How to “So What, What’s Next?” Your NIST CSF Assessment
Table of Contents
📚 Exam Objectives

🧭 The CR-MAP Process
Introduction: Why CR-MAP Matters
Core Purpose of A/CCRP Certification
The AKYLADE Certified Cyber Resilience Practitioner (A/CCRP) certification builds upon A/CCRF foundations to test practical knowledge of implementing the NIST Cybersecurity Framework through real-world scenarios.
The Fundamental Equation
NIST Cybersecurity Framework = What to do
Cyber Risk Management Action Plan (CR-MAP) = How to do it
Target Audience
Entry to mid-level cybersecurity professionals with 1-3 years experience in:
Cybersecurity operations/administration
Governance, Risk & Compliance (GRC)
The Five Essential Questions CR-MAP Answers
A successful CR-MAP implementation enables you to confidently answer:
🔝 What are the top five cyber risks to my organization?
💰 Am I getting the biggest return possible for my cyber risk management dollars?
👔 Do all our organization's executives and leaders understand our cybersecurity plans?
⚠ Does everyone at work know how they can help to mitigate our top cyber risks?
🗣 What do I tell our biggest customers or stakeholders when they ask, "What are you all doing about cybersecurity?"
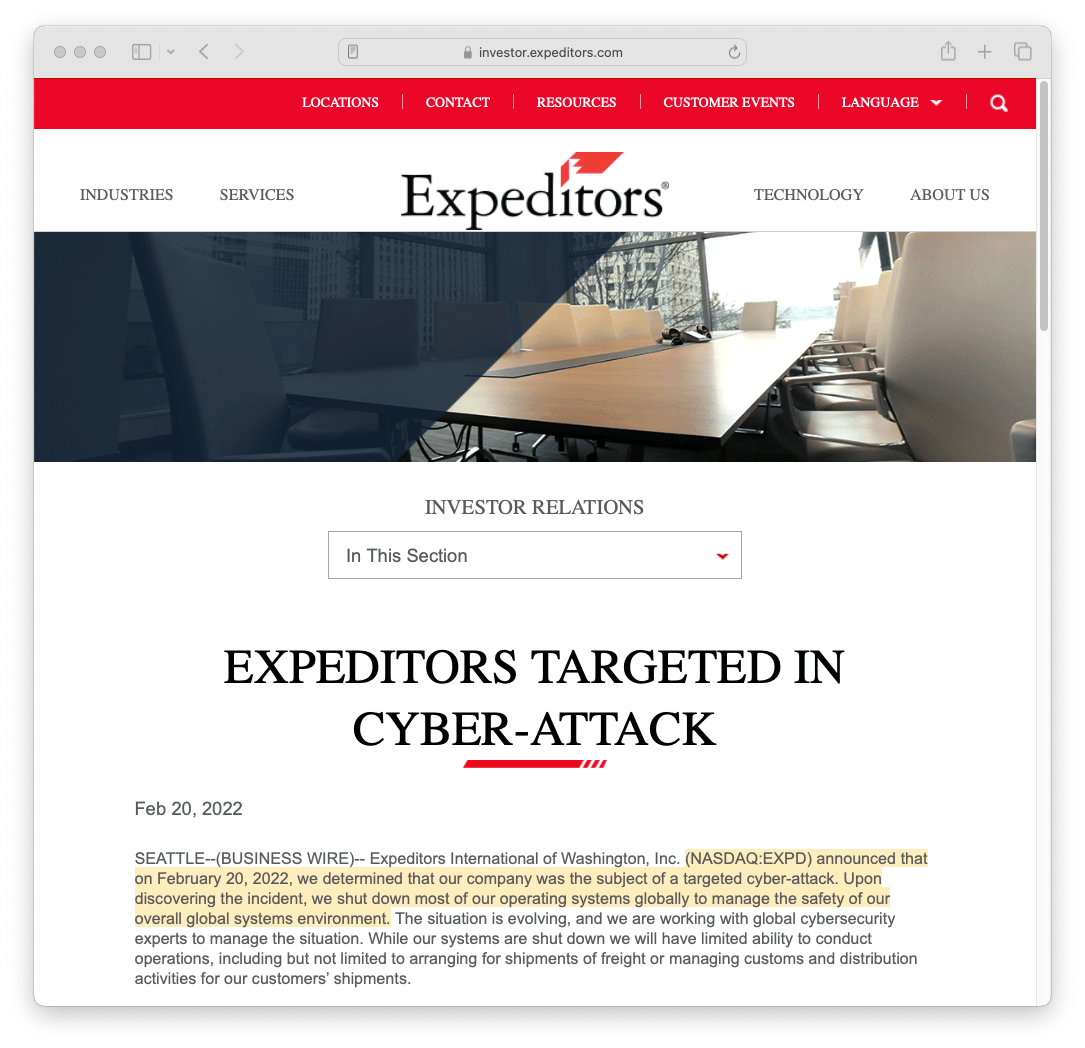
Real World Case Study: Expeditors
Background
Expeditors - Fortune 500 logistics company operating as a global freight management provider with approximately 18,000 employees.
The Incident (February 20, 2022)
Complete global network outage lasting three weeks, with several additional weeks required for full restoration.
The Cost of the Attack

Direct Costs to Expeditors
$47 million - Lost due to disrupted operations and fines from accumulated shipping containers
$18 million - Investigation, recovery, and shipping-related claims
Total: $65 million (unbudgeted, no cyber insurance coverage)
iRobot Corp Sued Expeditors

Cascading Impact: The iRobot Lawsuit (April 2023)
Lawsuit Amount: $2.1 million plus interest and legal fees
iRobot's Allegations:
Expeditors exposed systems through inattentiveness and negligence
Lacked proper business continuity plans
Breached contractual obligations for 24-hour shipping and 4-hour system updates
Fallout

iRobot's Direct Costs:
$900,000 in retailer refunds
$23,000 in expedited shipping
$1.1 million in new logistics provider transition costs
$1 million in additional storage and back charges
Physical counting and transportation of 12,000 pallets on 207 rented trailers
Foreseeable?
Critical Question: Was this foreseeable?
iRobot argued Expeditors' own 10-K filing identified cyberattack as a foreseeable risk
Failure to implement risk mitigation despite known risks
Demonstrates the business reality: Cyber resilience is fundamentally a business problem requiring both technical AND business acumen
The Cascading Effect: Expeditors → iRobot → Retailers → End Consumers
This illustrates how cyber incidents create ripple effects throughout entire supply chains, affecting multiple stakeholders and business relationships.
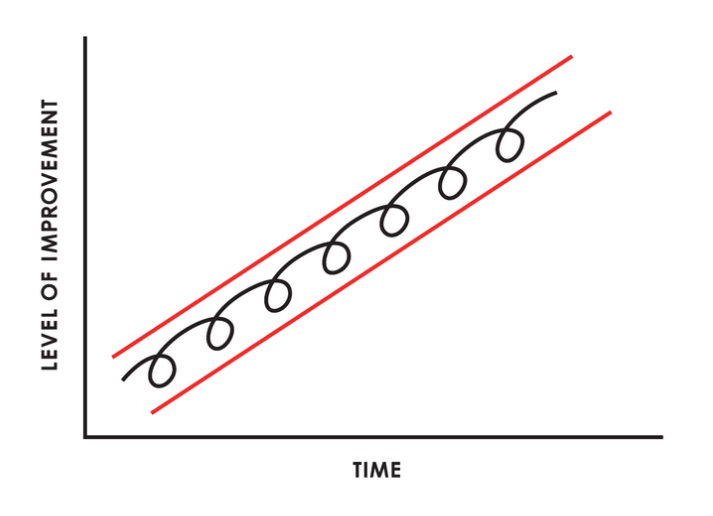
🔄 Reasonable and Repeatable Cybersecurity Practices
Federal Trade Commission (FTC) Mandate
Organizations implement reasonable security measures, based on their size, sophistication, and data collection practices.
Due diligence is establishing a plan, policy, and processes to protect the interests of the organization.
Due care is practising the individual activities that maintain the due diligence effort.
In today’s business environment, prudence is mandatory. Showing due diligence and due care is the only way to disprove negligence and occurrence of loss. Senior management must show due care and due diligence to reduce their culpability and liability when a loss occurs.
Take a Systematic Approach: “Rinse and Repeat”
The NIST CSF emphasizes the need for repeatable cybersecurity practices through its iterative framework. This is not a one-time exercise but an ongoing cycle of improvement.
It’s similar to ISO27001 in this regard:


Failure to comply with the FTC mandate, may result in:
Charges of unfair or deceptive acts, leading to severe consequences such as corrective orders
Extensive oversight of cybersecurity programs for up to two decades
Fines of up to $40,000 per violation.
Thrive Amidst Evolving Cyber Risks

Effective leadership lies in facilitating meaningful change
Relationship Between NIST CSF and CR-MAP
Complementary Frameworks
NIST Cybersecurity Framework:
Provides the "what" - outcomes to achieve
Framework Functions: Identify, Protect, Detect, Respond, Recover, Govern
Flexible, risk-based approach
Version 2.0 current standard
CR-MAP Process:
Provides the "how" - practical implementation method
Translates CSF outcomes into actionable steps
Quantifies progress using 0-10 scale
Contextualizes for specific organizations
The CR-MAP 0-10 Scale
Purpose: Quantifies organizational maturity against NIST CSF outcomes
How It Works:
Each CR-MAP question maps to specific CSF outcomes
Organizations rate themselves 0-10 on each question
Lower scores indicate less maturity
Higher scores indicate greater implementation
Target Score Setting:
Organizations establish target scores aligned with:
Risk tolerance
Industry benchmarks
Compliance requirements
Resource availability
Target scores drive goal setting and roadmap prioritization
Progress measured by improvement from current to target state
Importance of Target Scores:
Provides clear, measurable objectives
Enables progress tracking over time
Supports resource allocation decisions
Facilitates communication with stakeholders
Creates accountability for improvement
Risk Profile Alignment
NIST CSF Risk Profiles: Organizations must match their characteristics to appropriate CSF risk profile details:
Organizational Factors:
Industry sector and regulations
Size and complexity
Risk tolerance
Threat landscape
Available resources
Profile Components:
Current state assessment
Target state definition
Gap analysis
Prioritization approach
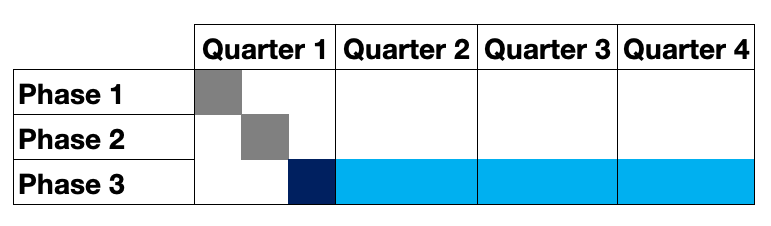
📝 Three Phases of the Cyber Risk Management Action Plan
Overview of the 12-Month Cycle
The CR-MAP process follows a structured three-phase approach designed to be completed within one year:
Phase One: 30 days - Discover Top Cyber Risks
Phase Two: 30 days - Create Action Plan
Phase Three: 10 months - Maintenance and Updates
The 13th Month: Repeat the cycle
Outcomes:
Establish a robust cyber resilience program within your organization
Reduce cyber risk footprint
Significantly enhance cyber resilience
Positively impacting your bottom line
Saving substantial time
Phases:
Discover your top cyber risks
Make your cyber risk management action plan
Perform maintenance and updates
🔍 Phase One: Discover Your Top Cyber Risks
Goal: Develop a rigorous prioritization method to determine your company's most critical risks

Core challenge:
As an executive, you encounter infinite cyber risks that can impact your organization, but it is crucial to prioritize them effectively, given your limited resources.
Key Activities:
Identify appropriate stakeholders
Create interview lists based on:
Role and technical ability
Geographic location and branch representation
Conduct interviews to gather risk data
Analyze network diagrams
Review both qualitative and quantitative data
Generate custom questionnaires tailored to the organization
Create visual representations of risk data
Deliverables:
Top 5 Cyber Risks Report showing:
Organization-wide aggregate risks
Risks by business unit
Themed contextualization
High-level remediation advice
Visual charts (radar/spider charts, bar graphs, pie charts)
Custom questionnaire for the target organization
Preparing for Assessment: Best Practices
Understanding the Target Organization
Pre-Assessment Research:
Industry sector and competitive landscape
Regulatory environment
Business model and operations
Technology infrastructure
Previous security incidents or audits
Organizational culture and structure
Key Questions to Answer:
What business are they in?
What are their critical assets?
Who are their key stakeholders?
What regulations apply to them?
What is their risk appetite?
Target Score Setting:
Establish alignment with NIST CSF using the CR-MAP 0-10 scale

📝 Phase Two: Create Your Cyber Risk Management Action Plan

Duration: 30 days
Goals:
Ensure that every dollar invested in cyber risk management provides maximum value in mitigating the prioritized risks.
Manage your risks effectively and improve your competitive advantage, by adopting reasonable cybersecurity practices.

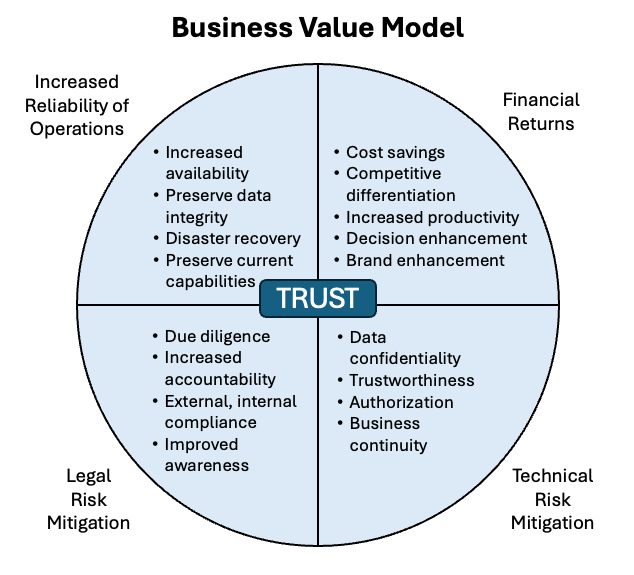
Core elements include:
4 key dimensions of business value
Every mitigation must be evaluated against these dimensions:
Financial Returns - Direct cost savings or revenue protection
Technical Risk Mitigation - Reduction of technical vulnerabilities
Legal Risk Mitigation - Compliance and liability reduction
Reliability of Operations - Improved uptime and operational continuity
Key Components
1. Personalized Cyber Risk Management Strategy
Create tailored strategies specific to your organization's:
Industry sector
Size and complexity
Risk tolerance
Resource availability
Compliance requirements

Contextualizing Plans for the Target Organization
Customization Factors:
Size Considerations:
Small organizations: Simpler processes, fewer resources
Medium organizations: Growing complexity, scaling challenges
Large organizations: Complex environments, more stakeholders
Industry-Specific Factors:
Healthcare: HIPAA compliance, patient data protection
Financial: PCI-DSS, SOX, financial regulations
Retail: PCI-DSS, customer data, e-commerce
Manufacturing: OT/IT convergence, supply chain risks
Maturity Level:
Starting fresh: More foundational work needed
Some practices in place: Build on existing foundation
Mature programs: Focus on optimization and gaps
Cultural Considerations:
Risk-averse vs. risk-tolerant
Hierarchical vs. flat structure
Technical sophistication level
Change readiness
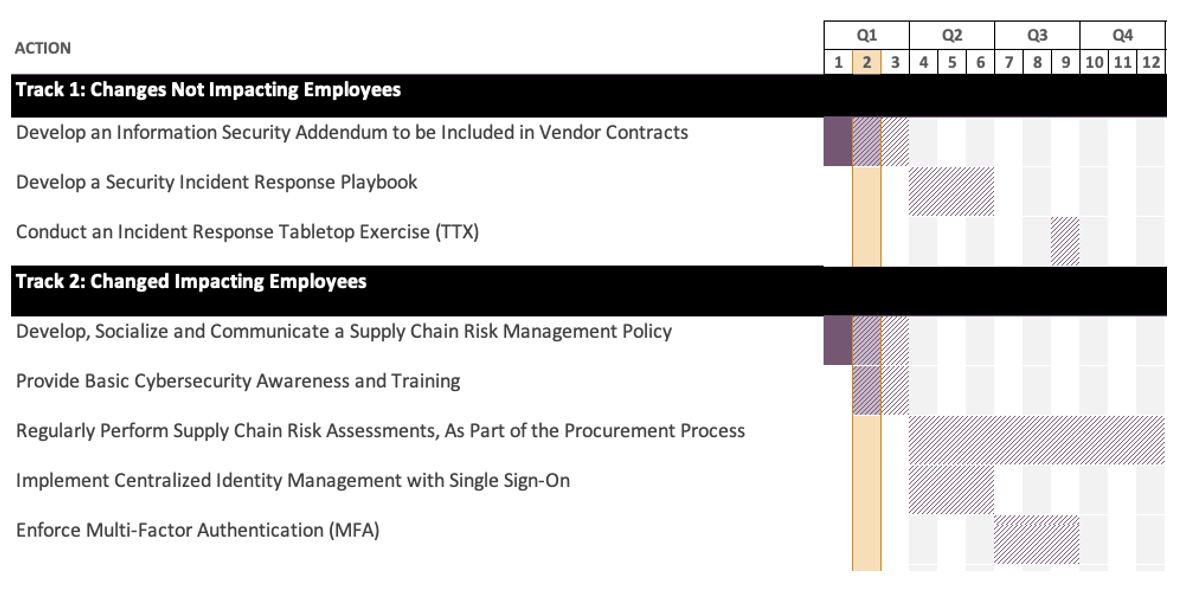
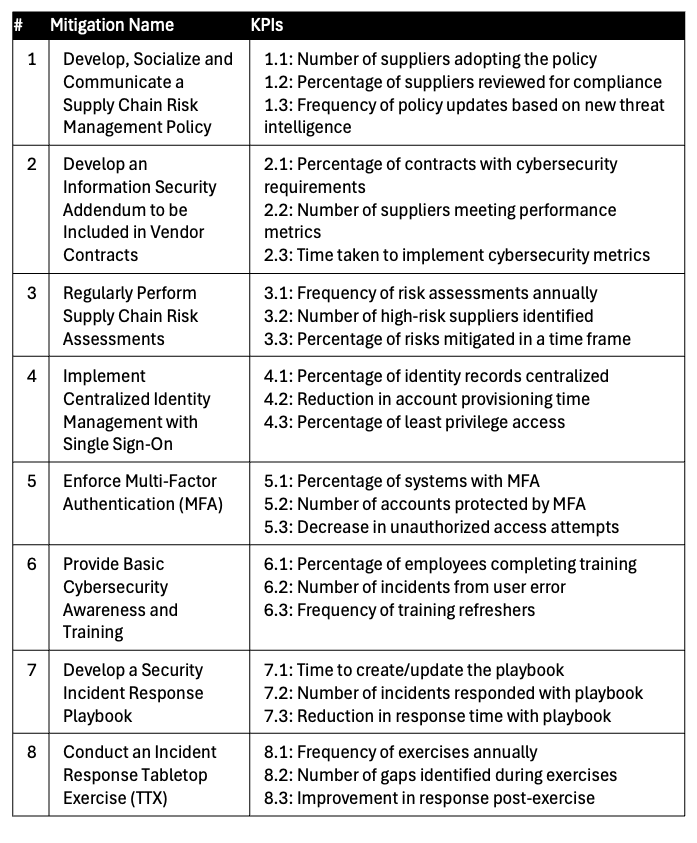
2. Prioritized Implementation Roadmap
Addresses the Top 5 Cyber Risks identified in Phase One with:
Specific mitigations mapped to each risk
Custom mitigations based on questionnaire and interview data
Standard Operating Procedures (SOPs) for each control
Cost estimates for implementation
Resource allocation considerations
Creating a Project Roadmap
Essential Roadmap Components:
1. Timeline and Milestones
Phase One: 30 days for discovery
Phase Two: 30 days for action plan
Phase Three: 10 months for maintenance
Key decision points and reviews
2. Resource Requirements
Personnel (internal and external)
Tools and technology
Budget allocation
Time commitments from stakeholders
3. Stakeholder Engagement Plan
Identification of key stakeholders
Interview schedules
Communication cadence
Approval processes
4. Document Requirements
Templates to prepare
Data collection tools
Reporting formats
Presentation materials
3. Resource Limitation Management
Understand and plan for constraints in:
Time - Implementation schedules and availability
Money - Budget allocations and cost justifications
Skilled Personnel - Availability of internal expertise
Key Activities:
Verify each top risk is covered by mitigation roadmap
Rate each mitigation using the Business Value Model
Create custom mitigations based on organizational context
Develop SOPs for mitigations and controls
Generate cost estimates
Create implementation roadmap with Gantt charts
Assign mitigations to specific organizational units
Group mitigations by owner type
Change Management Tools
Force Field Analysis
Identify and analyze:
Driving forces - Factors supporting change
Restraining forces - Factors resisting change
Strategies to strengthen drivers and weaken restraints

Stakeholder Analysis
Map stakeholders by:
Level of interest in cybersecurity initiatives
Level of influence over outcomes
Appropriate engagement strategies for each group

Coordinating with Management for Buy-In
Providing Adequate Answers to Management Questions
Common Executive Concerns:
"How much will this cost?"
Provide cost estimates broken down by phase
Show ROI through risk reduction
Compare to cost of potential incidents
Demonstrate business value dimensions
"How long will this take?"
Clear timeline with milestones
Resource requirements at each phase
Dependencies and critical path
Quick wins vs. long-term efforts
"Why should we do this now?"
Current threat landscape
Regulatory requirements
Competitive pressures
Cost of inaction (use Expeditors case study)
"How do we measure success?"
Clear KPIs and metrics
Progress against target scores
Risk reduction quantification
Business impact measures
Translating Technical Topics to Layman's Terms
Communication Strategies:
Use Analogies:
"Firewall is like a security guard checking IDs"
"Encryption is like a secret code only you can read"
"Backups are like insurance for your data"
Focus on Business Outcomes:
Instead of: "We need to patch vulnerabilities"
Say: "We need to fix security gaps that could let attackers in"
Quantify in Business Terms:
Instead of: "We have a critical zero-day"
Say: "We have a high-priority security issue that could cost us $X if exploited"
Tell Stories:
Use case studies (like Expeditors)
Industry examples
"What if" scenarios specific to the organization
Visual Communication:
Charts showing risk levels
Roadmap timelines
Before/after comparisons
Heat maps of risk areas
Change Management
Key elements:
Communication plans to achieve buy-in
Addressing management questions adequately
Translating complex technical topics into layman's terms
Demonstrating business impact of cyber incidents

Key Performance Indicators (KPIs)
Establish measurable metrics to:
Track implementation progress
Demonstrate value delivery
Justify continued investment
Support continuous improvement
⚙ Phase Three: Maintenance and updates
Duration:
10 months
When combined with phase one and phase two of the CR-MAP process, it completes the first-year cycle of the three-phase plan
Goals:
Maintain and continuously improve with monthly check-ins and comprehensive quarterly reviews to monitor progress
Bolster cyber resilience with a comprehensive approach, and by committing to ongoing vigilance
Opportunity to investigate and correct gaps or challenges to regain momentum
Acknowledge and celebrate achievements in managing cyber risks
Review Cadence:
Monthly check-ins - Quick progress reviews
Quarterly comprehensive reviews - Detailed assessment and adjustment
“Just like everything else in GRC, rinse and repeat! I hate to make it sound so uncool-or whetever- but this is the deal.
This is how you become a baller GRC Analyst: by understanding what these [CSF subcategories] are asking and being able to convey an example.”
Key Activities:
Assist leadership in assigning mitigations to internal and external parties
Generate updated presentations as mitigations are implemented:
Review completed mitigations
Determine numeric scores for each
Update charts and risk assessments with new data
Explain proposed mitigations and their accomplishments:
Technical controls
Administrative controls
Physical controls
Preventative controls
Detective controls
Corrective controls
Conduct ongoing reviews of cyber resiliency:
Create post-assessment communication plans
Update roadmap based on periodic reviews
Adjust for changing threat landscape
Adapt to business changes
🗓 The Thirteenth Month: Annual Cycle Repetition

Why continuous monitoring is critical:
Dynamic Threat Landscape:
Adversaries continually innovate
New attack vectors emerge constantly
Previous defenses become obsolete
Business Evolution:
Organizations undergo significant changes
New systems and processes are introduced
Business priorities shift
Cultural Reinforcement:
Interview process reminds employees of cyber hygiene importance
Keeps reasonable cybersecurity practices top-of-mind
Maintains organizational awareness and engagement
Continuous Improvement Mandate: The NIST CSF explicitly calls for repetition and continuous improvement. The 13th month represents the restart of the cycle, ensuring:
Ongoing adaptation to evolving threats
Alignment with changing business dynamics
Sustained competitive advantage
Continual enhancement of cyber risk management capabilities
The Five Questions
Once you have created your cyber risk management action plan, you should be able to confidently answer the five questions we asked at the beginning:
🔝 What are the top five cyber risks to my organization?
💰Am I getting the biggest return possible for my cyber risk management dollars?
👔 Do all our organization’s executives and leaders understand our cybersecurity plans?
⚠ Does everyone at work know how they can help to mitigate our top cyber risks?
🗣 What do I tell our biggest customers or stakeholders when they ask, “What are you all doing about cybersecurity?”
Bottom-Line Perspective on CR-MAP Value
1. Cultural Transformation Shifts organizational culture toward achieving reasonable cyber resilience
"Culture eats strategy for breakfast" - Peter Drucker
Embeds cybersecurity into organizational DNA
2. Legal Protection Demonstrates due diligence and due care
Provides evidence of reasonable security practices
Protects against negligence claims
Supports defense in legal proceedings
3. Repeatable Process Introduces "Lather, Rinse, Repeat" approach
Systematic and documentable
Meets regulatory requirements
Provides consistency across cycles
4. Resource Optimization Prioritizes infinite cyber risks with limited resources
Maximizes four types of business value
Ensures efficient allocation of budget
Focuses effort where it matters most
5. Actionable Roadmap Answers "so what, what's next?" for top cyber risks
Right-sized for organizational capacity
Achievable and measurable
Clear implementation plan
6. Effective Communication Enables risk management communication throughout organization
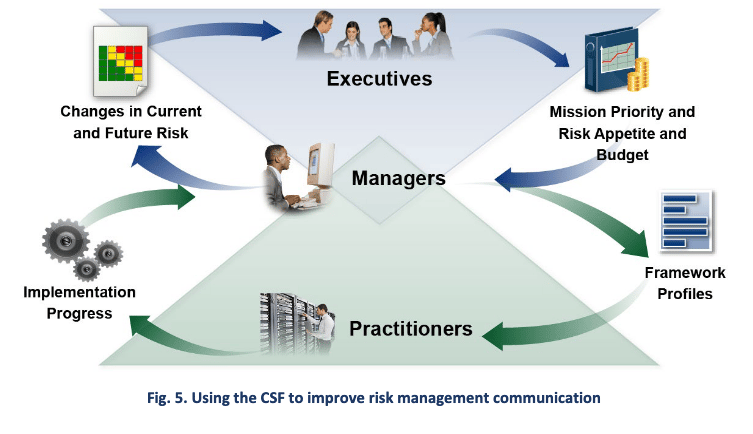
Executives understand cybersecurity plans
Technical teams know their role
All employees understand how they contribute
Stakeholders receive confident answers
7. Competitive Advantage Enhances operational reliability and market position
Demonstrates security maturity to customers
Supports business development
Protects reputation and brand value
👥 Fostering Security Culture
The People Problem in Cybersecurity
Key Insight: You can’t buy security culture off the shelf and plug it in! You need these cultural elements:
1. Security Awareness
Regular training programs
Phishing simulations
Security reminders and communications
2. Shared Responsibility
Every employee understands their role
Security is not just IT's problem
Active participation expected at all levels
3. Positive Reinforcement
Celebrate security wins
Recognize good security behavior
Make compliance easier than non-compliance
4. Leadership Commitment
Executive buy-in and visibility
Resources allocated appropriately
Security integrated into business decisions
5. Continuous Learning
Stay current with evolving threats
Share lessons learned from incidents
Adapt practices based on feedback
Measurement Considerations: CISOs should develop metrics to measure security culture effectiveness:
Employee participation in training
Reporting rates for suspicious activity
Reduction in successful phishing attempts
Speed of incident reporting
🔒 Attorney-Client Privilege Considerations
Purpose and Benefits
Primary Advantage: Retain control over cyber risk records and navigate potential disclosure requests
How It Works:
Communications between client and attorney are protected
Covered under Federal Rules of Evidence and common law
May extend to work product of cyber resilience practitioners working under attorney direction
Strategic Value: If an identified cyber risk manifests as a breach:
Without privilege: Risk prioritization decisions may be used against you
With privilege: Records may be protected from discovery
Attorney can help navigate disclosure requests
Implementation Approach
1. Engage Legal Counsel
In-house counsel (if available)
Outside attorney with cybersecurity expertise
2. Establish Formal Relationship
Document attorney-client relationship
Ensure proper contractual arrangements
Define scope of privileged work
3. Work Product Protection
Cyber resilience practitioner follows attorney's instructions
Proper handling and protection of cyber risk information
Documentation created under attorney supervision

Disadvantages to Consider
Increased Costs:
Legal fees for attorney involvement
Additional administrative overhead
More complex documentation requirements
Extended Timeline:
Legal review processes
More formal approval procedures
Additional coordination requirements
Cost-Benefit Analysis: "Based upon over two decades of commercial and business litigation experience, one of our authors can confirm that it is almost always less expensive to retain proper legal advice from a licensed attorney up front to mitigate your liability exposure than to hire a lawyer to defend your organization against litigation later on."
Important Limitations
Not Universal:
Concept may vary by country
Some limited exceptions exist
May not apply in all circumstances
Consult licensed attorney for specifics
Not Legal Advice: This course and these notes do not constitute legal advice. Always consult with qualified legal counsel in your jurisdiction.
✅ Conclusion and Touchpoints
CR-MAP: 3 Phases
First phase: focuses on discovering and assessing the top cyber risks faced by the organization
This phase involves prioritizing risks to allocate limited resources effectively
Second phase: involves creating a personalized cyber risk management action plan that addresses the top five risks identified in phase one
This plan considers various dimensions of business value and aims to mitigate risks while enhancing operational reliability and competitive advantage
Third phase: emphasizes the importance of maintaining, updating, and continuously improving the organization’s cybersecurity posture and risk management strategy
The 13th month 🗓 concept was introduced to emphasize the need for an ongoing and iterative approach to cyber risk management
Repeat the CR-MAP process annually
This repetition ensures continual improvement and adaptation to evolving cyber threats and the alignment of cyber risk management efforts with changing business dynamics.
Systematic approach
In summary, the CR-MAP process provides organizations with a structured and comprehensive framework to strengthen their cyber resilience.
By systematically identifying and managing cyber risks, organizations can proactively mitigate potential incidents, safeguard valuable assets, and sustain a competitive advantage in the modern digital landscape.
However, it is vital to emphasize the significance of perpetual vigilance, continuous improvement, and the ingrained integration of cybersecurity practices into the organization’s culture to effectively achieve these objectives.