Table of Contents
1.1 - Understand, adhere to, and promote professional ethics
ISC2 Code of Professional Ethics
Organizational code of ethics
Notes:
Code of Ethics Cannons
Protect society, the common good, necessary public trust and confidence, and the infrastructure.
Act honorably, honestly, justly, responsibly, and legally.
Provide diligent and competent service to principals.
Advance and protect the profession.
Distractor:
1.2 Understand and apply security concepts
Confidentiality, integrity, and availability, authenticity and nonrepudiation
Authenticity: Genuine. Verified to be from claimed origin. Not a deep fake! Hash signed by my private key, decrypted with public key
Non-repudiation: subject of an activity can’t deny that an event occurred or was done by someone else. Threat actor identity is known and they can’t cover their tracks.
1.3 - Evaluate and apply security governance principles
Alignment of the security function to business strategy, goals, mission, and objectives
Organizational processes (e.g., acquisitions, divestitures, governance committees)
Organizational roles and responsibilities
Security control frameworks
Due care/due diligence
Governance outcome: everyone knows the company’s risk appetite, and makes decisions aligned to it
Starts with the Board
COBIT
Governance related but in the Security Control Frameworks section
The COBIT toolkit has a spreadsheet with objectives and practice descriptions
E.g. Align, Plan & Organize APO07.01 “Evaluate internal and external staffing requirements…”
Key principles
End-to-End Governance System
Concerned with value delivery from digital transformation and mitigation of associated business risk
Provide Stakeholder Value
3 main outcomes
Benefits realization
Risk optimization
Resource optimization
Holistic Approach
Not limited to the IT department
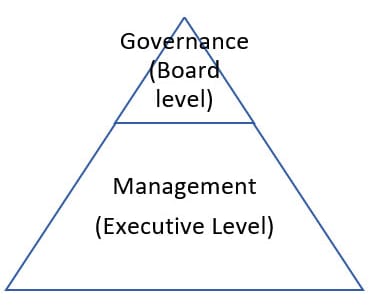
Governance Distinct from Management
Dynamic Governance System
Tailored to Enterprise Needs