🧭 Chapter 11: The CR-MAP Process
📚 Exam Objectives
1.1 Explain how to best prepare for an assessment
Understand the target organization
Create a project roadmap
1.2 Understand the CR-MAP process
Prepare needed documents
Contextualize plans in relation to the target organization
1.3 Given a scenario, coordinate with management to achieve organizational buy-in
Provide adequate answers to management questions
Communicate potential business impacts of cyber security incidents
Communicate complex technical topics in laymens terms
Create communication plans to achieve buy-in
1.4 Explain the relationship between the NIST CSF and the CR-MAP process
Understand how CR-MAP questions relate to NIST CSF outcomes
Understand how CR-MAP 0-10 scale relates to the NIST CSF
1.5 Given a scenario, establish risk profiles for an organization
Match the target organization to details in the NIST CSF risk profiles
📰 Real World Case Study: Expeditors
Case Study: Expeditors' Cybersecurity Incident
Cyber resilience is fundamentally a business problem. Yes, there’s a large technical component, but to be a good cyber resilience practitioner, you need both technical acumen and business acumen.
Expeditors, a Fortune 500 logistics company with 18,000 employees, manages global freight movements.
On February 20, 2022, Expeditors announced a complete outage of their global computer network, lasting three weeks.
During this time, they gradually restored enough functionality to resume serving customers and bookkeeping tasks, though full functionality took several additional weeks.
Cost of the Attack
$47 million was lost due to disrupted business operations and fines from accumulated shipping containers.
$18 million was spent investigating and recovering from the incident and covering shipping-related claims.
Total unbudgeted cost: $65 million, which wasn’t covered by cyber insurance because they lacked coverage.
Legal Fallout: iRobot Lawsuit
In April 2023, iRobot Corp, a Roomba vacuum manufacturer, filed a $2.1 million lawsuit against Expeditors. Alleging contractual breaches, iRobot claimed Expeditors:
Exposed systems to cyber attacks due to inattentiveness and negligence.
Lacked proper business continuity plans, which led iRobot to physically count products at Expeditors' warehouses and arrange for direct delivery of 12,000 pallets on 207 rented trailers.
This caused iRobot:
$900,000 in refunds to retailers.
$23,000 in extra shipping costs to reach consumers.
Contractual Obligations and Additional Costs
Expeditors was supposed to store, maintain, and ship iRobot’s products within 24 hours of order and update their system within four hours of any movement. However, when these systems became unavailable, iRobot’s orders went unfulfilled. As a result, iRobot incurred:
$1.1 million in additional storage and back charges after switching to a new logistics provider.
The cascading impact of this incident went from Expeditors to iRobot to retailers.
Was This Foreseeable?
iRobot argued that Expeditors’ annual report had already identified cyber attack as a foreseeable risk. Claiming Expeditors failed to implement reasonable risk mitigation, iRobot sought $2.1 million plus interest and legal fees. While the final outcome is unknown, this case highlights the severe financial consequences of lacking cyber resilience.
🔄 Reasonable and Repeatable Cybersecurity Practices
Federal Trade Commission (FTC) Mandate
Organizations implement reasonable security measures, based on their size, sophistication, and data collection practices.
Due diligence is establishing a plan, policy, and processes to protect the interests of the organization.
Due care is practising the individual activities that maintain the due diligence effort.
In today’s business environment, prudence is mandatory. Showing due diligence and due care is the only way to disprove negligence and occurrence of loss. Senior management must show due care and due diligence to reduce their culpability and liability when a loss occurs.
Take a Systematic Approach: “Rinse and Repeat”

Failure to comply with the FTC mandate, may result in:
Charges of unfair or deceptive acts, leading to severe consequences such as corrective orders
Extensive oversight of cybersecurity programs for up to two decades
Fines of up to $40,000 per violation.
Thrive Amidst Evolving Cyber Risks
Effective leadership lies in facilitating meaningful change
📝 Three Phases of the Cyber Risk Management Action Plan
Outcomes:
Establish a robust cyber resilience program within your organization
Reduce cyber risk footprint
Significantly enhance cyber resilience
Positively impacting your bottom line
Saving substantial time
Phases:
Discover your top cyber risks
Make your cyber risk management action plan
Perform maintenance and updates
🔍 Phase One: Discover Your Top Cyber Risks
Duration: 30 days
Goal: Develop a rigorous prioritization method to determine your company's most critical risks

As an executive, you encounter infinite cyber risks that can impact your organization, but it is crucial to prioritize them effectively, given your limited resources.

📝 Phase Two: Create Your Cyber Risk Management Action Plan

Duration: 30 days
Goals:
Ensure that every dollar invested in cyber risk management provides maximum value in mitigating the prioritized risks.
Manage your risks effectively and improve your competitive advantage, by adopting reasonable cybersecurity practices.
Core elements include:
4 key dimensions of business value
Creation of a personalized cyber risk management strategy tailored to your organization’s specific need

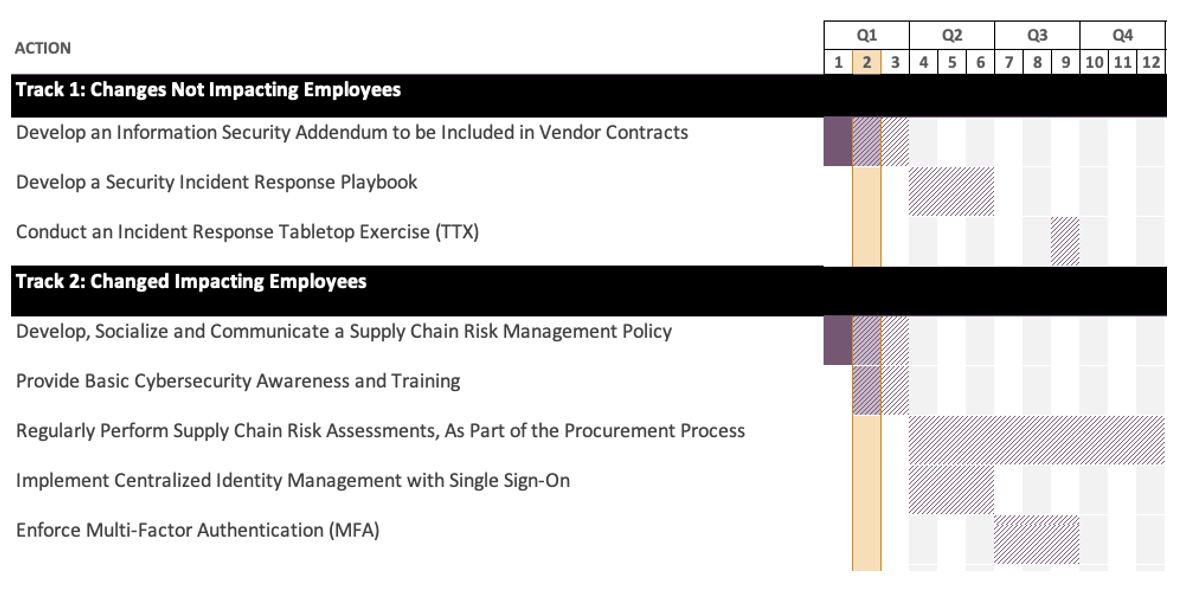
Roadmap of Prioritized Actions, Addressing the Top 5 Cyber Risks Identified in Phase One
Force Field Analysis

Stakeholder Analysis

Change Management

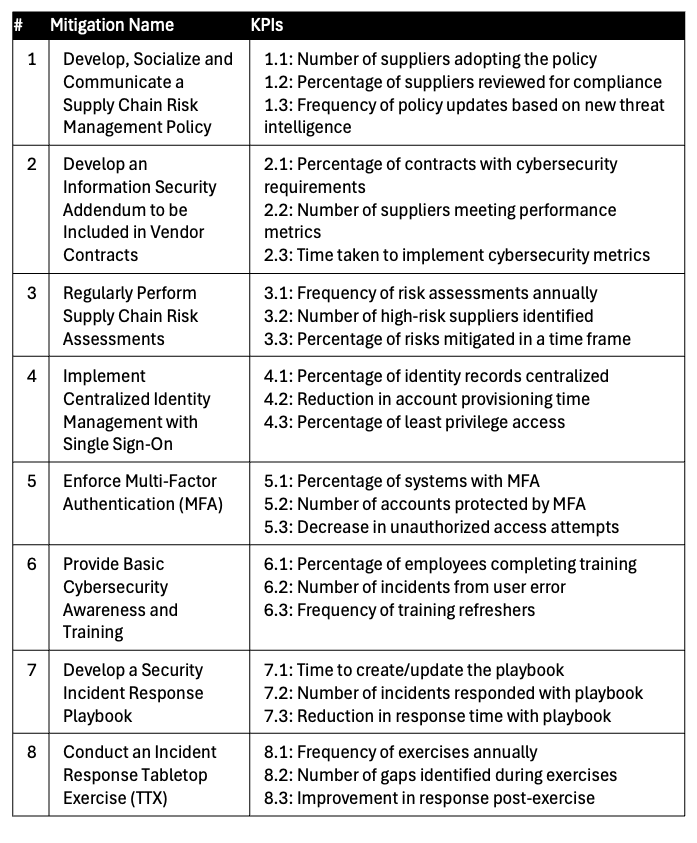
Key Performance Indicators
⚙ Phase Three: Maintenance and updates
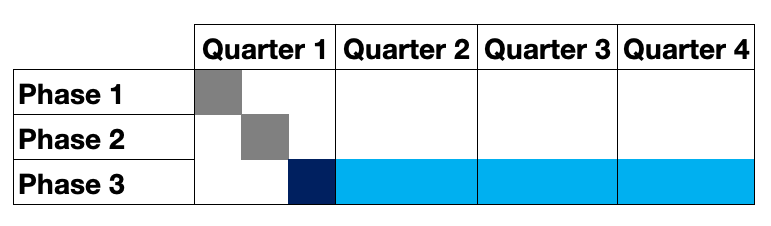
Duration:
10 months
When combined with phase one and phase two of the CR-MAP process, it completes the first-year cycle of the three-phase plan
Goals:
Maintain and continuously improve with monthly check-ins and comprehensive quarterly reviews to monitor progress
Bolster cyber resilience with a comprehensive approach, and by committing to ongoing vigilance
Opportunity to investigate and correct gaps or challenges to regain momentum
Acknowledge and celebrate achievements in managing cyber risks
🗓 The Thirteenth Month
📋The Five Questions
Once you have created your cyber risk management action plan, you should be able to confidently answer the following five questions:
🔝 What are the top five cyber risks to my organization?
💰Am I getting the biggest return possible for my cyber risk management dollars?
👔 Do all our organization’s executives and leaders understand our cybersecurity plans?
⚠ Does everyone at work know how they can help to mitigate our top cyber risks?
🗣 What do I tell our biggest customers or stakeholders when they ask, “What are you all doing about cybersecurity?”
Bottom-Line Perspective on CR MAP Value
Shifts the culture of your organization to achieving reasonable, cyber resilience - which is a big deal
“Culture eats strategy for breakfast” - Peter Drucker
Demonstrates due diligence and due care
Introduces repeatable cybersecurity practices - “Lather, Rinse, Repeat”
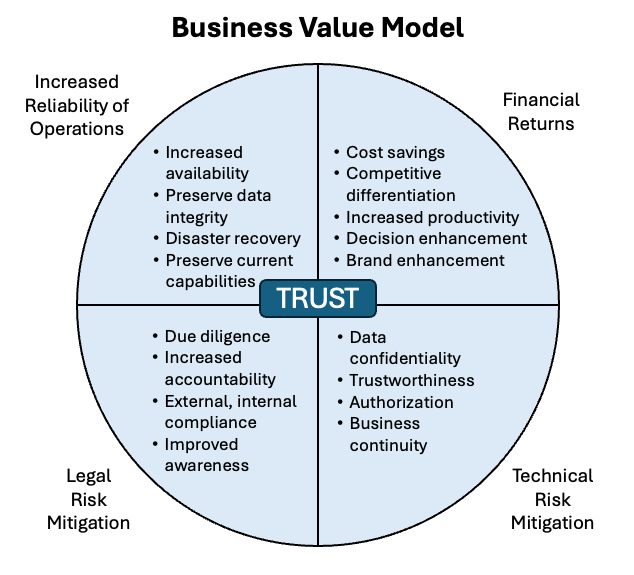
Prioritizes unlimited cyber risks (mission impossible), to optimize use of limited resources, and maximize 4 types of business value:
Increased reliability of operations
Legal risk mitigation
Technical risk mitigation
Financial returns
Answers “so what, what’s next?” for top cyber risks, with a right-sized, actionable, achievable, measurable implementation plan
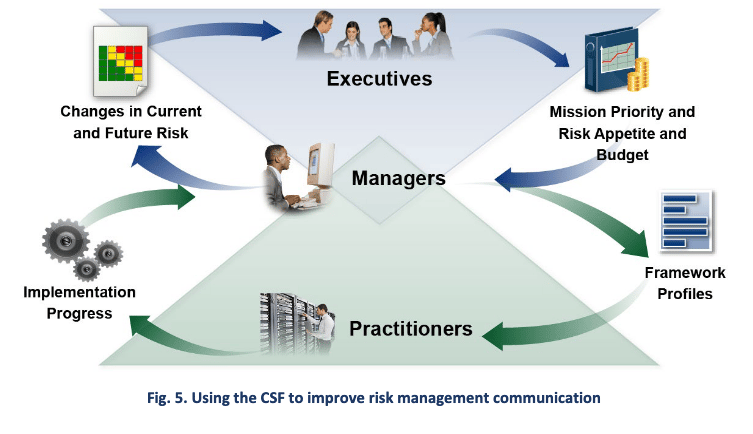
Enables effective risk management communication, up, down and across the organization, which is what CSF is all about
👥 Fostering Security Culture
🔒 Attorney-Client Privilege
Benefits
Retain control over your cyber risk records
Navigate any potential requests for a copy of those records
Disadvantages
⬆ costs
⬆ timeline to complete the work
✅ Conclusion and Touchpoints
CR-MAP: 3 Phases
First phase: focuses on discovering and assessing the top cyber risks faced by the organization
This phase involves prioritizing risks to allocate limited resources effectively
Second phase: involves creating a personalized cyber risk management action plan that addresses the top five risks identified in phase one
This plan considers various dimensions of business value and aims to mitigate risks while enhancing operational reliability and competitive advantage
Third phase: emphasizes the importance of maintaining, updating, and continuously improving the organization’s cybersecurity posture and risk management strategy
The 13th month 🗓 concept was introduced to emphasize the need for an ongoing and iterative approach to cyber risk management
Repeat the CR-MAP process annually
This repetition ensures continual improvement and adaptation to evolving cyber threats and the alignment of cyber risk management efforts with changing business dynamics.
Systematic approach
In summary, the CR-MAP process provides organizations with a structured and comprehensive framework to strengthen their cyber resilience.
By systematically identifying and managing cyber risks, organizations can proactively mitigate potential incidents, safeguard valuable assets, and sustain a competitive advantage in the modern digital landscape.
However, it is vital to emphasize the significance of perpetual vigilance, continuous improvement, and the ingrained integration of cybersecurity practices into the organization’s culture to effectively achieve these objectives.



