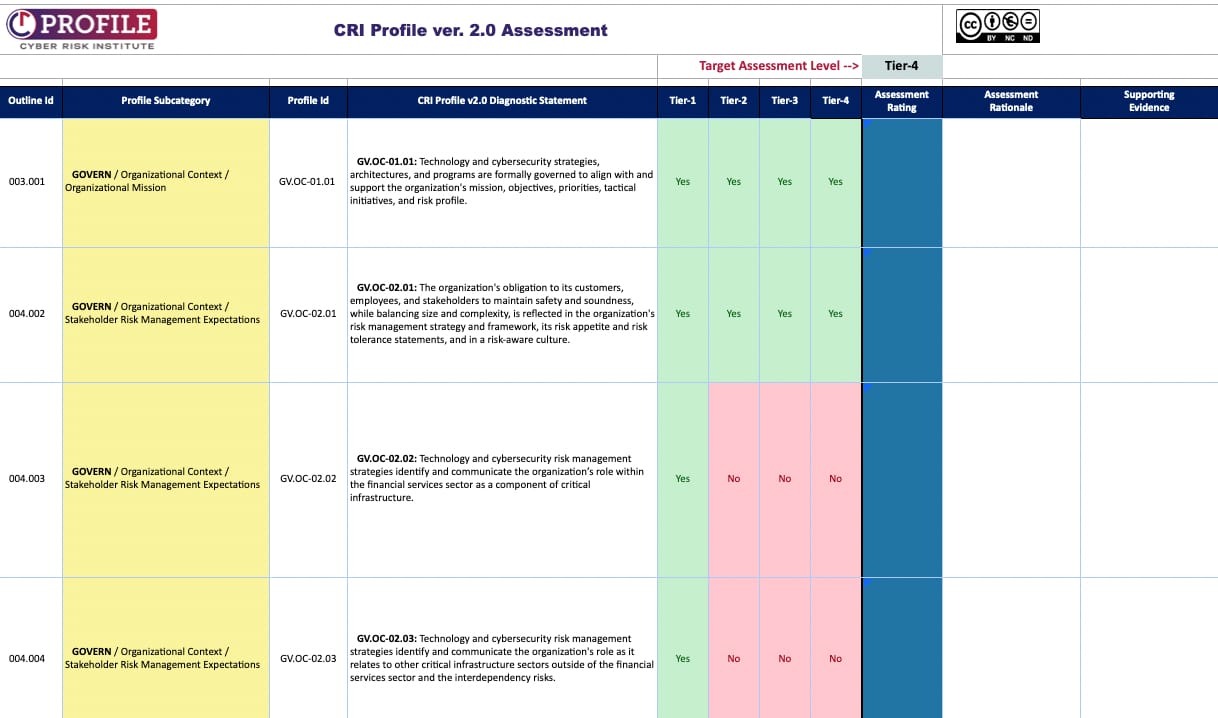
Selected Target Implementation Tier
What are Framework Implementation Tiers and how are they used?
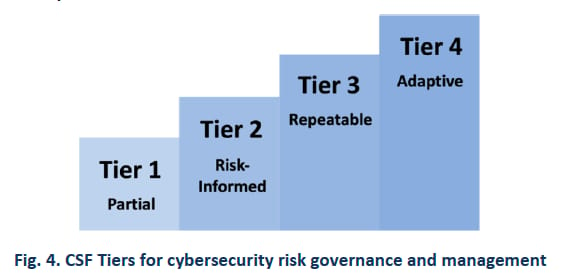
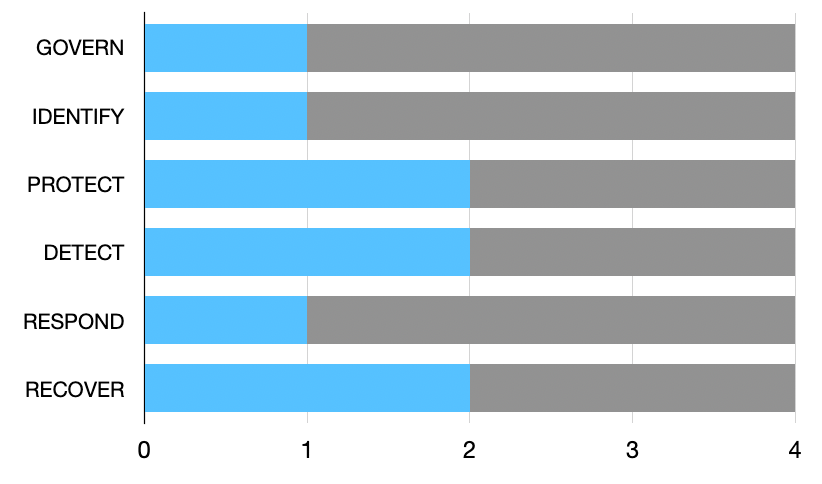
Framework Implementation Tiers ("Tiers") provide context on how an organization views cybersecurity risk and the processes in place to manage that risk. Tiers describe the degree to which an organization's cybersecurity risk management practices exhibit the characteristics defined in the Framework (e.g., risk and threat aware, repeatable, and adaptive). The Tiers characterize an organization's practices over a range, from Partial (Tier 1) to Adaptive (Tier 4). These Tiers reflect a progression from informal, reactive responses to approaches that are agile and risk-informed. During the Tier selection process, an organization should consider its current risk management practices, threat environment, legal and regulatory requirements, business/mission objectives, and organizational constraints.
Are the Tiers equivalent to maturity levels?
The Framework Implementation Tiers are not intended to be maturity levels. The Tiers are intended to provide guidance to organizations on the interactions and coordination between cybersecurity risk management and operational risk management. The key tenet of the Tiers is to allow organizations to take stock of their current activities from an organization wide point of view and determine if the current integration of cybersecurity risk management practices is sufficient given their mission, regulatory requirements, and risk appetite. Progression to higher Tiers is encouraged when such a change would reduce cybersecurity risk and would be cost-effective.
Key Components of a Profile
The same as the CSF Core: Functions ➡ Categories ➡ Subcategories and activities
For each:
Determine relevance and priority that align to the the organization’s risk management objectives
Customize
Creating a Profile 🎨
Step 1: Identify Organizational Requirements and Objectives

Foundational step
Thoroughly assess the organization’s risk management objectives, industry-specific regulations, business priorities, and cybersecurity needs.
Identify the key drivers that shape the organization’s cybersecurity strategy, e.g.
Protecting sensitive data
Complying with regulatory requirements
Safeguarding critical infrastructure
Step 2: Evaluate the Framework Core
Stakeholder engagement is key
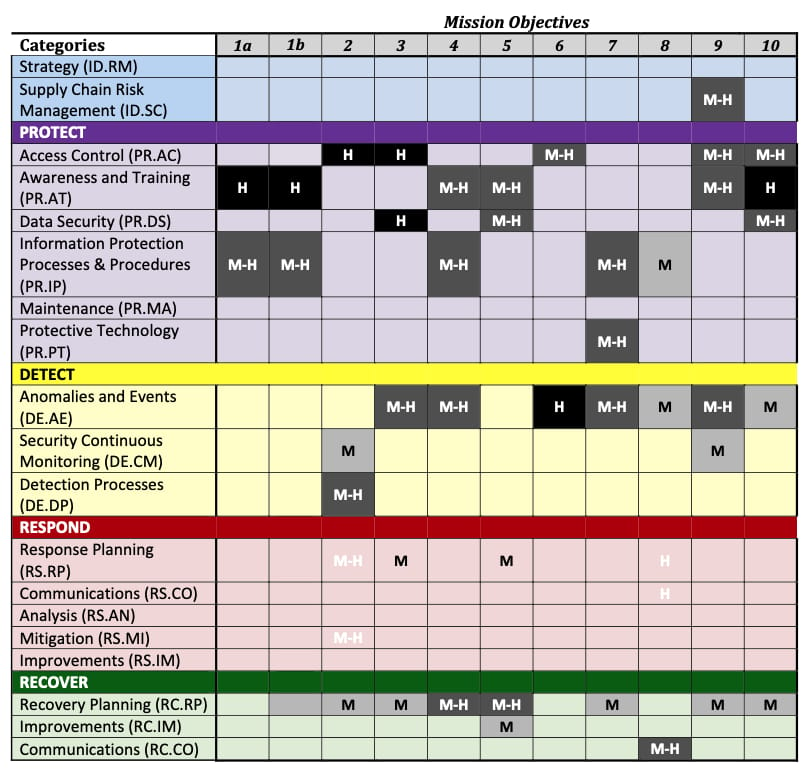
Identify the specific categories and subcategories that are most relevant to cyber resilience
Assess alignment and fit with the organization’s objectives and its risk management strategy
Step 3: Select and Prioritize Categories

No organization has enough time or money to focus on everything all of the time
Choices will have to be made
Prioritization is crticial
What are this organization’s unique cybersecurity challenges and focus areas?
Which categories will yield the highest return on security investment, to optimize cyber resilience?
Step 4: Define Subcategories and Activities

Within each selected category, define the specific subcategories and activities that will guide the organization’s cybersecurity efforts
These subcategories and activities provide a more granular level of detail and actionable steps to achieve the desired cybersecurity outcomes
Customize these subcategories and activities to align with the organization’s specific needs, resources, and risk landscape
Step 5: Establish Performance Goals and Metrics
Measure the effectiveness and progress of its cybersecurity practices
Take the time to define clear indicators
This helps to
Track improvements over time
Give management the data they need to make informed decisions about enhancing cybersecurity capabilities
Step 6: Document and Implement the Profile
By ensuring that the profile is well-documented, easily understood, and accessible to relevant stakeholders within your organization, you can more easily communicate the profile to the key personnel responsible for implementing and managing the organization’s cybersecurity program
During this step, it is also important to actually conduct the implementation of the profile by integrating the defined measures, controls, and practices into the organization’s cybersecurity operations
After the initial implementation is complete, it is important to periodically review and update the profile as the organization’s cybersecurity needs evolve over time
Profile Tailoring 🪡
Example Approaches for Limited Engagements
DETECT FUNCTION ONLY
2 categories
11 subcategories
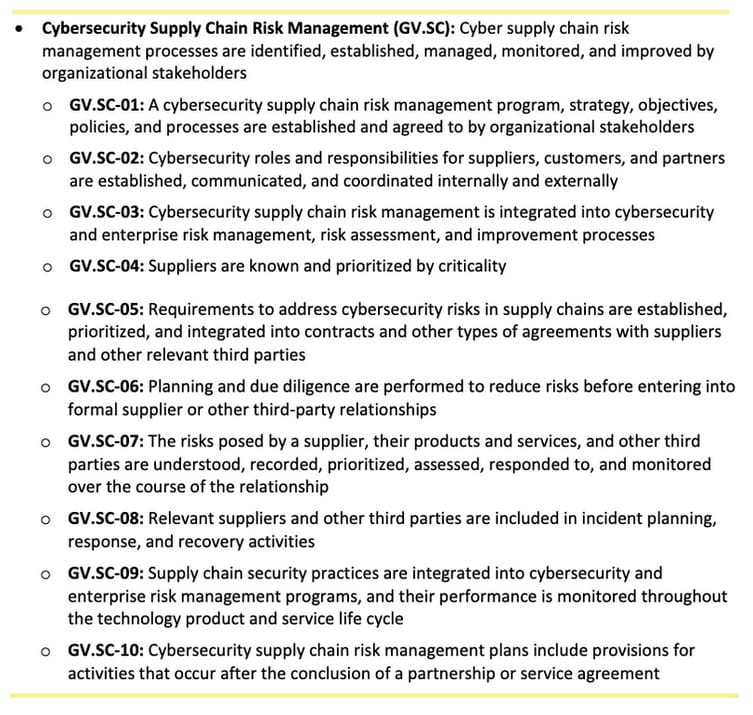
GOVERNANCE.Cybersecurity Supply Chain Risk Management (GV.SC) Category Only
10 subcategories
Example Short, Tailored Profile

CSF Category | CSF Description (NIST) | Profile Objective (Organization) |
|---|---|---|
Identity Management, Authentication, and Access Control (PR.AA): | Access to physical and logical assets is limited to authorized users, services, and hardware and managed commensurate with the assessed risk of unauthorized access | Establish robust identity management, authentication, and access control measures to safeguard sensitive data in our certification exam systems |
Awareness and Training (PR.AT): | The organization’s personnel are provided with cybersecurity awareness and training so that they can perform their cybersecurity-related tasks | Enhance cybersecurity awareness and provide effective training to our personnel and users to mitigate the risk of unauthorized access and security incidents |
CSF Subcategory | CSF Description (NIST) | Profile Subcategory (Organization) |
|---|---|---|
PR.AA-03 | Users, services, and hardware are authenticated | Users, services, and hardware are authenticated to ensure secure access to certification exam systems. |
PR.AT-01 | Personnel are provided with awareness and training so that they possess the knowledge and skills to perform general tasks with cybersecurity risks in mind | Personnel are provided with awareness and training so that they possess the knowledge and skills to perform general tasks with the cybersecurity risks of the certification exam systems in mind. |
Profile Templates 📄
Benefits
Consistency, efficiency, alignment with recognized cybersecurity best practices
Consistency across an organization or industry helps facilitate bench-marking, sharing of best practices and collaboration
Tips
Look for reputable sources like industry associations or government agencies, who have worked with a whole portfolio of organizations out in the field and learned from those experiences
Use as a starting point
Sections
Section | Description |
|---|---|
Summary | Concise overview Key objectives and focus areas |
Framework Components | Functions, categories, and subcategories |
Objectives | Desired outcomes to be achieved |
Activities | To meet the profile objectives |
Goals | To later assess the success and effectiveness of the profile implementation |
Metrics | To measure progress and performance |
Sector-Specific Profiles 🏭
Cyber Risk Institute (CRI) Profile
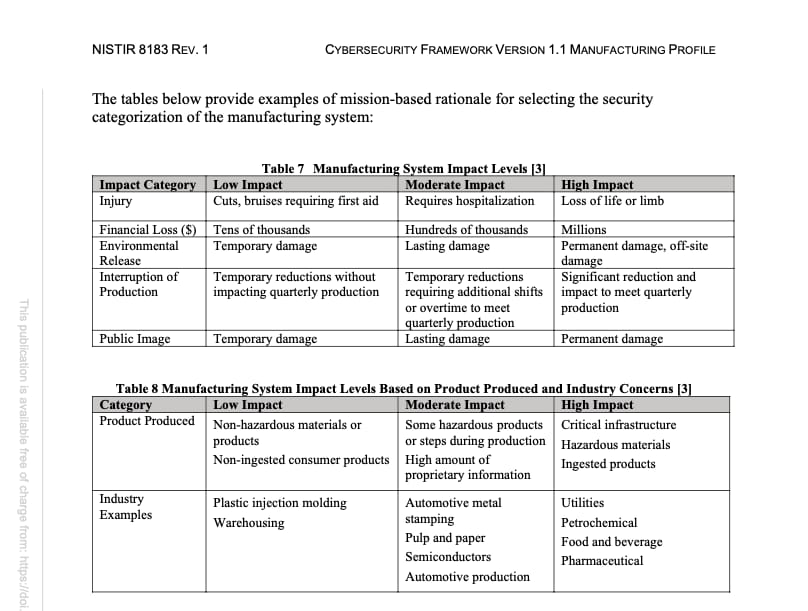
Manufacturing Profile
IT (Information Technology) networks
Manage and process data
Email, documents, spreadsheets, websites, file sharing
OT (Operational Technology) networks
Control and monitor physical processes, devices, and infrastructure in manufacturing
Includes Industrial Control Systems (ICS)
Supervisory Control and Data Acquisition (SCADA) systems
Distributed Control Systems
Programmable Logic Controllers (PLC)
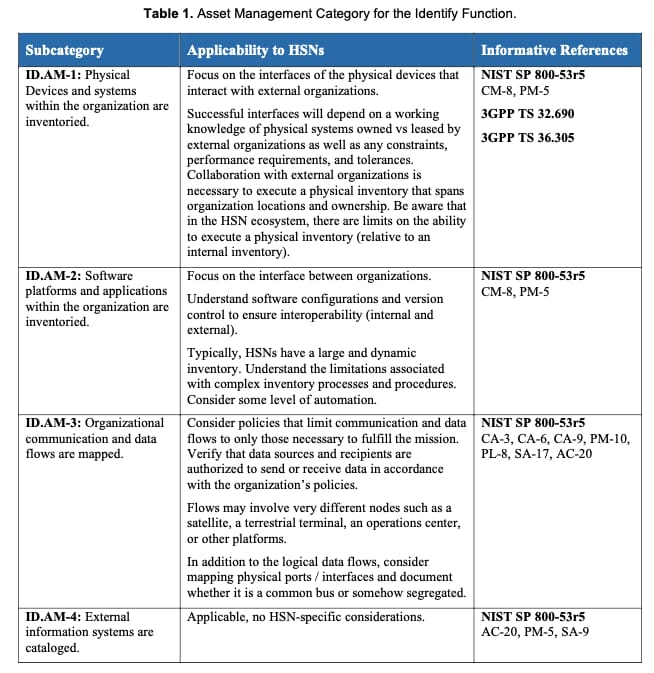
IDENTIFY Function Example
CSF v1.1 Subcategory PR.AC-5 Example

CSF v1.1 Subcategory | CSF v2.0 Subcategory |
|---|---|
PR.AC-05: Network integrity is protected | PR.IR-01: Networks and environments are protected from unauthorized logical access and usage |
Election Infrastructure Profile



Hybrid Satellite Networks Profile

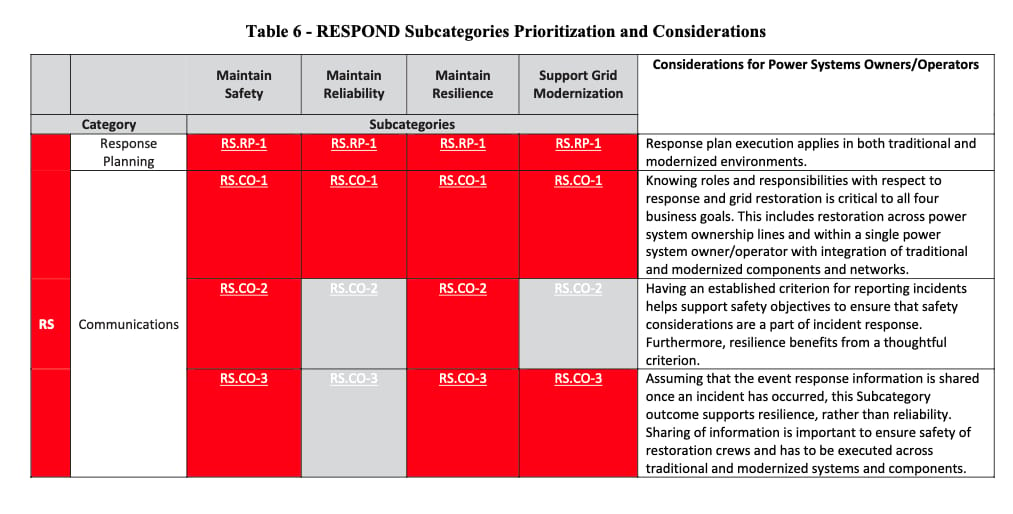
Smart Grid Profile
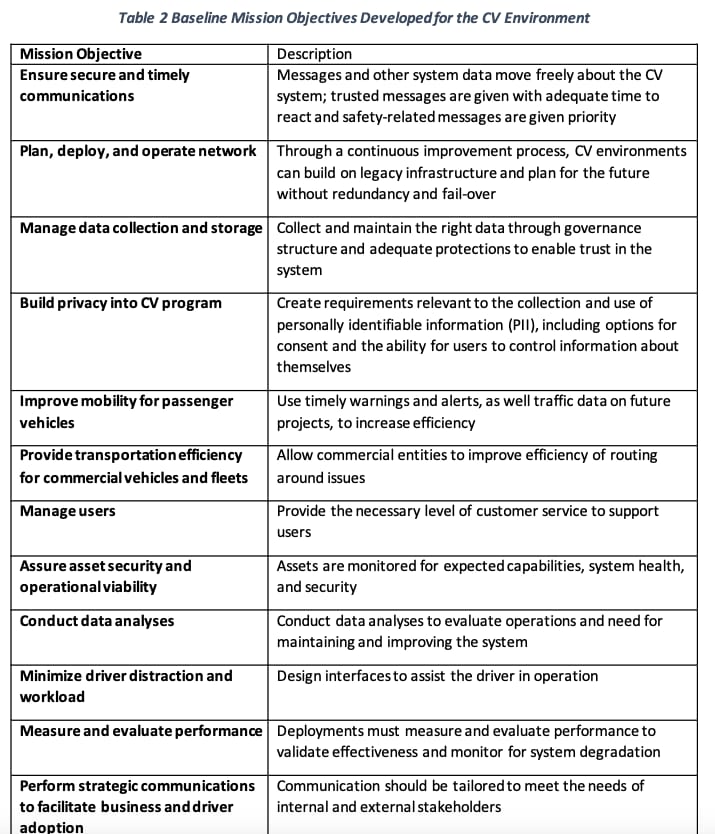
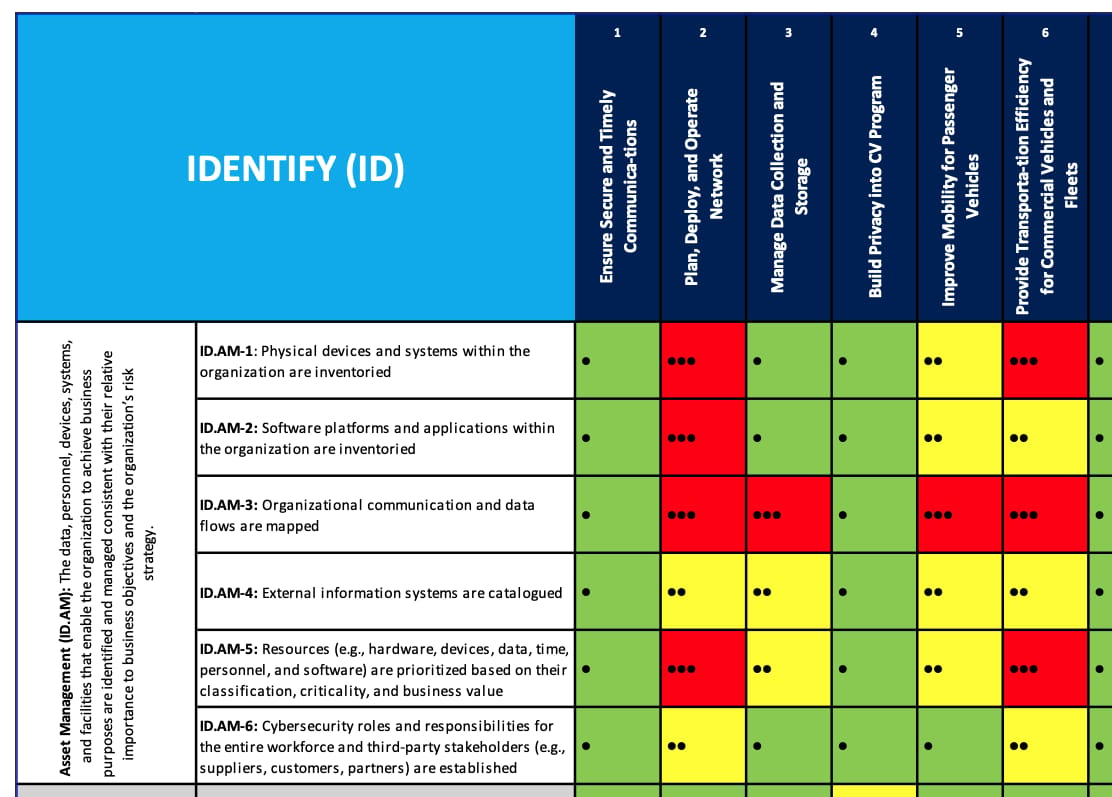
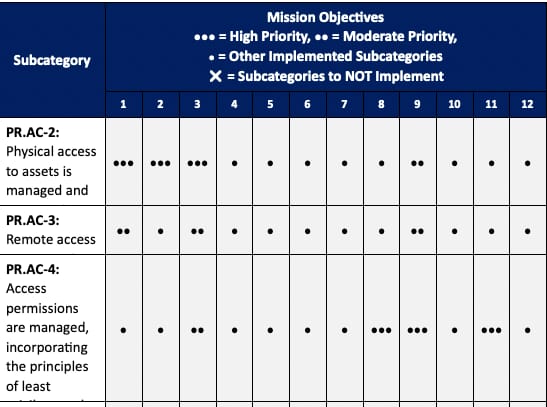
Connected Vehicle Profiles
Payroll Profile
Maritime Profile
Communications Profile
Profiles and Regulatory Compliance 🔍
Carefully assess requirements and map to CSF
While many industries have their own specific cybersecurity requirements and best practices that organizations must adhere to, customizing your CSF profile to include them ensures that your cybersecurity practices
Meet regulatory compliance
Adress the unique challenges and risks associated with their specific industry.
It establishes a structured and systematic approach to meeting compliance obligations.
Identify gaps
It helps identify gaps in current cybersecurity practices to then develop targeted plan to address
This approach enables organizations to demonstrate their commitment to regulatory compliance, enhance their security posture, and mitigate potential risks associated with non-compliance
Secure Once, Comply Many ✔️
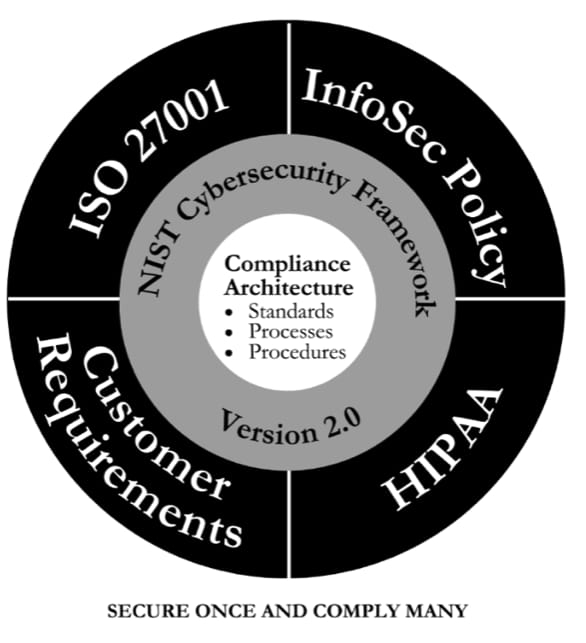
Mastering Cyber Resilience, p. 147, AKYLADE
Benefits of this Compliance Architecture:
Remove guesswork
Simplify
Map all compliance requirements to outcomes
Check new mandates against current framework
Make it easier to operationalize the framework
Spend less time and money implementing controls
Get more consistent execution
HIPPA Requirement | CSF v2.0 | ISO27001 |
|---|---|---|
164.308(a)(7)(ii)(A): Data Backup Plan “[e]stablish and implement procedures to create and maintain retrievable exact copies of electronic protected health information” | PR.DS-11: backups of data are created, protected, maintained, and tested | A.12.3.1 Information backup A.17.1.2 Information security continuity A.17.1.3 Verification of continuity plans A.18.1.3 Protection of records |
Conclusion and Touchpoints ✅
Profiles
Customizable Approach
Profile Templates
Sector-Specific Templates
Align Profiles with Regulatory Compliance