Table of Contents
12.1 📚️ Introduction & Exam Objectives


🔍 Phase 1: Discovering Top Cyber Risks

Duration: 30-day process with 8 structured steps
Purpose: Help executives navigate infinite cyber risks with limited resources
Key Metaphor: "Sweeping for landmines" (military VP's terminology)
12.2-12.4 🧭 Be a Compass for Risk Decisions

Executives face:
Infinite cyber risks
Limited resources
Need for strategic direction
Your role: Provide the compass for navigating turbulent waters
Risk Treatment Options
Transfer - Insurance, outsourcing
Avoid - Don't engage in risky activities
Accept - Acknowledge and monitor
Mitigate - Implement controls
👣 8 Steps
Widen Your Scope - Beyond technology
Get Buy-In - Win hearts and minds
Select Interviewees - Choose right stakeholders
Generate Questionnaire - Create assessment tools
Determine Target Scores - Set benchmarks
Conduct Interviews - Gather data
Compile & Average Scores - Analyze results
Communicate Top 5 Risks - Present findings
👀 Step 1: Widen Your Scope
Holistic risk management approach
Cybersecurity encompasses more than just technology, to reliably achieve an organization’s mission

Cyber risk management needs a comprehensive assessment of:
People | Process | Management | Technology |
|---|---|---|---|
- Employee cyber risk awareness - Adherence to cybersecurity practices | - Effectiveness of established procedures and protocols | - Leadership commitment - Oversight | - Robustness of the technological systems and infrastructure |

Breaking Down Silos - Key Insights from Dr. Gerald Auger
Understanding Different Perspectives
Engineering/IT Side:
Success metrics: uptime, upgrades, minimal maintenance windows
Work style: product-focused, weekend work, automation
Demonstrating value through deliverables
Business Side:
Primary focus: revenue and mission achievement
View of IT/Security: cost centers
Decision drivers: financial impact
Bridging the Gap Through Empathy
For Technical Teams:
Explain business objectives in engineering terms
Show how their work supports revenue
Connect technical wins to business outcomes
For Business Teams:
Make security personal (e.g., MFA protects personal accounts too)
Demonstrate value: "Do you like 24/7 email access?"
Link security to business continuity

“End users are going to end use!” - Dr. Gerald Auger
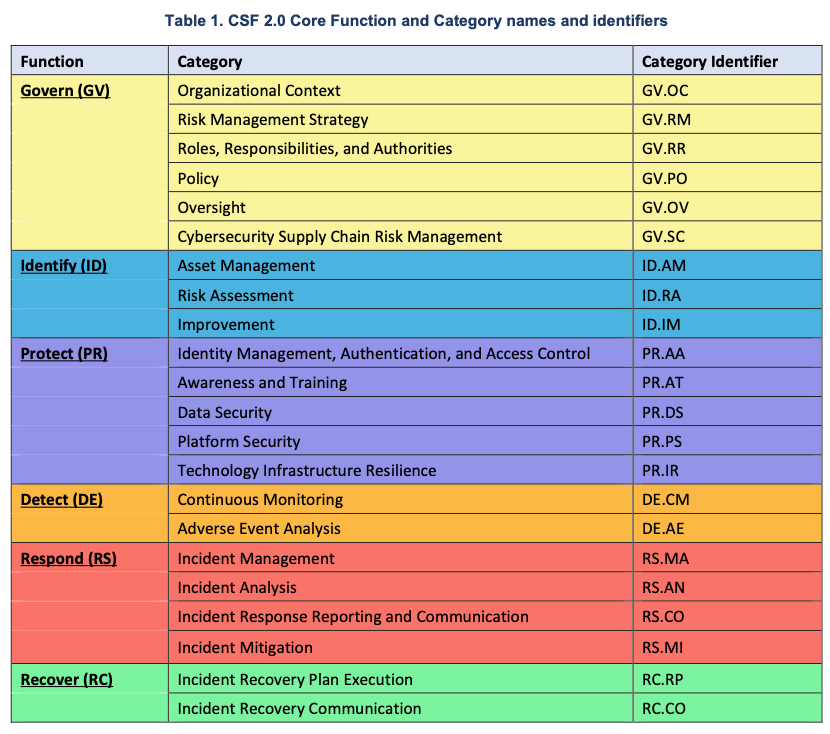
CSF Integration
Recommendation: Incorporate all 22 CSF subcategories
Benefits:
Demonstrates comprehensiveness
Identifies blind spots
Provides world-class framework coverage
Common Discovery: Many organizations find unexpected gaps when first exposed to CSF
Benefits of Widening Scope
Prudent - Risk-aware approach
Transparent - Open about assessment breadth
Communicative - Facilitates dialogue
Comprehensive - Shows commitment to protection
Foundation-setting - Establishes robust CRMAP base
Key Warnings
Bad news doesn't age well - Address issues early
Audit landmines - Late discoveries increase scope, time, cost, and stress
Reactive mode - Avoid firefighting through upfront comprehensiveness
Professional integrity - High standards serve long-term success
12.5 💙 🧠 Step 2: Get Buy-In: “Winning Hearts and Minds”
Change is Hard. Here Are 4 Steps to Gain Buy-In:

Tactics to Make Cultural Change Happen
Audits vs Assessments
Term | Audience | Perception |
|---|---|---|
Audit | External customers or regulators | - Finding faults and deficiencies - Puts stakeholders on the defensive |
Assessment | Internal | - Identifying areas for improvement |
C-suite Sample Kick-off Email

Mastering Cyber Resilience - AKYLADE
Key Elements:
Opening: Personal concern about cybersecurity
Business Context:
Threat landscape reality
Business impact examples (trade secrets, money, customer lists)
Disruption potential
Program Introduction:
Implementing Cyber Risk Management Action Plan
First step: stakeholder interviews
Balance security needs with business operations
Logistics:
30-90 minute interviews
In-person or video options
Point of contact for scheduling
Call to Action:
Questions about program → CEO/Leader
Questions about logistics → Coordinator
External Consultant Considerations
Challenge: Unknown entity without trust reservoir
Solution: Leadership endorsement email
Benefits:
Fast credibility establishment
Authority backing
Clear organizational support
Post-Email Best Practices
Expect immediate questions - Be ready
Address anxieties - Interview concerns common
Response qualities:
Prompt
Warm
Reinforcing collaboration
Building confidence
12.6 👥 Step 3: Select Interviewees

Ratios
Commercial Industry (Revenue-Based)
Revenue | # of Interviewees | Type of Interviews |
|---|---|---|
<$10 Million | 6 | In-person |
$100 Million | 15-20 | In-person |
$1 Billion+ | 20+ | Questionnaire forms |
Non-profits (Staff-Based)
# of Staff | Interviewee to # of Staff Ratio |
|---|---|
<50 | 1:5 |
51-1000 | 1:10 |
Target Interviewee Profile
The "Goldilocks Zone"
Position: Middle managers & senior-level individual contributors
Why this level?
Not too junior (see big picture)
Not too senior (connected to operations)
Direct operational knowledge
Risk exposure visibility
Key Departments to Include
Finance - Financial risks and controls
Human Resources - People-related risks
Operations - Process and production risks
IT - Technical infrastructure risks
Legal/Compliance - Regulatory risks (if applicable)
Sales/Marketing - Customer data risks

The “Cyber Risk Experts” across key departments such as Finance, HR, Operations and IT
Strategic Value of Interviewees
Internal "Cyber Risk Experts"
Characteristics:
Won't pass Security+ exam
Don't work in cybersecurity daily
BUT understand business risk impacts
Firsthand insight into the cyber risk landscape
Their Expertise:
Business objective threats
Operational vulnerabilities
Process weaknesses
Department-specific risks
Geographic considerations

Multi-Location Organizations
Ensure representation from:
Different regions
Various time zones
Remote locations
Branch offices
Benefits:
Comprehensive risk landscape
Regional compliance differences
Cultural considerations
Infrastructure variations
Cultural Transformation Opportunity
Interviewees as Change Agents
Internal Influencers:
Trusted by peers
Department ambassadors
Opinion leaders
Post-Interview Impact:
Become cyber risk managers
Advocate for security
Shift organizational culture
Champion reasonable cybersecurity
KEY TAKEAWAYS
Comprehensive Approach Required
Technology alone isn't enough
Four cylinders must work together
All 22 CSF categories recommended
Buy-In is Critical
Change management skills essential
Four-step process for success
Culture beats strategy
Strategic Interviewee Selection
Middle management sweet spot
Cross-functional representation
Geographic considerations
Cultural change agents
Professional Excellence
Transparency builds trust
Bad news doesn't improve with age
Integrity serves long-term success
Empathy bridges gaps
Next Steps
Module B: Generate the Questionnaire (Step 4)
Module C: Determine Target Scores (Step 5)
Module D: Interview Execution & Analysis (Steps 6-8)