Hey there,
Did you catch Dr. Gerald Auger’s excellent video on Third Party Risk Management (TPRM)? It’s yet another Simply Cyber must watch, not just because of the valuable knowledge you can apply, but it’s 100x more fun that anything else YouTube has seen on the topic! Cool also that TryHackMe gave the GRC domain a nod by including this module in Advent of Cyber. It’s a concrete step towards GRC getting more “socially acceptable” to quote Dr. Auger, or recognized as being awesome and underrated as I like to say.
Why does TPRM (also called SCRM - Supply Chain Risk Management) matter? We see supply chain cybersecurity incidents in headlines everyday, and we’re only getting more dependant on third parties. 📈
One driver is complexity, which NIST Fellow Dr. Ron Ross points out is the biggest cyber threat we face today:
Trillions of lines of code in billions of devices, with ubiquitous connectivity across the globe.
Another is concentration risk associated with the “magnificent 7” tech titans that have emerged in our economy, that are uniquely positioned for further industry disruption with AI, beyond what what we’ve already experienced with cloud, mobile and other big transformations.
The Magnificent Seven contributed 58% fo the S&P 500’s total return in 2023. Historically, the top 10 stocks in the S&P500 contribute 14% of the index’s total return, showing the current over-concentration
The growing importance of SCRM for these reasons and more is why we saw NIST Cybersecurity Framework increase emphasis on it both in their version 1.1 in 2018 and 2.0 in 2024.
In this blog I’ll provide my perspective on key points Dr. Auger walks through, and connect it to Mastering Cyber Resilience material and my experiences, to drive these concepts home to help you maximize outcomes as a GRC practitioner or a cybersecurity consultant.
Check it out and let me know what you think!
Be safe, be well,
Steve
Contents
What is GRC?
GRC is an acronym that stands for Governance, Risk, and Compliance. Each of these are kind of independent of each other and we'll break down each of them. But they basically ensure that an organization has a methodical and intelligent approach to driving cyber risk reduction.
Mission Impossible? Unlimited Cyber Threats vs Limited Resources
As the cliche goes, cybersecurity is hard.
Two key points to wrap our heads around in the context of this lesson:
It’s not JUST that there’s infinite cyber risk and limited resources
Cybersecurity and cyber resilience are not something that you can just write a cheque to solve faster
Even if you had infinite money - here's a blank check, go buck wild, you got a genie with three wishes and the first wish you wish for is infinite money, good for you - you know what you can't do?
You can't buy all the tools. You can't train all the staff. You can't keep staff who know what they're doing there because they might go to another place. So infinite money doesn't equal infinite security.
It’s like the project management analogy that pregnancy takes 9 months - you can’t spend money to shorten that timeframe
Or the saying that “you can’t rack and stack security culture” - it’s not something you can buy off the shelf and plug in.
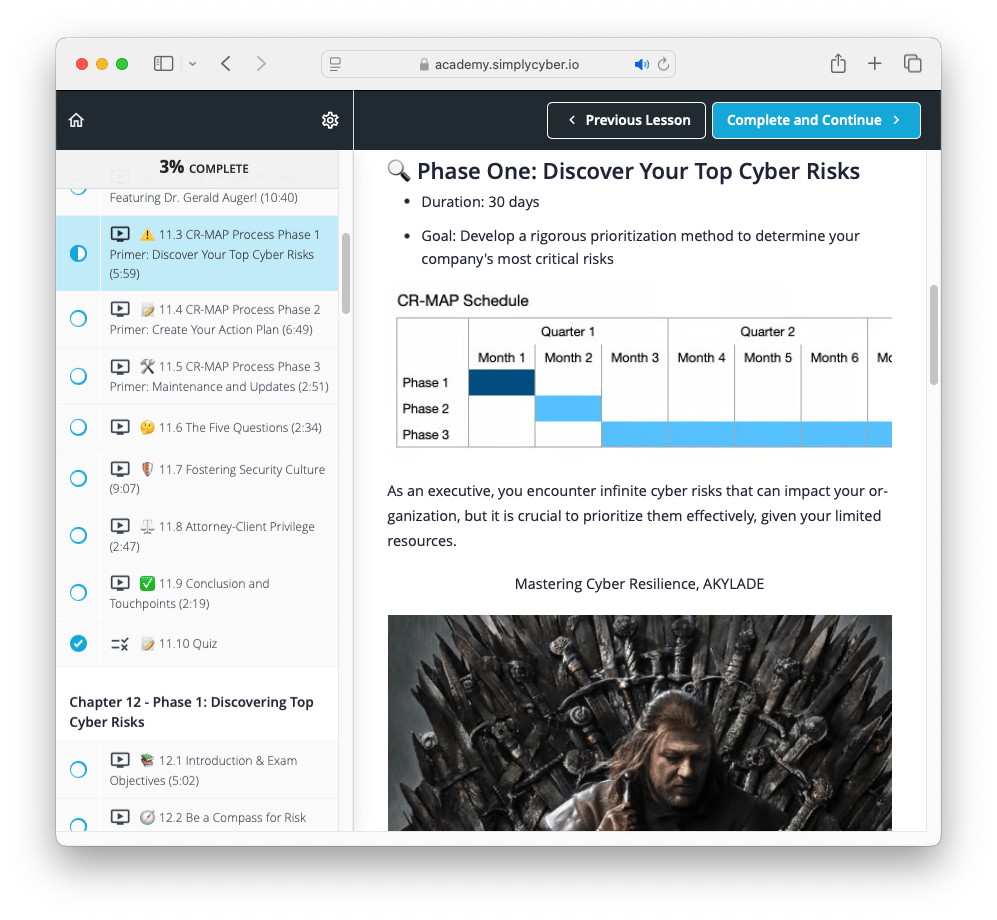
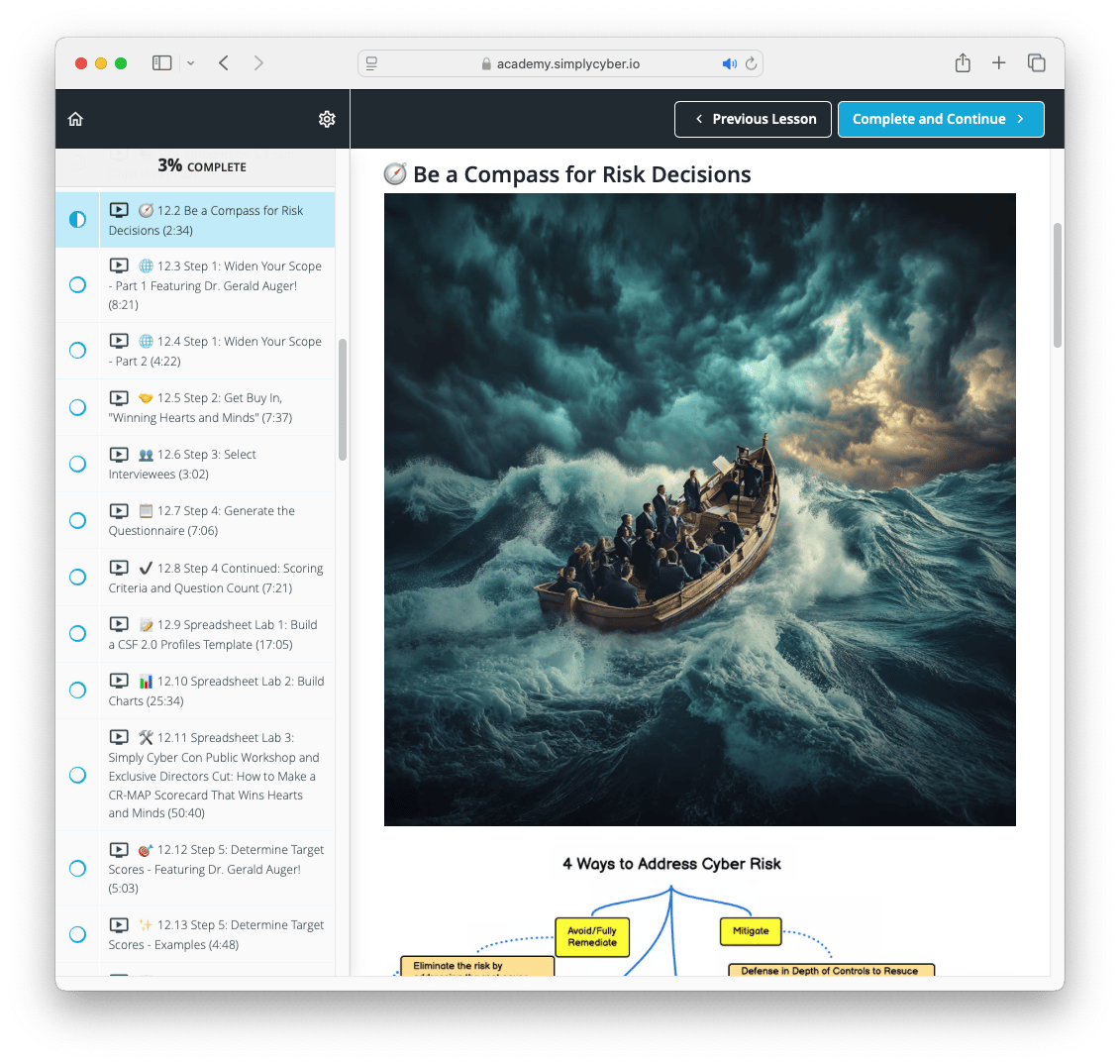
As Kip Boyle points out in Fire Doesn’t Innovate and Mastering Cyber Resilience, cyber risk management needs a comprehensive assessment of people, process, management and technology
But in reality, we don't have infinite money. We don't have infinite resources or infinite time. So what we need to do is figure out where we need to spend our money, what we need to prioritize first, and who's going to do the work and how they're going to do it. This is what GRC basically is - looking at and thinking of.
Also, bonus tip: there's actually academic research that shows there's diminishing returns the more money you put in. I.E. if I give you a million dollars, you can get your InfoSec program to pretty good. If I gave you another million dollars, you wouldn't double the effectiveness of your cyber program. It would only be like a percentage of that. So there's a logarithmic curve.
Identifying reasonable places in the risk to cost of control curve, in the trade-off of protecting and enabling the business is the key
The 0-10 score key in Mastering Cyber Resilience from Insecurity to Too Much Security is a helpful guide to find the appropriate Goldilocks zone in your assessments
This score key is included in my Simply CYBERCON workshop, How to Make a Cyber Risk Scorecard that Wins Hearts and Minds

Governance Explainer
Governance is basically what are the rules of the business and what is the attitude of the business? What is normal at this business? And then having leadership be like, "No, this is important."
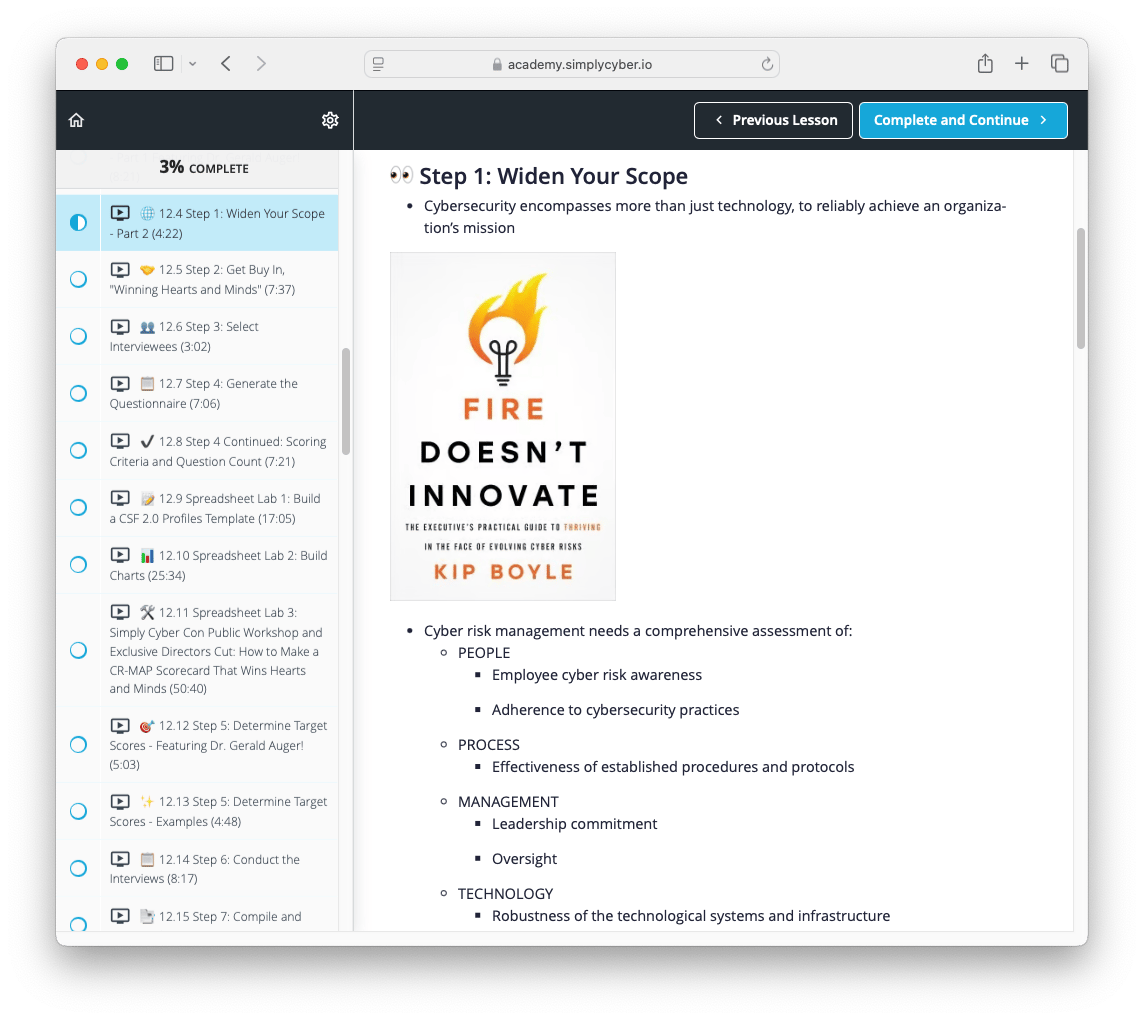
You’ve heard that cyber risk management is the perfect storm
Your Cyber Risk Management Action Plan work provides the executive team a compass to steer through it
Governance can also include frameworks. I'm a huge fan of the NIST Cybersecurity Framework and CIS Top 18.
Frameworks are great and it allows you a repeatable, mature process in order to grow into a mature InfoSec program and make sure that you're hitting comprehensively all the elements of a cyber program. Making sure that you're looking at people, process, technology - not just saying "Oh, we're taking backups and we've got multi-factor, we're good to go." Yeah, okay, but are you doing configuration management? Are you doing vulnerability management? Are you regularly pen testing your environment? Are you doing risk assessments? Who's allowed to access what? Do you revoke credentials if they get compromised? Who's allowed to do that? A million things!
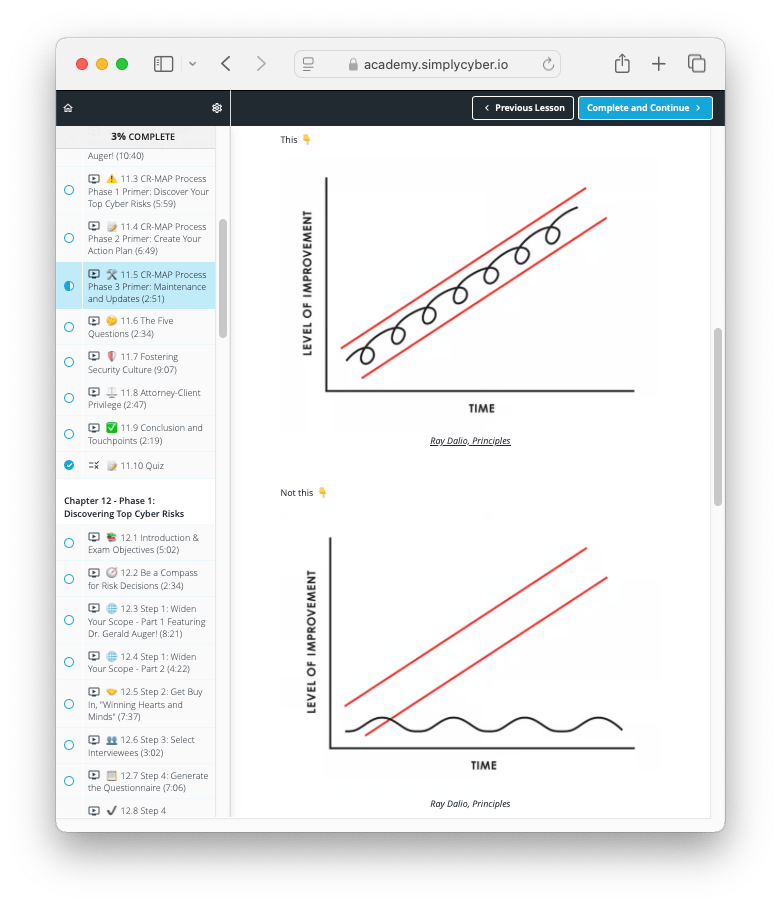
Follow the Simply Cyber mantra “Lather, rinse, repeat” to grow into a mature InfoSec program!
Being comprehensive is key for demonstrable due diligence and due care
That “comprehensive” word pops up in places like the FTC Safeguards Rule of 2023 for financial data, that is used in the court of law and the court of public opinion

Another insight related to comprehensiveness in the Governance function, is establishing clear expectations in policies
Turn on your negative mindset for a moment to risk assess a malicious insider attack scenario, where an insider harms your company and your colleagues, in a way that seems really bad
If your policies weren’t comprehensive enough by being baselined against an industry framework, the justice system is going to have a hard time being effective, because the malicious insider can say, “I didn’t know that wasn’t’ allowed”
Not legal advice here, of course, but food for thought
Compliance Explainer
And then finally, compliance. This is like your on-ramp to GRC. Compliance is straightforward. There's a list of documented requirements, whether it's PCI (Payment Card Industry), or it is HIPAA (the Health Insurance Portability and Accountability Act). I don't want to say compliance is easy, but compliance is easy to understand. Here's a bunch of things: are you doing them? Yes or no. This is where a lot of GRC people actually start in their career because you audit against the compliance standard.
Some industry resources to check out here are ISO27k, NIST Special Publications, CRI, CIS CSC, COBIT 5, ITIL, PCI DSS, HIPPA, NERC CIP, FedRAMP, STAR and OWASP
Risk Explainer
Let's talk about the next one: risk. What is risk? Again, like I said before, you can't secure all the things. You will always, always, always have residual risk. I don't care what you're doing, what industry, what size org - you will always have residual risk. So it's managing how much of that residual risk exists with respect to funding or budget, manpower or person power, and just resources like time and stuff.
"Oh cool, Security Onion, what a great tool! Let's roll it out." Okay, well what are you going to put down in order to roll out Security Onion? "Oh, I didn't think about that." And once you roll it out, who's going to manage it, maintain it, care and feed it? I can't tell you - honestly, quick side note - I can't tell you how many abandoned projects I've seen in my career. People get all geeked up like "Oh, let's roll out Security Onion!" And then like a month later, you've got it rolled out and then nobody's using it because nobody's managing it. And then it's like, "Oh, that was a lot of fun."
An action plan to implement Security Onion didn’t consider people or process elements to go with the technology
➡ Back to STEP 1: 👀 Widen Your Scope
It also wasn’t reasonable and repeatable 🔄, in the appropriate place for the risk to cost of control curve
That's what risk is. We need to understand what is the risk of doing something, what is the risk of not doing something.
Multi-factor authentication - perfect example. In my opinion, should be rolled out everywhere. But maybe some organizations don't want to put it on the executives for whatever reason. They're special snowflakes and they don't want to use multi-factor because it's hard. Well, you could say, "Okay, we are taking on additional risk because
(a) if you reuse passwords or you have crappy passwords, business executives, you're probably going to get your account cracked.
(b) Secondly, without MFA, they're going to walk right through. This could lead to business email compromise, loss of revenue. This could lead to phishing or social engineering of staff and other problems. This could lead to a compromise of reputational harm because you're a publicly traded company and sensitive financial forecasting data gets out because they're in your account."
Is that the kind of risk you want to take on? Maybe you don't say it in that way to the executives - there's a much more polished way to do it. But my point is, this is risk and it's what we GRC folks are responsible for managing, maintaining, and keeping an eye on. Because risk is a very fluid, very dynamic element.
There are four ways to address cyber risk: mitigate, avoid, transfer or accept
The default position is acceptance: if your organization isn’t cyber threat aware, they might be accepting and holding onto a bigger bag of risk than they realize

On Dr. Auger’s note about having a “polished” way to explain risk treatment options, this is crucial and I don’t think well understood
Rather than shaming end users and applauding threat actors, dial up your emotional intelligence quotient to meet your audience where they are on cyber risk awareness, and tell them what they need to know
Here’s my attempt with Uncle Carl at a barbecue
Risk Assessments
Holler! Let's talk risk assessments. Risk assessments is what it sounds like. There's risk - I just flipped out about that for a minute - and a risk assessment is basically a deliberate method of going through and looking at your, you know, either looking at an application, looking at a system, looking at an overall enterprise, and figuring out where the weaknesses are. And then discovering how bad those weaknesses are, specifically, because some weaknesses aren't such a big deal.
Classic example: you got a Windows XP machine running, which would be disgusting, but it's in a lab environment, air-gapped from the internet. Who cares?
You can see here McSkidy and Grinch are going to basically hand out a third-party questionnaire, which basically gets information solicited from third parties. That information comes in and then based on that information, we're going to assess the risk of their security posture and them holding our data.
We’re getting into GV.SC-07 here: “The risks posed by a supplier, their products and services, and other third parties are understood, recorded, prioritized, assessed, responded to, and monitored over the course of the relationship”
Third Party Risk Assessments work well as a checkpoint during the Procurement process, and should be tailored (in terms of due diligence and friction to the business trying to buy something) to the risk level of the third party. RIsk level is commensurate to:
The security classification of the data on your network that will traverse to the third parties network
Access the third party might require to your network.

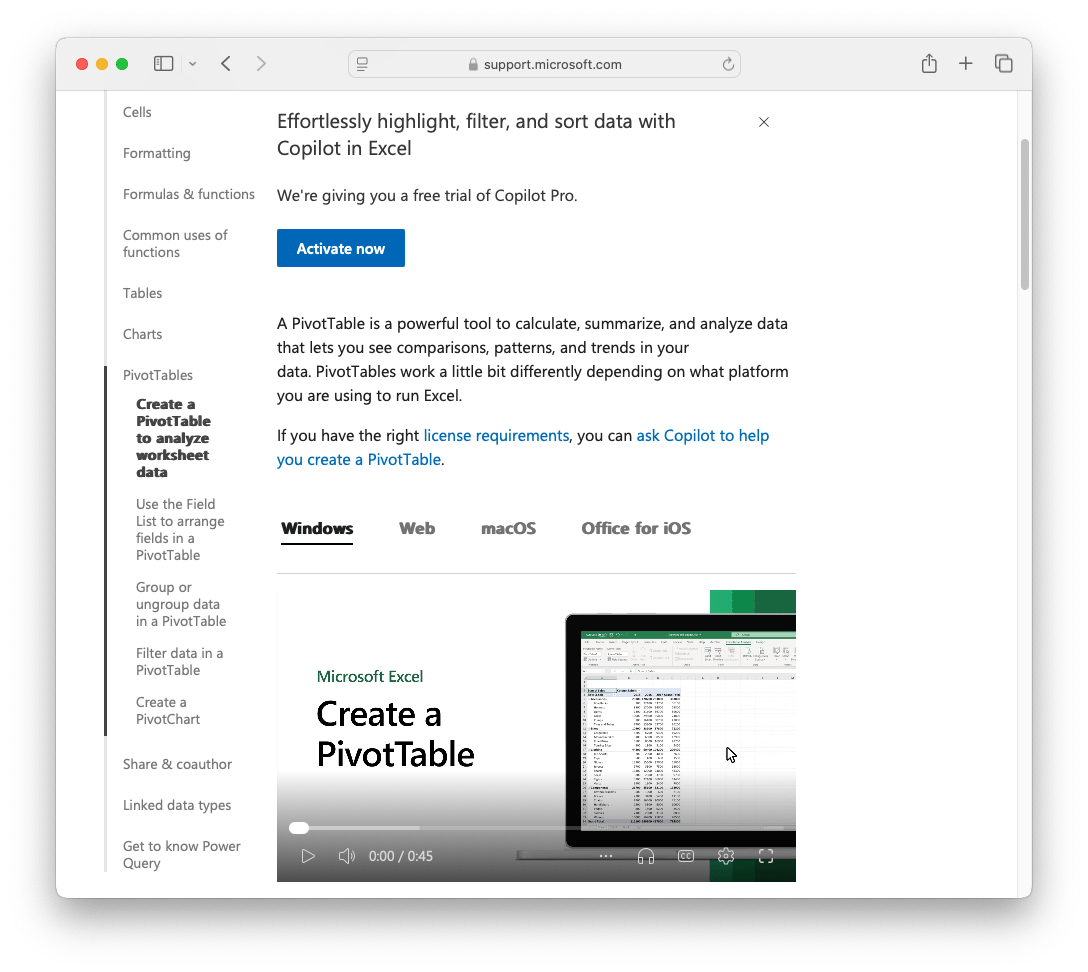
Spreadsheets (Like GRC) Are Awesome and Underrated, for Fit-For-Purpose Data Analysis
Ah, here we go. Be still my heart - the spreadsheet. This is, you know, like if a cowboy has a pistol and a holster on his hip, a GRC professional has a spreadsheet in the holster on the hip. I know there's all sorts of fancy tools, but I'm telling you right now, the spreadsheet - and once you pick up pivot tables, oh my goodness, slow down!
It’s so great to find Dr. Auger sharing not just contrarian view point that GRC can make an outsided impact, but Excel too for fit-for-purpose tasks!
With GRC it’s about interfacing between the business and technical teams to prioritize limited resources against unlimited cyber threats. With spreadsheets its about ad hoc data analysis to extract actionable insights from large and disparate data sets. There’s a reason Excel is one of the most searched for topics in e-learning.
Just make sure it’s the right tool for the job.
To learn about Excel Tables, Slicers, Formulas like XLOOKUP, Pivot Tables, Charts and Power Query so you can “invert the power dynamic between yourself and executives,” check out my Simply CYBERCON workshop that demonstrates these capabilities, and don’t hesitate to let me know if you have any questions.
Or if you just want to know the top 2 highest Return On Investment Data Analytics techniques in Excel, here they are:
1. XLOOKUP
XLOOKUP is an easier and more powerful, adaptable approach for joining data sets than VLOOKUP, if you’ve heard of that very popular formula.
2. Pivot Tables
Once you have clean and comprehensive underlying data, Pivot tables can quickly extract insights from it, by rolling up, drilling down, slicing and dicing for analysis.
Vendor Security Questionnaire Assessment
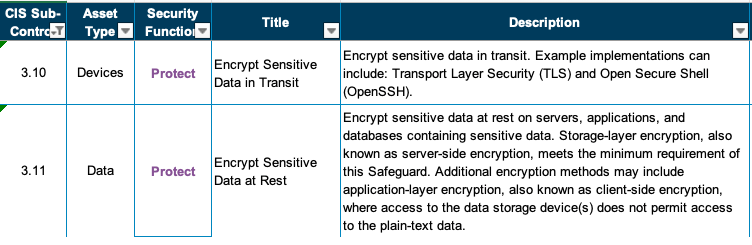
Question 1: PR.DS Protecting Data in Transit and at Rest
We want to know about data in transit and at rest needs to be encrypted with AES as a requirement. Maybe it's contractually required; maybe it's a business policy that you need AES, which is currently considered secure—AES 256 or higher. What type of AES encryption does your company use for data? Remember, they're holding our sensitive data. The vendor response here is AES 256 for in transit and AES 256 for data at rest. This is right on; I like this one.
If the impact were to get compromised, there would be for sure significant impact of the data. The potential security risk here—we're going to document that this is where the GRC risk assessment piece comes in. It's not very high honestly but data captured and later decrypted—I don't think this is very likely to happen honestly. Quantum computers are where we're at right now, so I'll leave this unlikely but the impact would be high if it were to happen. Let's go ahead and click add risk.

NIST CSF Category Lookup: PR.DS-01 and PR.DS-02
CSF Subcategory ID | Implantation Example(s) |
|---|---|
PR.DS-01: The confidentiality, integrity, and availability of data-at-rest are protected | Ex1: Use encryption, digital signatures, and cryptographic hashes to protect the confidentiality and integrity of stored data in files, databases, virtual machine disk images, container images, and other resources |
PR.DS-02: The confidentiality, integrity, and availability of data-in-transit are protected | Ex1: Use encryption, digital signatures, and cryptographic hashes to protect the confidentiality and integrity of network communications |
Informative References
CIS Controls v8.0
3.11 Encrypt Sensitive Data at Rest
SP 800-53 Rev 5.1.1
CA-03: Information Exchange
CP-09: System Backup
MP-08: Media Downgrading
SC-04: Information in Shared System Resources
SC-07: Boundary Protection
SC-12: Cryptographic Key Establishment and Management
SC-13: Cryptographic Protection
SC-28: Protection of Information at Rest
SC-32: System Partitioning
SC-39: Process Isolation
SC-43: Usage Restrictions
SI-03: Malicious Code Protection
SI-04: System Monitoring
SI-07: Software, Firmware, and Information Integrity
CIS Controls v8.0
3.10 Encrypt Sensitive Data in Transit
SP 800-53 Rev 5.1.1
AU-16: Cross-Organization Audit Logging
CA-03: Information Exchagne
SC-04: Information in Shared System Resources
SC-07: Boundary Protection
SC-08: Transmission Confidentiality and Integrity
SC-11: Trusted Path
SC-12: Cryptographic Key Establishment and Management
SC-13: Cryptographic Protection
SC-16: Transmission of Security and Privacy Attributes
SC-40: Wireless Link Protection
SC-43: Usage Restrictions
SI-03: Malicious Code Protection
SI-04: System Monitoring
SI-07: Software, Firmware, and Information Integrity
CIS Controls
Encryption in transit examples:
Sending an email, from your laptop to a 3rd party Gmail server to the person’s phone you sent it to
Or saving a document on Sharepoint - that file goes from the computer to your cloud to your colleagues
Or typing in your password to log into a service - that’s sensitive data that encryption helps to keep confidential
TLS (Transport Layer Security)
A handshake between an end users web browser, and a back end server, establishing an encrypted session that puts a padlock beside the URL in your browser
SSH (Secure Shell)
Typically used in the Command Line Interface (CLI) for remote management of servers and network hardware.
Frequently used in automated scripts for remote system updates, backups and administrative tasks, or in an Integrated Development Environment (IDE) for connecting to version control systems, remote debugging and deploying applications
Encryption at rest examples:
Operating systems
Bitlocker (WIndows)
Veracrypt (Windows, Ubuntu, macOS)
FileVault (macOS)
Database encryption
Data files on the disk, backup files, logs
Mobile device encryption
Modern hard drives and solid-state drives (SSDs)
NIST SP 800-53
SC-12 Cryptographic Key Establishment and Management
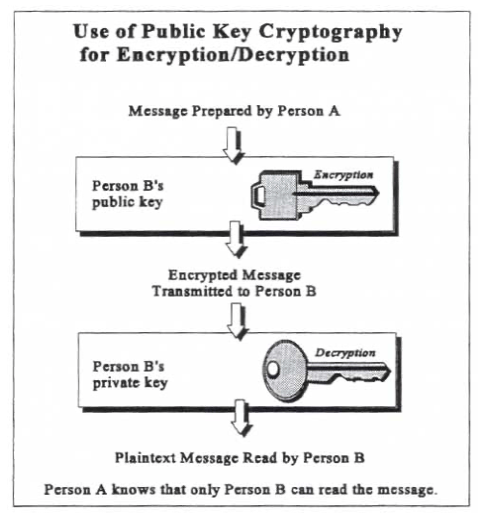
There are two main types of encryption:
Distinct Features | Symmetric (Secret Key) Cryptography | Asymmetric (Public Key Cryptography) |
|---|---|---|
Number of Keys | Single Key | Pair of keys |
Types of Keys | Key is secret | One key is private, and one key is public |
Protection of Keys | Disclosure and modification | Disclosure and modification for private keys and modification for public keys |
Relative Speeds | Faster | Slower |
Asymmetric Encryption
Symmetric Encryption
Uses the same key for both encrypting and decrypting data (block cipher). This key must be shared and kept secret between the sender and the recipient
Examples are AES (Advanced Encryption Standard) and DES (Data Encryption Standard)
Typically faster than asymmetric encryption and is commonly used for encrypting large amounts of data
Often used for encrypting data at rest, such as files on a hard drive, or data in transit in scenarios where secure key exchange has already occurred
SYMMETRIC KEYS
Produce, control, and distribute symmetric cryptographic keys using [Selection: NIST FIPS- validated; NSA-approved] key management technology and processes.
Discussion: [SP 800-56A], [SP 800-56B], and [SP 800-56C] provide guidance on cryptographic key establishment schemes and key derivation methods.
SP 800-56A: Recommendation for Pair-Wise Key Establishment Using Discrete Logarithm Cryptography
Use of asymmetric (public key) cryptography to securely establish symmetric (shared keys) between two parties.
Although SP 800-56A is primarily about key exchange mechanisms like Diffie-Hellman (DH) and Elliptic Curve Diffie-Hellman (ECDH), the secure keys established can be used with symmetric key algorithms like AES-256 for encrypting data in transit.
AES is considered a “well established cryptographic scheme”
AES is defined in FIPS-197
AES-256 has the largest key length and number of rounds
FIPS-197: Advanced Encryption Standard (AES)
FIPS-198: The Keyed-Hash Message Authentication Code (HMAC)
HMAC (Hash-Based Message Authentication Code) can be used in conjunction with AES (Advanced Encryption Standard) to provide both encryption and integrity protection for data in transit
For example, in a typical TLS session, AES might be used to encrypt the data being transmitted, while HMAC is used to ensure the data integrity and authenticate that the data has not been tampered with during transit
SP 800-56B: Recommendation for Pair-Wise Key Establishment Using Integer Factorization Cryptography
Like 800-56A, it's about secure key exchange, but based on RSA encryption methods.
The keys established can similarly be used with symmetric encryption algorithms such as AES-256 for secure data transmission.
NIST SP 800-56C: Recommendation for Key-Derivation Methods in Key-Establishment Schemes
Key derivation methods are another crucial process that we don’t want to become the weak link
Even if AES-256 encryption is robust, the security of the encryption scheme is largely dependent on the secrecy and integrity of the keys used. If keys are derived or managed poorly, the strength of AES-256 can be undermined
If our vendor adheres to these guidelines, it can add a layer of trust in how they handle key management
Question 2: PR.AA-05 Access Permissions | Principle of Least Privilege
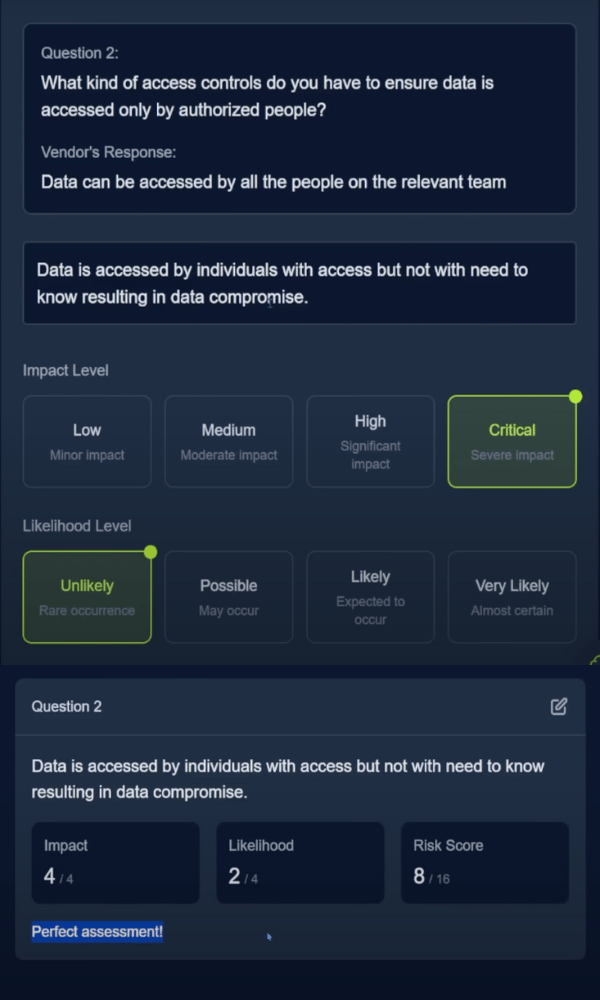
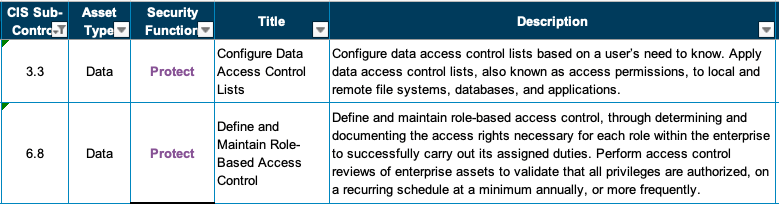
Alright, so let's go to question two: What kind of access controls do you have to ensure data is accessed only by authorized people? This is very important; access control is huge especially in a modern society where we're doing all sorts of partnering in cloud services and stuff. The vendor here, Violet Wolf, says data can be accessed by all the people on the relevant team. This is decent controls but there may be people on the team who don't really need access—so financial planner, a project manager, contractors that are supporting the team but not directly required to access the data. There is a little bit of a risk here; basically you want ideally only people with a need-to-know to have access—least use or least privilege is the control if you want to look it up in NIST 853.
The risk here is that data is accessed by individuals with access but not with need-to-know resulting in data breach or at least data compromise. Again, if people are getting access to this where they shouldn't—severe impact—this remember GRC and qualitatively assessing the impact and likelihood of a risk is very subjective; it's very fluid. This is why we have discussions about this and you're able to add additional controls to reduce or mitigate down risk levels to acceptable levels.
In this instance we'll say the impact is critical but anytime you make a decision on impact and likelihood you must absolutely be ready to defend it in a meeting because basically what you're saying is we need to invest more into security to reduce the risk to acceptable levels or you're saying we're not going to use this vendor and potentially cost this vendor millions of dollars or cost our business more money because the other vendors are more expensive. Just whenever you're choosing your values it's not just close your eyes and whack-a-mole; it's like literally you have to be able to defend this.
NIST CSF Category Lookup: PR.AA-05
CSF Subcategory ID | Implementation Example(s) |
|---|---|
PR.AA-05: Access permissions, entitlements, and authorizations are defined in a policy, managed, enforced, and reviewed, and incorporate the principles of least privilege and separation of duties | Ex1: Review logical and physical access privileges periodically and whenever someone changes roles or leaves the organization, and promptly rescind privileges that are no longer needed Ex2: Take attributes of the requester and the requested resource into account for authorization decisions (e.g., geolocation, day/time, requester endpoint's cyber health) Ex3: Restrict access and privileges to the minimum necessary (e.g., zero trust architecture) Ex4: Periodically review the privileges associated with critical business functions to confirm proper separation of duties |
Informative References
CIS Controls v8.0:
SP 800-53 Rev 5.1.1:
AC-01: Access Control Policy and Procedures
AC-02: Account Management
Authorize access to the system based on:
A valid access authorization;
Intended system usage; and
[Assignment: organization-defined attributes (as required)];
AC-03: Access Enforcement
Role-based access control (RBAC) is an access control policy that enforces access to objects and system functions based on the defined role (i.e., job function) of the subject.
AC-05: Separation of Duties
AC-06: Least Privilege
Employ the principle of least privilege, allowing only authorized accesses for users (or processes acting on behalf of users) that are necessary to accomplish assigned organizational tasks.
AC-10: Concurrent Session Control
AC-16: Security and Privacy Attributes
AC-17: Remote Access
AC-18: Wireless Access
AC-19: Access Control for Mobile Devices
AC-24: Access Control Decisions
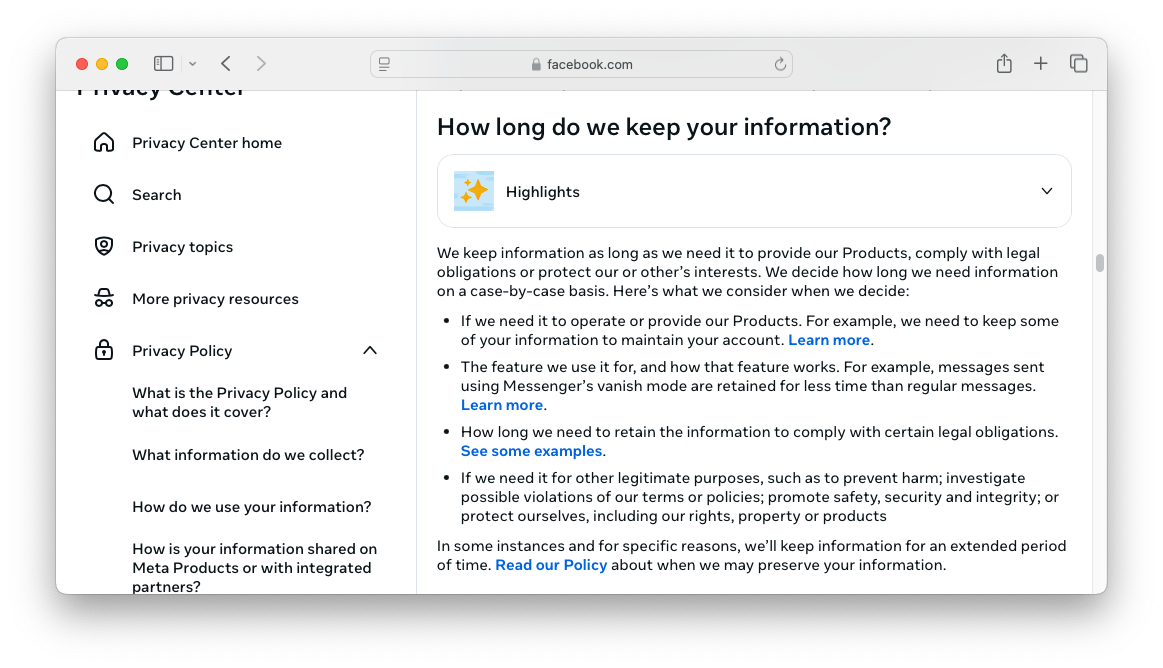
Question 3: ID.AM-8 Data Lifecycle | Securely Dispose of Data
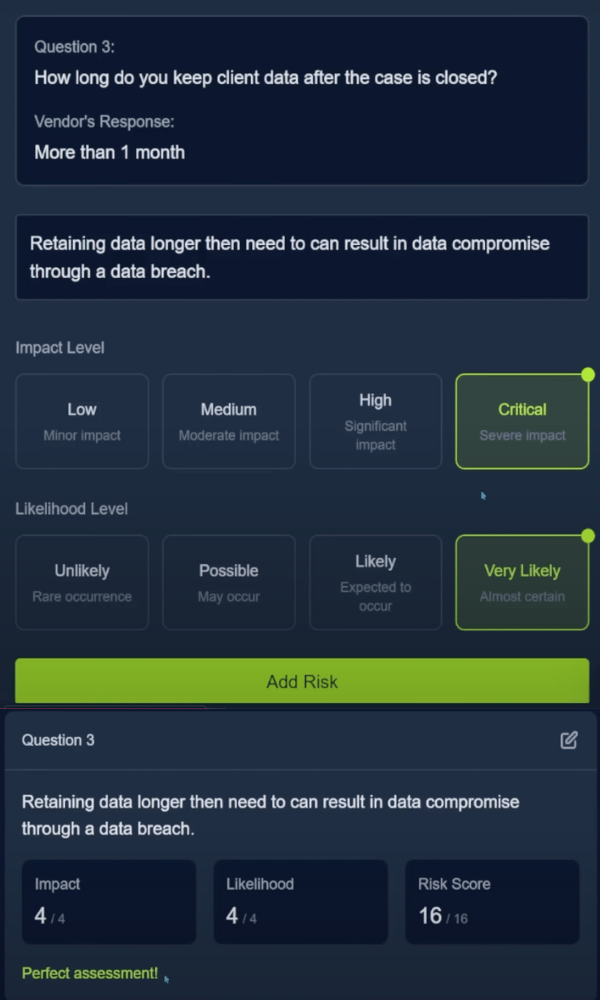
Okay so now let's go to question three: How long do you keep client data after the case is closed? This is a data governance issue—a data retention issue—more than a month is not good; they shouldn't be keeping it longer than they need to.
Data breach—retaining data longer than needed can result in data compromise through a data breach. Honestly you see this all the time with third-party data breaches—literally all the time—and it stinks because typically the business like our business in this case would be the one getting raked through the news and the mud—not the company that held our data. Go look at like the Snowflake breach recently or go look at what CL0P ransomware did with Progress MOVEit software last summer—you know what I mean? The companies that are impacted are not the ones that actually had the data breach.
This is literally the risk we're trying to deal with—significant impact—it would be really bad frankly; it wouldn't jeopardize catastrophic business operations but it would be a pretty high impact. More than a month—I mean you're basically dancing with fire so I'm going to say expected to occur.

NIST CSF Category Lookup: ID.AM-08
CSF Subcategory ID | Implementation Example(s) |
|---|---|
ID.AM-08: Systems, hardware, software, services, and data are managed throughout their life cycles | Ex7: Securely destroy stored data based on the organization's data retention policy using the prescribed destruction method, and keep and manage a record of the destructions |
Informative References
CIS Controls v8.0: 1.1 CIS Controls v8.0: 3.5

SP 800-53 Rev 5.1.1:
CM-09: Configuration Management Plan
CM-13: Information System Monitoring Plan
Control: Develop and document a map of system data actions.
Discussion: Data actions are system operations that process personally identifiable information. The processing of such information encompasses the full information life cycle, which includes collection, generation, transformation, use, disclosure, retention, and disposal.
MA-02: Controlled Maintenance
MA-06: Timely Maintenance
PL-02: System Security Plan
PM-22: Personally Identifiable Information Quality Management
PM-23: Data Governance Body
A Data Governance Body can help ensure that the organization has coherent policies and the ability to balance the utility of data with security and privacy requirements.
SA-03: System Development Life Cycle
SA-04: Acquisition Process
SA-08: Security Engineering Principles
SA-22: Unsupported System Components
SI-12: Information Management and Retention
Information management and retention requirements cover the full life cycle of information, in some cases extending beyond system disposal. Information to be retained may also include policies, procedures, plans, reports, data output from control implementation, and other types of administrative information.
SI-18: Personally Identifiable Information Quality Operations
SR-05: Acquisition Strategies, Tools and Methods
SR-12: Component Disposal
Conclusion: Crushed it! 🥊
Nice job everybody! Learn more about GRC risk management visiting the risk management room at TryHackMe. Let's go ahead and hit complete alright - absolutely crushed it! Hope you enjoyed day nine of Advent of Cyber. I'm Gerry from Simply Cyber, I’ll see you tomorrow.