Table of Contents
Exam Objectives 📚
Candidates must be able to understand the Framework Core as it relates to the NIST Cybersecurity Framework. Students will be able to:
2.1 Explain the importance of the Framework Core
Purpose
Usage
Benefits
Effectiveness
Framework Components 🧩
Framework Core
Set of common cybersecurity activities, desired outcomes, and applicable references that help organizations manage and mitigate cyber risks
Presents industry standards, guidelines, and best practices in a way that allows communication with various stakeholders across the organization, regardless of whether they operate at the executive, operational, implementation, or tactical levels
This common lexicon can greatly enhance communication up and down the organizational hierarchy and ensure everyone is well understood
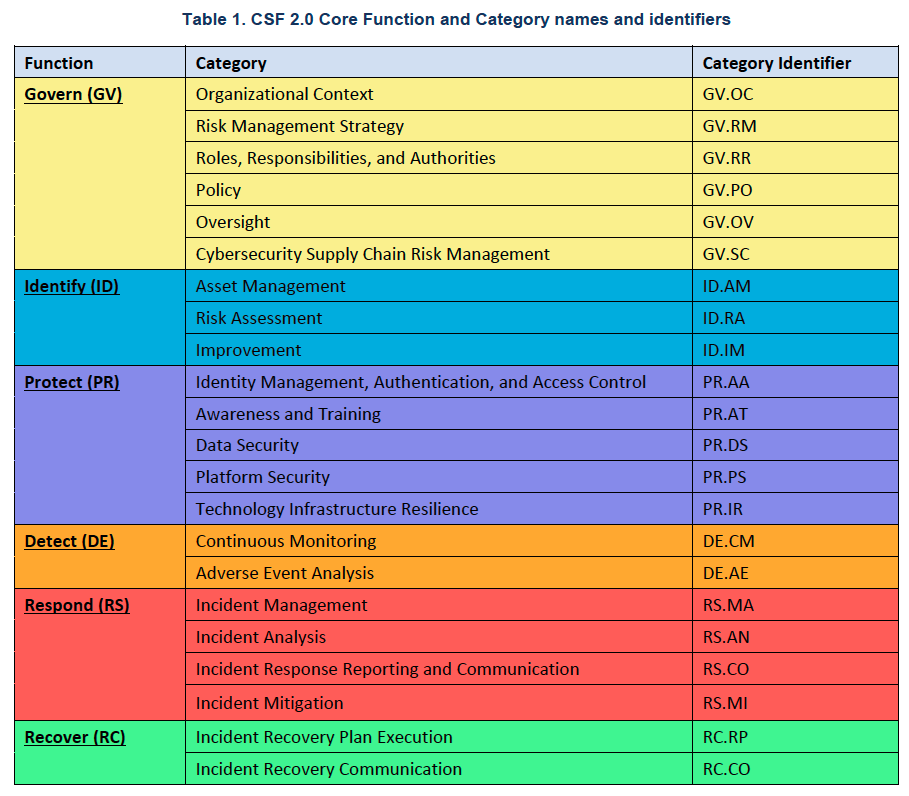
Six Functions
Concurrent and continuous functions that all organizations perform when conducting cybersecurity activities
Performed concurrently and continuously to form an operational culture that addresses the dynamic nature of cybersecurity risk
Not intended to form a serial or linear path that will ultimately achieve a static desired end state
Constantly evolve and adapt, just like the adversary
Group related activities and outcomes together in order to achieve specific cybersecurity objectives
Profile
Tiers
Help understand how well an organization is aware of its risks and threats, how repeatable the outcomes they produce are, and how well the organization adapts to new risks and threats.
The level of effectiveness in implementing cybersecurity practices within an organization
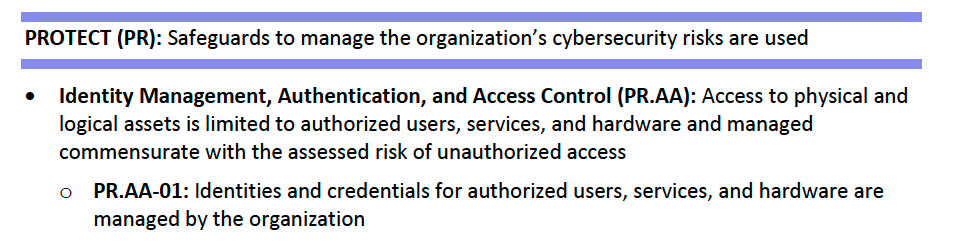
Categories
For each function, there are also underlying key categories and subcategories with specific outcomes.
Subcategories
For each subcategory, these activities are then matched with example informative references from existing standards, guidelines, and best practices used throughout the industry.
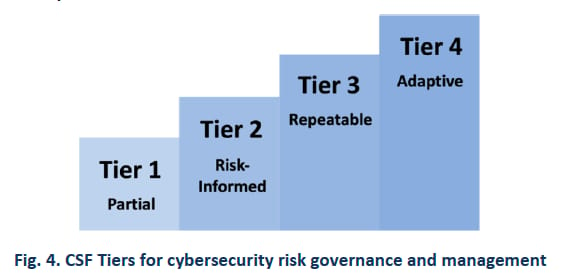
Implementation Tiers 🪜
Tier 1 Organizations: Partial

Overall ineffective risk management methods
Initial stage of cybersecurity implementation
Limited awareness and capabilities
Cybersecurity practices are ad hoc and reactive in nature
Usually have unsystematic risk management processes, unreliable risk management programs, and unresponsive risk management participation
Everybody starts somewhere
Hopefully not the desired/target state!
Tier 2 Organizations: Risk Informed

Informal risk management methods with unfinished risk management processes, underdeveloped risk management programs, and incomplete risk management participation.
They aren’t as bad off as the Tier 1 organizations, but there is still a lot of room for improvement.
Generally has a higher level of cybersecurity implementation by having developed some formalized policies and procedures and with greater awareness and proactive cybersecurity practices in place.
Tier 3 Organizations: Repeatable

Structured risk management methods with orderly risk management processes, robust risk management programs, and routinely reviewed risk management participation.
While there is room for improvement, overall, they are doing a good job with risk management.
Many organizations will decide that reaching Tier 3 is good enough based on the cost and resources that may be required to achieve the next higher tier level.
Demonstrate a proactive approach to cybersecurity, focusing on continuous improvement and the ability to respond effectively to emerging threats and vulnerabilities.
Tier 4 Organizations: Adaptive

Proactive, innovative, and adaptive approach to cybersecurity and the organization’s risk management methods.
Demonstrate the characteristics of Tier 3 and have an advanced capability to adapt and respond to evolving cybersecurity risks.
Actively seek out emerging technologies, collaborate with industry partners, and participate in research and development efforts to stay ahead of cyber threats.
Continuously strive for excellence and maintain a strong cybersecurity posture that enables them to effectively protect their systems, assets, and sensitive information.
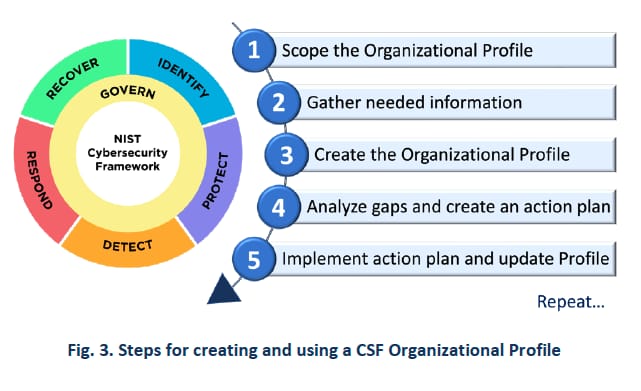
The Framework Profile 🛤️
The organization’s cybersecurity objectives, current state, and target state
Developing a profile
To develop a profile, review all the categories and subcategories in the framework and then select the relevant ones based on your business or mission drivers and a risk assessment
Which are most important to your organization for reducing or mitigating cyber risk?
Current profile - existing state
The current profile depicts an organization’s existing cybersecurity practices, including its activities, outcomes, and current risk management approaches.
Target profile - desired state
The target profile represents the organization’s desired state of cybersecurity practices and outcomes and outlines the specific cybersecurity improvements and goals it aims to achieve
Once the organization creates its current profile and target profile, it can be used to conduct a gap analysis between your current state and desired future state
The results of this gap analysis will then be used to create a plan of action

A law firm likely won’t need PR.PS-6, “Secure software development practices are integrated, and their performance is monitored throughout the software development life cycle.”
When developing your profiles, remember that there are 106 outcomes listed in the framework that you can choose from, but you do not need to use them all.
Conclusion and Touchpoints ✅
The framework consists of three key components:
Framework core
Implementation tiers
Profile
Framework core: the framework's foundation and encompasses six key functions: govern, identify, protect, detect, respond, and recover.
These functions are interconnected and form an operational culture that addresses the dynamic nature of cybersecurity risks.
Framework implementation tiers: used to categorize organizations based on their cybersecurity maturity level, ranging from Tier 1 (partial) to Tier 4 (adaptive).
Framework profile: used as a customizable tool that allows organizations to align the framework with their unique risk management objectives and prioritize their cybersecurity improvements.
By understanding and leveraging these framework components, organizations can enhance their cyber resilience and effectively protect their critical assets and operations in today’s highly connected digital world.
The NIST Cybersecurity Framework is not a compliance requirement or regulation. It’s voluntary
There is no right or wrong answer when developing these tiers within your organization
Where to focus? 🤔
Ensure that what you identify as your current state accurately reflects where you truly are
Then that your target state is where you truly plan to work across the entire organization